Hi @PARTH DESAI ,
Thank you for posting in Q&A!
In order to distinguish group membership for users establishing connections, we will Configure the network policy VSA attribute in NPS server. As most RADIUS servers including NPS will attempt to match authentication policies in top-down sequence, the rules are generally configured from most-specific/highest-privilege at the top and least-specific/lowest-privilege at the bottom.
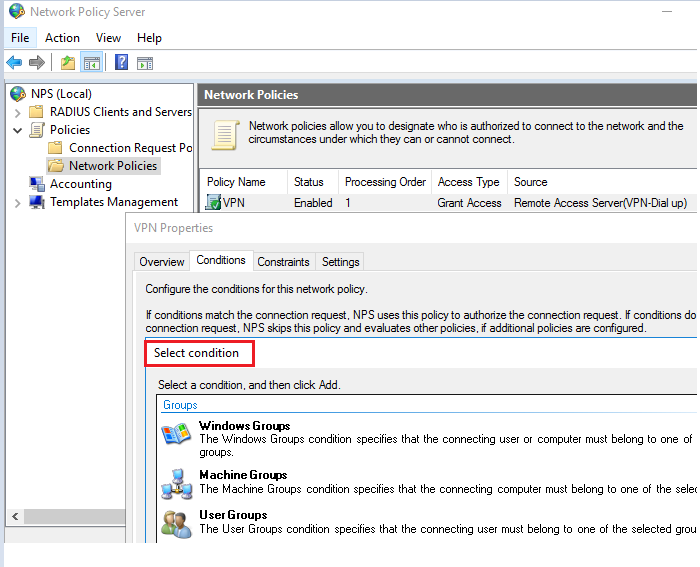
1.To configure a custom vendor-specific attribute:
Open the Network Policy Server console> Network Policies> Double-click the policy to which you want to add a custom VSA> Conditions> the specific group you want to apply.
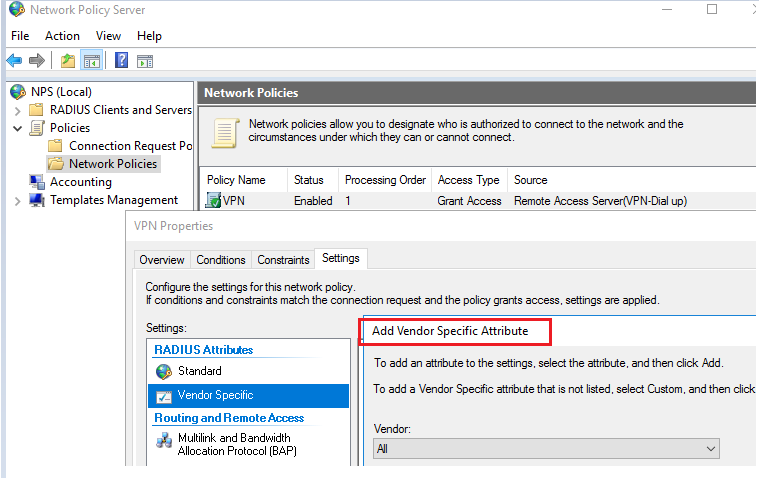
2.The Vendor-Specific Attribute Information dialog box opens. In Specify network access server vendor, choose an item in Select from list, or click Enter Vendor Code, and then type the vendor code supplied by your device manufacturer.
For more details, please refer to:
https://learn.microsoft.com/en-us/previous-versions/windows/it-pro/windows-server-2008-R2-and-2008/cc731611(v=ws.10)?redirectedfrom=MSDN
https://inside.fortinet.com/doku.php?id=sslvpn_with_radius_using_active_directory_and_nps
============================================
If the Answer is helpful, please click "Accept Answer" and upvote it.
Note: Please follow the steps in our documentation to enable e-mail notifications if you want to receive the related email notification for this thread.