Hi @Vikas Tiwari Please find my comments inline:
1) Repeated history length: User should not be allowed to repeat last 24 passwords while changing password.
As of now we do not support enforcing password history in B2C.
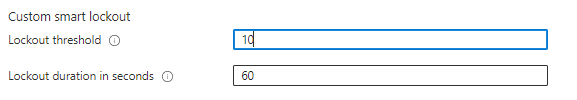
2) Account Lockout: After 3 consecutive failed login attempts within 60 minutes, user account should be locked for "N" hours.
This can be configured via Azure AD B2C > Authentication Methods > Password Protection.
3) If an account is not accessed for 90 consecutive days, the account shall be disabled on 91st day and will be delete after 120 days of inactivity.
To disable the account after 90 days of inactivity, you can refer to this sample: Disable and lockout an account after a time period. For deleting the accounts, you can create a PowerShell Script that checks **exentsion_lastLogonTime attribute and delete accounts where the value is >120 days.**
4) Increment previous passwords should not be allowed while changing password : If last password was P@$$WORD123 next password can not be P@$$WORD124, 125, 126 etc up to 10 increments.
This is not supported. Best you can do is, Enforce Banned password list via Azure AD B2C > Authentication Methods > Password Protection.
5) Customize audit message when user enters wrong userid or password as "The User Id or Password that you have entered is not correct".
You can use below localization string IDs for this purpose. Refer to https://learn.microsoft.com/en-us/azure/active-directory-b2c/localization-string-ids for more details,
<LocalizedString ElementType="ErrorMessage" StringId="UserMessageIfClaimsPrincipalDoesNotExist">The User Id or Password that you have entered is not correct.</LocalizedString>
<LocalizedString ElementType="ErrorMessage" StringId="UserMessageIfInvalidPassword">The User Id or Password that you have entered is not correct.</LocalizedString>
Please "Accept the answer" if the information helped you. This will help us and others in the community as well.