Hello @김 우준 ,
Thanks for reaching out.
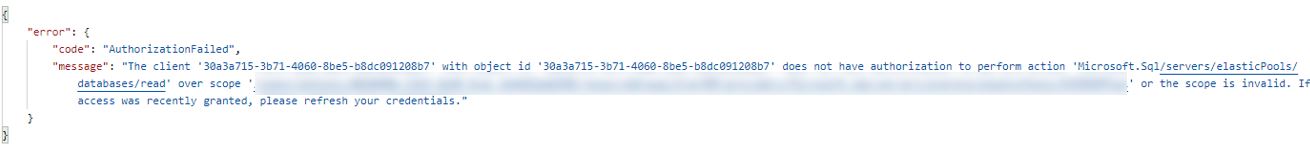
It seem to be the service principal that you are using doesn't have appropriate rights at your subscription level to perform action.
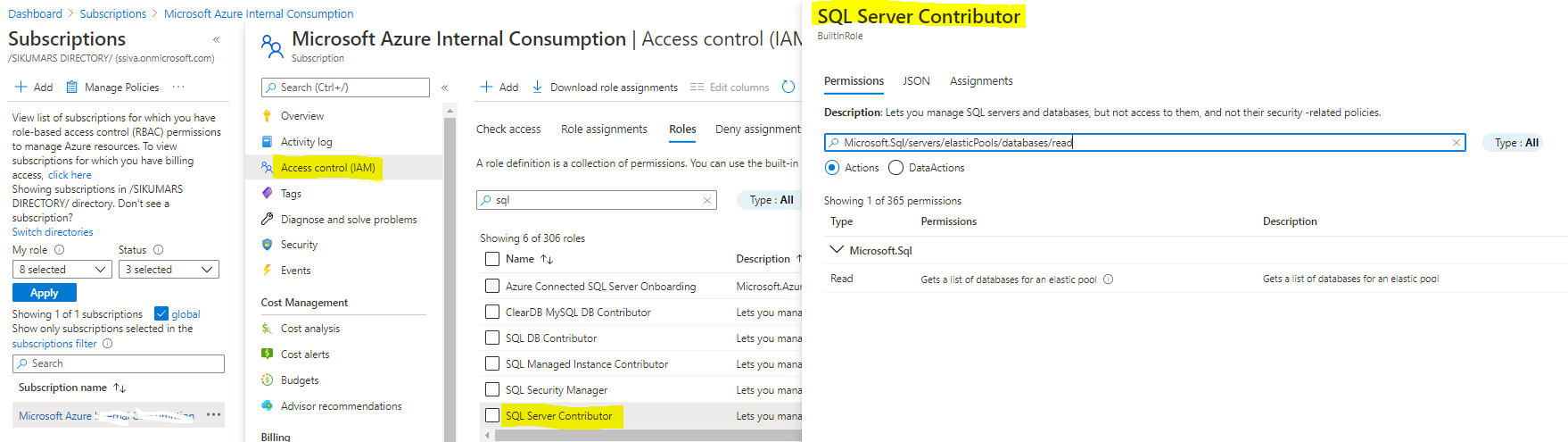
To fix the issue, assign any of below RBAC build role which has access to perform action at Microsoft.Sql/servers/elasticPools/databases/read by using either Portal or PowerShell as explained here and try getting new set of Azure AD token which should work.
These build-In role contains read action for SQL elastic Pools SQL Server Contributor OR Contributor OR Owner
Example:
You can also verify this by going to subscription blade and selecting each build-in RBAC role to validate as shown below:
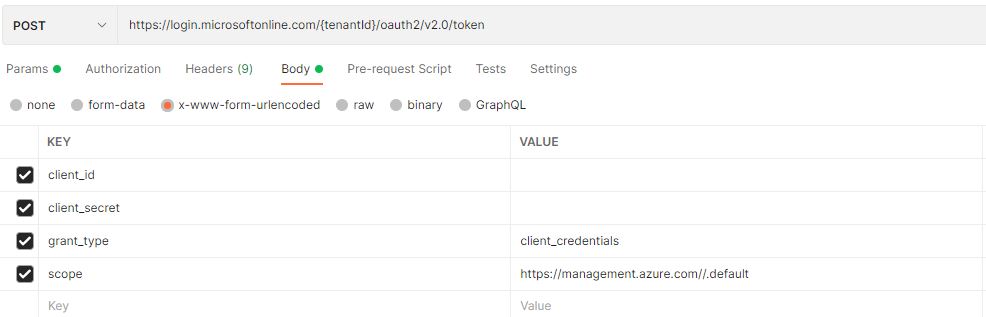
Therefore, you don't have to set any additional scope value other than https://management.azure.com/.default in parameter which you are already passing it while getting acces_token so all you need to assign RBAC (Role Based Access Control) role for a given principal to perform action 'Microsoft.Sql/servers/elasticPools/databases/read' over your subscription as explained above .
Hope this helps.
------
Please "Accept the answer" if the information helped you. This will help us and others in the community as well.