The issue was indeed, not using the .p12/pfx file. However, issues will also arise should some of the settings clash between the rootCA and subordinateCA, e.g Provider information. Hope you guys will be able to release the entire list of default configuration on this.
Create CSR file when installing Certificate Authority
If done via the GUI, there is an option to generate a csr request file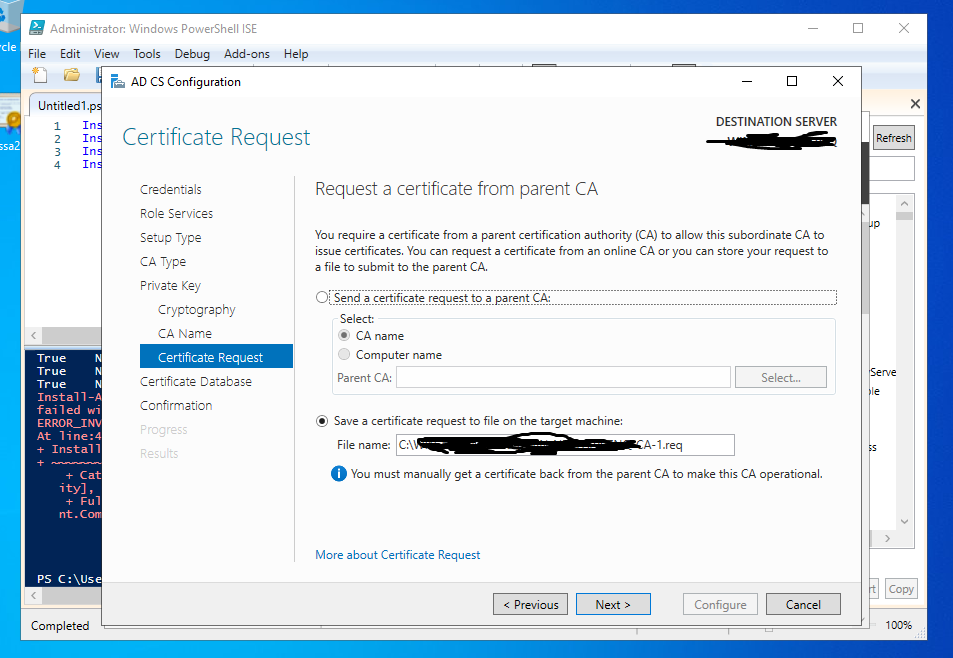
However, when I try to install the certificate Authority via Powershell, there is no such option.
https://learn.microsoft.com/en-us/powershell/module/adcsdeployment/install-adcscertificationauthority?view=windowsserver2019-ps
I resorted to using certreq -new to generate a new .req file from the following .inf file:
[newrequest]
Subject = "CN=mySubCA"
HashAlgorithm = sha256
, but when installing it via Powershell command (after approving and exporting it from Root CA)
Install-AdcsCertificationAuthority -CAType StandaloneSubordinateCA -CertFile C:\Users\Administrator\Desktop\cert.p7b , the following error is given: The data is invalid. 0x8007000d (WIN32: 13
ERROR_INVALID_DATA).
I'd like to know 1) Is it possible to create the p7b file before creating the Certificate Authority?
2) Is it possible to generate the csr request from Powershell alone?
2 additional answers
Sort by: Most helpful
-
 Limitless Technology 39,391 Reputation points
Limitless Technology 39,391 Reputation points2021-10-20T13:38:52.293+00:00 Hello @Jie wei
I would recommend to check the next potential scenarios that usually lead to this error:
a) You copied the wrong CSR to the root CA and submitted it
b) You created the new CSR properly, copied it to the root CA but accidentally submitted the original CSR
c) You successfully submitted the new CSR, but accidently exported the old version of the CA certificate.
About your questions:
- You will need the CA first
- May need a bit of tweak depending in the Certification Authority, but normally I am using the next script (as example): Write-Host "Creating CertificateRequest(CSR) for $CertName
r " Invoke-Command -ComputerName testbox -ScriptBlock { $CertName = "newcert.contoso.com" $CSRPath = "c:\temp\$($CertName)_.csr" $INFPath = "c:\temp\$($CertName)_.inf" $Signature = '$Windows NT$' $INF = @" [Version] Signature= "$Signature" [NewRequest] Subject = "CN=$CertName, OU=Contoso East Division, O=Contoso Inc, L=Boston, S=Massachusetts, C=US" KeySpec = 1 KeyLength = 2048 Exportable = TRUE MachineKeySet = TRUE SMIME = False PrivateKeyArchive = FALSE UserProtected = FALSE UseExistingKeySet = FALSE ProviderName = "Microsoft RSA SChannel Cryptographic Provider" ProviderType = 12 RequestType = PKCS10 KeyUsage = 0xa0 [EnhancedKeyUsageExtension] OID=1.3.6.1.5.5.7.3.1 "@ write-Host "Certificate Request is being generatedr "
$INF | out-file -filepath $INFPath -force
certreq -new $INFPath $CSRPath
}
write-output "Certificate Request has been generated"
Hope this helps with your query,
--If the reply is helpful, please Upvote and Accept as answer--
-
Jie wei 116 Reputation points
2021-10-21T06:03:12.967+00:00 Thanks for the reply, however, I believe the error lies in using a .p7b file instead of a .p12 file, which contains the private key information while a p7b file does not, as above code does not work as well.
As part of the question however, given a .cer file obtained from the root CA, how do we obtain the private keys of the certificate signing request (csr) generated previously such that we can create the p12 file to use?
Do let me know if I'm correct