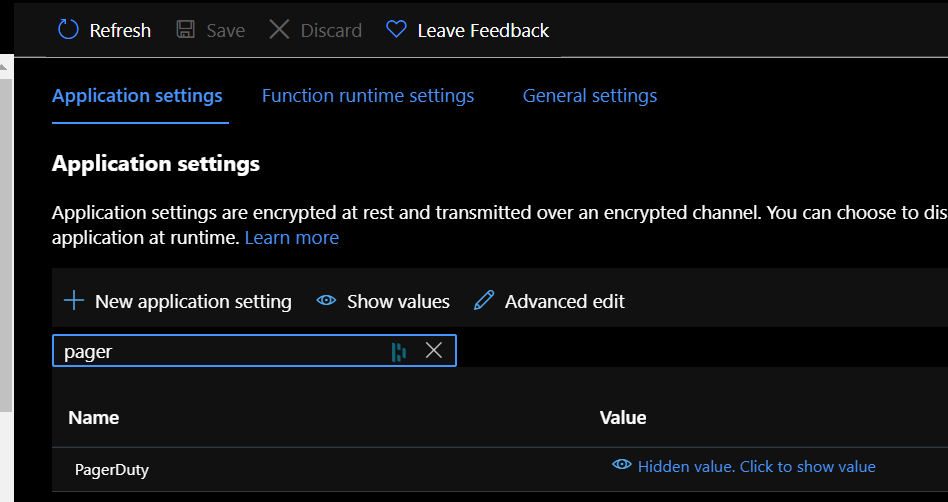
@Dave Gray App settings and connection strings are stored encrypted in Azure. They're decrypted only before being injected into your app's process memory when the app starts. The encryption keys are rotated regularly. If you prefer to instead manage the secure storage of your secrets like you mentioned SQL DB connection string, the app setting should instead be references to Azure Key Vault rather than hardcoding the connection string like scenarios where your team may have access only to function app and you don't want them to view the connection strings that are used in application or any of the other use case.
While application settings are sufficient for most many functions, you may want to share the same secrets across multiple services. In this case, redundant storage of secrets results in more potential vulnerabilities. A more secure approach is to a central secret storage service and use references to this service instead of the secrets themselves then in that case Azure Key Vault is a service you can leverage as centralized secrets management, with full control over access policies and audit history. You can use a Key Vault reference in the place of a connection string or key in your application settings. To learn more, see Use Key Vault references for App Service and Azure Functions.