Hello @Somansh Reddy
API Permissions: You should configure API Permissions when you would like to return the permissions in the Access token. When application consumes the token, it makes authorization decision on the basis of permissions present in the token. Delegated permissions are used when authentication is done under user's context and are returned in scope claim of the token. Application permissions are used when authentication is done under application (service principal) context and are returned in roles claim. For example, if you have a web application, you can configure it to allow access to the user if scope claim contains read otherwise deny access or grant write access to application only when roles claim contains write.
Role Assignments: Role assignments are used to assign permission to users/service principals on Azure Resources. In this case authorization is done by Azure and not by the end application which happens in case of API permissions.
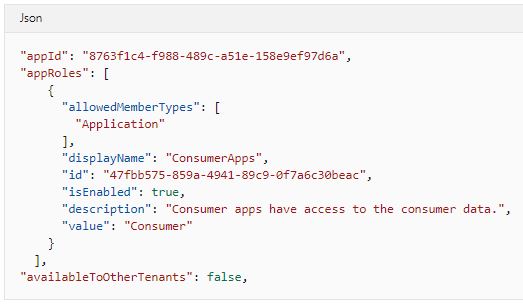
To configure application permissions, app roles must be added to app manifest as shown below:
However, Azure Storage API is exposed on an app registered in Microsoft tenant and you cannot configure the application permissions by updating app manifest. Which is why the application permissions are not available for Azure Storage API. You can however configure permission via Role Assignment to application (service principals) over Azure Storage.
You can configure both permissions simultaneously as these permissions are evaluated at different places (as mentioned above) and one doesn't override the other.
-----------------------------------------------------------------------------------------------------------
Please "Accept the answer" if the information helped you. This will help us and others in the community as well.
