So, just by
az ad sp create --id <B2C_APP_CLIENT_ID> somehow it finds the info for the app in the B2C tenant and adds its presence in the main tenant. The rest I did manually.
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
In my org, we have our main tenant and a B2C tenant. There are apps that live in the main tenant (mostly for internal use) and some for external customers that live in the B2C tenant. In the past, I was able to register apps from the main tenant into the B2C tenant (then a new enterprise application would appear) using the admin consent flow. What I did was
https://login.microsoftonline.com/<B2C_TENANT_ID>/v2.0/adminconsent?client_id=<MAIN_ORG_APP_ID>&<MAIN_ORG_APP_SCOPE>
However, when trying to do the opposite, add a presence for a B2C app registration in the main tenant, I get prompted the admin consent confirmation, I accept it, but no enterprise application gets added to my main tenant.
Example of what I am using to trying achieve it
https://login.microsoftonline.com/<MAIN_TENANT_ID>/v2.0/adminconsent?client_id=<B2C_APP_CLIENT_ID>&<B2C_APP_SCOPE>
Example prompt consent. (Everything looks correct)
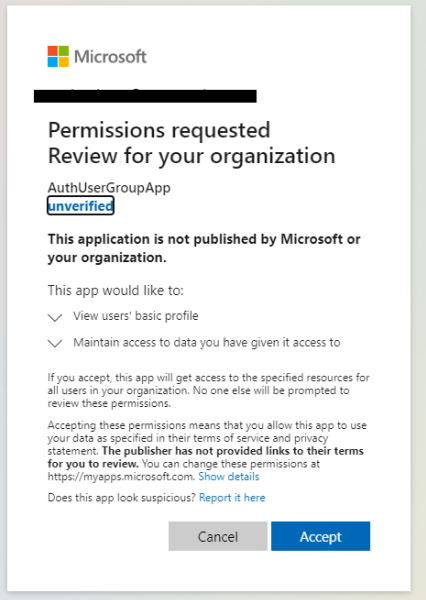
My B2C app is multi-tenant, but its presence won't get added to the main catalog of apps in the organization tenant.
So, just by
az ad sp create --id <B2C_APP_CLIENT_ID> somehow it finds the info for the app in the B2C tenant and adds its presence in the main tenant. The rest I did manually.

@Paul Stevenson • Thank you for reaching out.
I don't see any issues and ideally it should work. I tested this with my B2C and AAD tenants and it worked for me.
Can you give it a try using the V1 endpoint, as mentioned below:
https://login.microsoftonline.com/<MAIN_TENANT_ID>/adminconsent?client_id=<B2C_APP_CLIENT_ID>
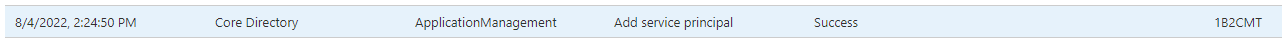
Check the Azure AD > Audit logs to see if there was an attempt to create a servicePrincipal and if the attempt was success or not, as shown below:
Also, double-check the filters under the Enterprise Apps blade of the main tenant to ensure it is not hidden due to filter conditions.
-----------------------------------------------------------------------------------------------------------
Please "Accept the answer" if the information helped you. This will help us and others in the community as well.
Appreciate your response @AmanpreetSingh-MSFT . Under my API app registration (in the b2c), I see no "Authorized Client Applications" in "Expose an API".
The documentation for knownClientApplications says
"Used for bundling consent if you have a solution that contains two parts: a client app and a custom web API app. If you enter the appID of the client app into this value, the user will only have to consent once to the client app. Azure AD will know that consenting to the client means implicitly consenting to the web API. It will automatically provision service principals for both the client and web API at the same time. Both the client and the web API app must be registered in the same tenant."
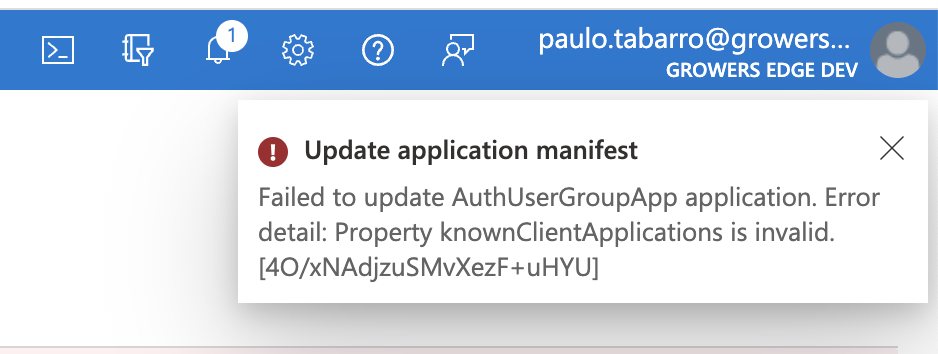
If I try to add the application Id of my client in the manifest directly, it gives an error (probably because the application Id doesn't exist in the B2C tenant):
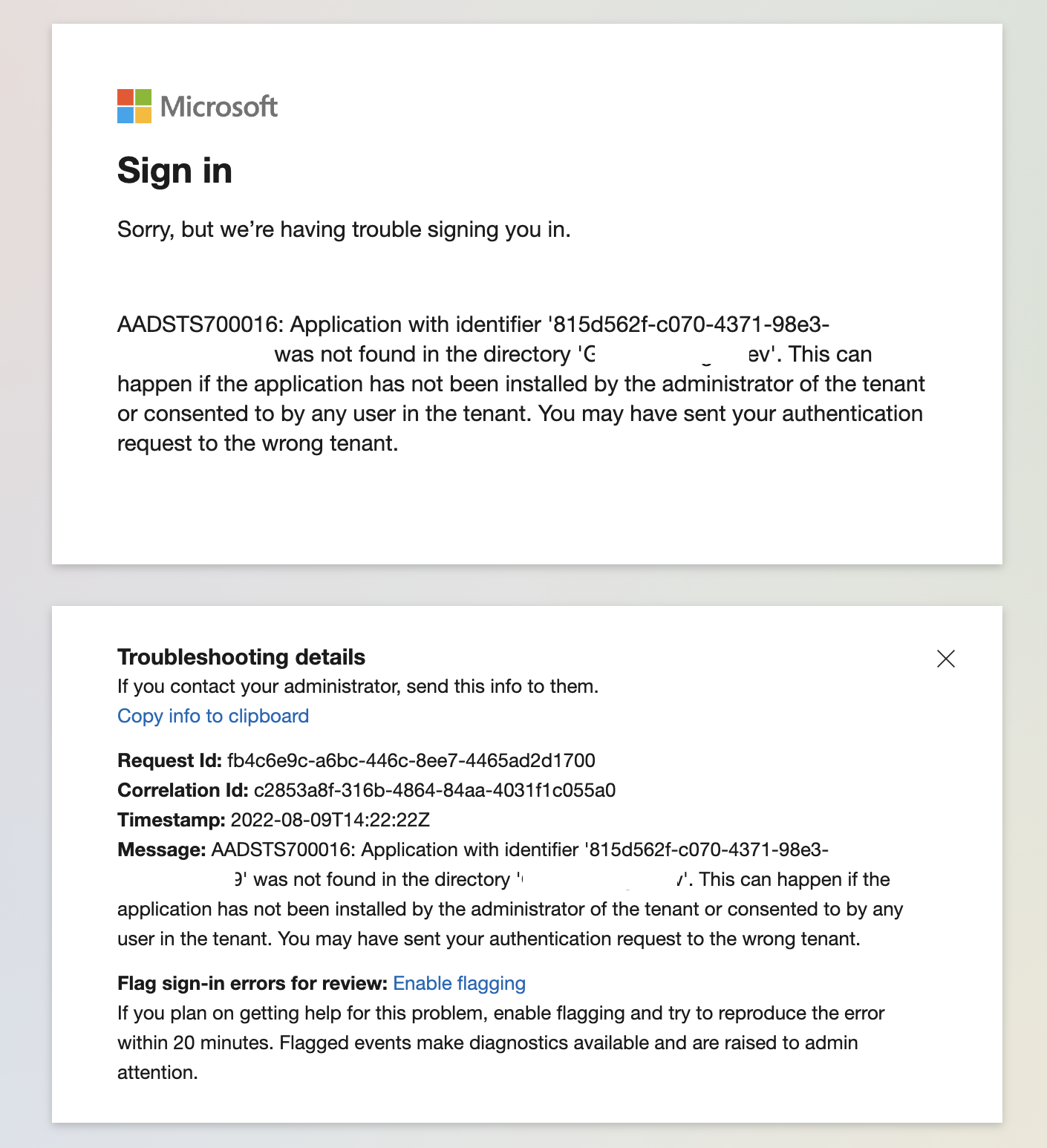
and finally, if I try to /adminconsent my client app in the B2C tenant (I'd have to use adminconsent v1 because v2 requires a scope, which my frontend client doesn't have). It yields: