Setting up Kerberos with a Client Access Server Array Exchange 2010 SP1
By default, clients that attempt to negotiate authentication will fail Kerberos authentication when a CAS array is configured thus falling back to NTLM. The reason Kerberos authentication fails is because the authentication request is sent using the FQDN of the CAS array which does not match the SPN value on the CAS servers. To address this issue we must create an appropriate SPN value for the CAS array within Active Directory. We also cannot configure the same SPN value on multiple objects in Active Directory. To work around this we created a method called Alternate Service Account (ASA). The ASA can be either a computer account or user account. Then we can associate the SPNs we want for the CAS array to the ASA.
Note. We can use one ASA for all CAS arrays or make an ASA for each CAS array.
Creating the alternate service account (ASA)
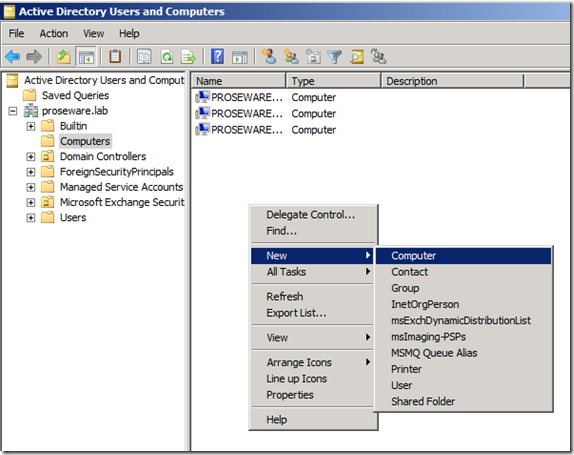
Open Active Directory Users and Computers and create the ASA. In this example we will create a computer account.
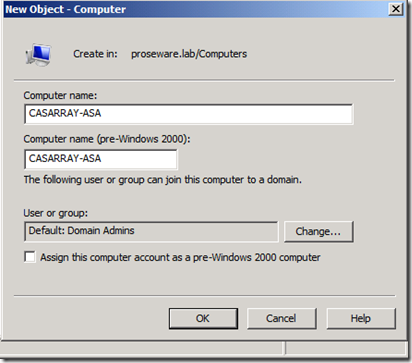
The account name does not matter as long is its valid but consider making the name self explanatory.
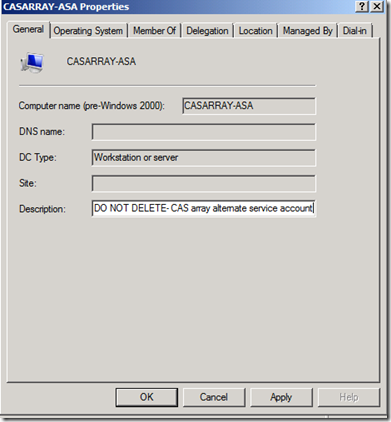
Fill in a description. (This is not required but should to prevent some-one from deleting the account)
Setting the correct SPNs to the ASA
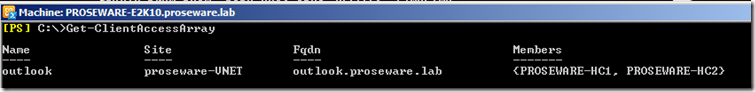
Confirm the FQDN of the CAS array with the following command in Exchange Management Shell.
Now we need to set the SPNs of the CAS array Autodiscover and EWS. Some MAPI applications that interact with Exchange may need to use the Array’s short name or NetBIOS. We will set NetBIOS and FQDN for each SPN.
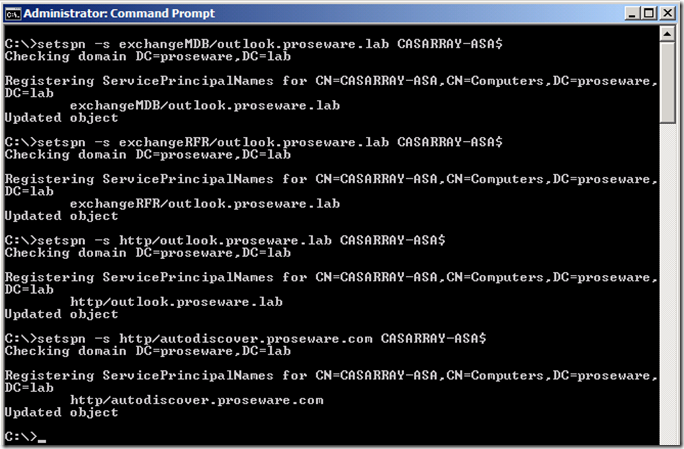
In this example the commands will be as follows. (If a computer account is being used, a $ must be after the name you have assigned.)
setspn -s exchangeMDB/outlook CASARRAY-ASA$
setspn -s exchangeRFR/outlook CASARRAY-ASA$
setspn -s exchangeAB/outlook CASARRAY-ASA$
setspn -s exchangeMDB/outlook.proseware.lab CASARRAY-ASA$
setspn -s exchangeRFR/outlook.proseware.lab CASARRAY-ASA$
setspn -s exchangeAB/outlook.proseware.lab CASARRAY-ASA$
setspn -s http/outlook.proseware.lab CASARRAY-ASA$
setspn -s http/autodiscover.proseware.com CASARRAY-ASA$
Note. At this point new authentication attempts to the above DNS names will fail until the ASA is assigned to the CAS servers.At this point we could back out by simply running the following command for each SPN. setspn –d {spn} {account}
Setting the ASA to the CAS servers
From here we will want to assign the ASA to our CAS servers so that clients can start authenticating to the CAS array.
Go to the Scripts directory located in the Exchange install directory (by default it is C:\Program Files\Microsoft\Exchange Server\V14\Scripts\)
Run the following command in Exchange Management Shell.
.\RollAlternateserviceAccountPassword.ps1 –ToArrayMembers {CAS array name}-GenerateNewPasswordFor {Domain}\{ASA}" –Verbose

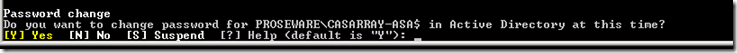
The script will ask if we want to change the password on the ASA.In this case we will say Yes.
The final output will tell us if we succeeded or failed on any part of the script. 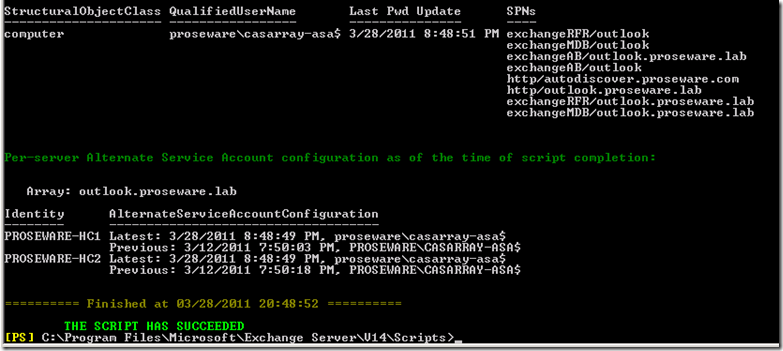
Confirm that CAS is accepting Kerberos
Now we want to verify that the CAS servers can accept Kerberos requests.
Check in the Address book logs to see if the authentication method is set to Kerberos. (Default location is C:\Program Files\Microsoft\Exchange server\v14\Logging\AddressBook Service)
2011-03-11T20:00:12.000Z,9,0,/o=First Organization/ou=Exchange Administrative Group (FYDIBOHF23SPDLT)/cn=Recipients/cn=Administrator,,192.168.0.123,proseware-hc1,ncacn_ip_tcp,Bind,,6,,,Kerberos,
OR
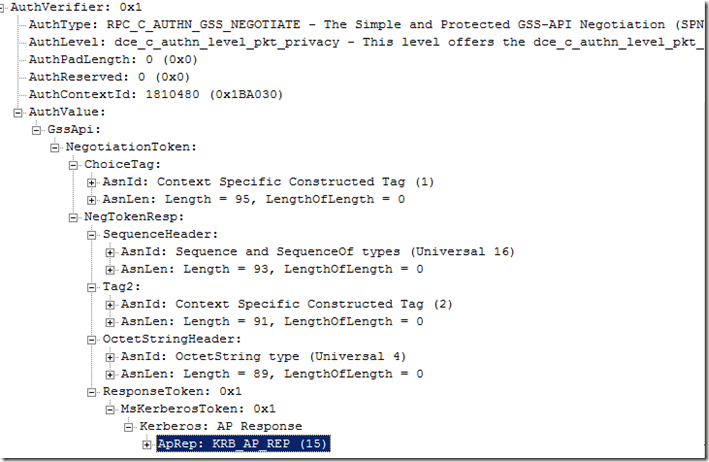
Since this blog is geared to exchange and networking. Take a netmon and look to see if we are using a Kerberos Token.
Side notes
If you ever add an additional node to the CAS array you can use the following command to copy the ASA credentials over to the new server without changing the password on the ASA.
.\RollAlternateServiceAccountPassword.ps1 -CopyFrom ServerA -ToSpecificServers ServerB –Verbose
To find the CAS servers that have been configured with an ASA run the following command.
Get-ClientAccessServer -IncludeAlternateServiceAccountCredentialstatus |Fl Name, AlternateServiceAccountConfiguration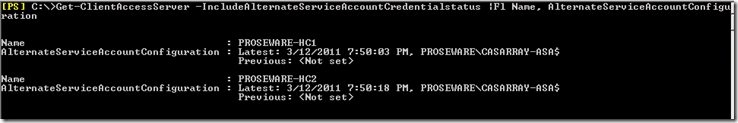
Related Articles
Configuring Kerberos Authentication for Load-Balanced Client Access Servers
Using Kerberos with a Client Access Server Array or a Load-Balancing Solution
Using the RollAlternateserviceAccountCredential.ps1 Script in the Shell