Visit the Microsoft Defender portal
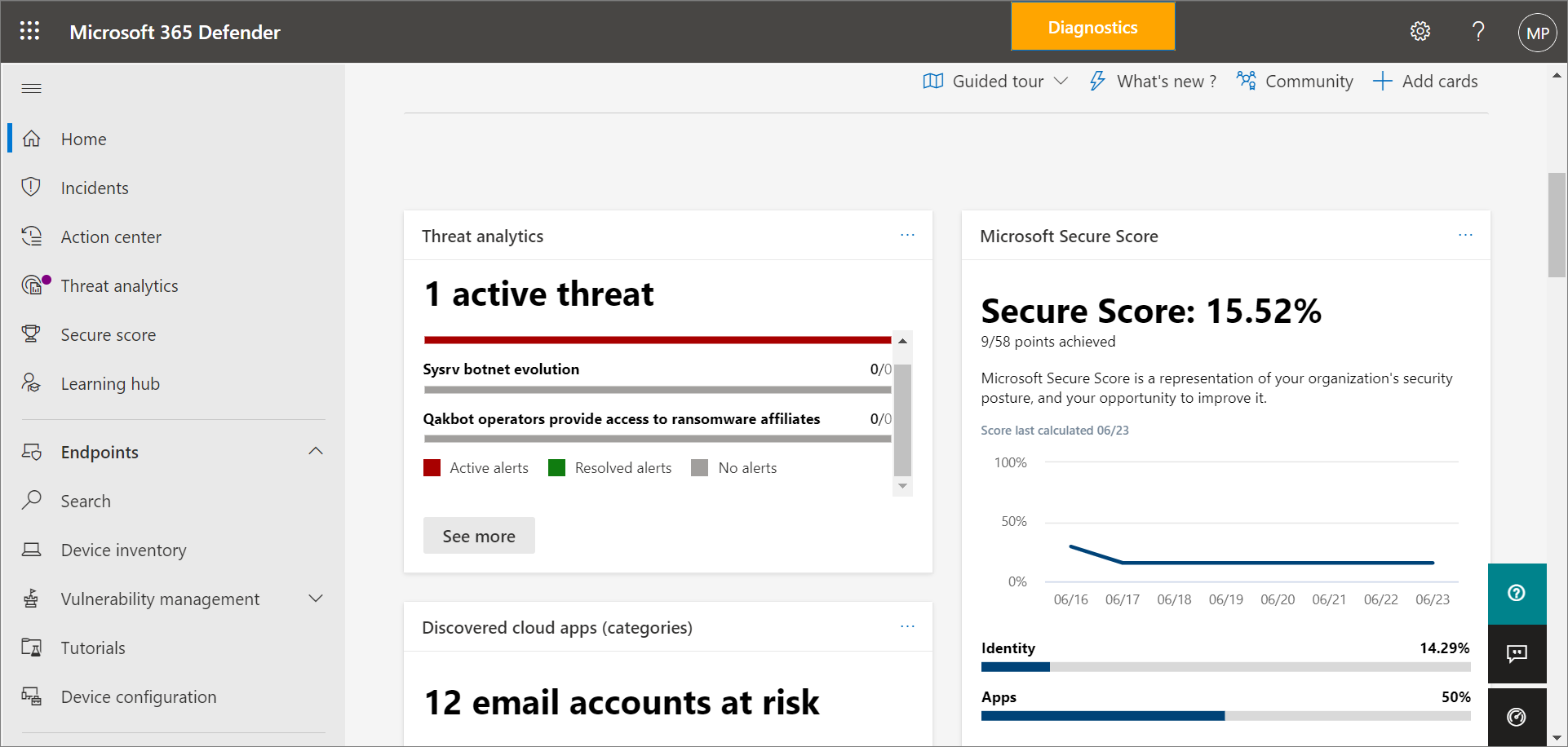
The Microsoft Defender portal (https://security.microsoft.com) is your one-stop shop for using and managing Microsoft Defender for Business. It includes callouts to help you get started, cards that surface relevant information, and a navigation bar to give you easy access to various features and capabilities.
The navigation bar
Use the navigation bar on the left side of the screen to access your incidents, view reports, and manage your security policies. The following table describes items you'll see in your navigation bar.
| Item | Description |
|---|---|
| Home | Takes you to your home page in the Microsoft Defender portal. The home page highlights any active threats that are detected, along with recommendations to help secure your company's data and devices. Recommendations are included in Defender for Business to save your security team time and effort. The recommendations are based on industry best practices. To learn more, see Security recommendations - Microsoft Defender Vulnerability Management. |
| Incidents & alerts > Incidents | Takes you to your list of recent incidents. As alerts are triggered, incidents are created. An incident can include multiple alerts. Make sure to review your incidents regularly. To learn more, see View and manage incidents in Defender for Business. |
| Actions & submissions > Action center | Takes you to your list of response actions, including completed and pending actions. - Select the Pending tab to view actions that require approval to proceed. - Select the History tab to see the actions that were taken. Some actions are taken automatically; others are taken manually or complete after they're approved. To learn more, see Review remediation actions in the Action center. |
| Actions & submissions > Submissions | Takes you to the unified submissions portal, where you can submit files to Microsoft for analysis. To learn more, see Submit files in Microsoft Defender for Endpoint (the process is similar for Defender for Business). |
| Secure score | Provides a representation of your company's security position and offers suggestions to improve it. To learn more, see Microsoft Secure Score for Devices. |
| Learning hub | Provides access to security training and other resources through learning paths that are included with your subscription. You can filter by product, skill level, role, and more. The Learning hub can help your security team ramp up on security features and capabilities in Defender for Business and more Microsoft offerings, such as Microsoft Defender for Endpoint and Microsoft Defender for Office 365. |
| Trials | Try additional security and compliance capabilities by adding on a trial subscription. If you do not see Trials in your navigation bar, and you want to add on another trial, you can take one of the following steps: - Visit the Small Business Solutions page, and choose Questions? Talk to an expert to get some help adding on a trial subscription. - Go to the Microsoft 365 admin center, and choose Billing > Purchase services. If you need help, choose Help & support. |
| Partner catalog | Lists Microsoft partners who provide technical and professional services. |
| Assets > Devices | Enables you to view devices, such as computers and mobile devices that are enrolled in Microsoft Intune. |
| Endpoints > Vulnerability management | Enables you to access your Microsoft Defender Vulnerability Management capabilities. Provides a dashboard, recommendations, remediation activities, a software inventory, and a list of potential weaknesses within your company. |
| Endpoints > Tutorials | Provides access to walkthroughs and simulations to help you learn more about how your threat protection features work. Select the Read the walkthrough link before attempting to get the simulation file for each tutorial. Some simulations require Office apps, such as Microsoft Word, to read the walkthrough. |
| Endpoints > Configuration management > Device configuration | Lists your security policies by operating system and by type. To learn more about your security policies, see View or edit policies in Defender for Business. |
| Endpoints > Configuration management > Device management reporting | Lists devices that are onboarded to Defender for Business, along with their operating system version, sensor health state, and when they were last updated. |
| Email & collaboration > Policies & rules | If your subscription includes Exchange Online Protection or Microsoft Defender for Office 365, this section is where you'll manage your security policies and settings for email and collaboration services. Learn more about Office 365 security. The standalone version of Defender for Business does not include email & collaboration policies, but Microsoft 365 Business Premium does include Exchange Online Protection and Defender for Office 365 Plan 1. |
| Cloud apps > App governance | If your subscription includes Microsoft Defender for Cloud Apps, you can add on app governance, and this section is where you'll view and access those capabilities. Defender for Business and Microsoft 365 Business Premium do not include Defender for Cloud Apps. |
| Reports | Lists available security reports. These reports enable you to see your security trends, view details about threat detections and alerts, and learn more about your company's vulnerable devices. |
| Health | Enables you to view your service health status and plan for upcoming changes. - Select Service health to view the health status of the Microsoft 365 services that are included in your company's subscription. - Select Message center to learn about planned changes and what to expect. |
| Permissions | Enables you to assign permissions to the people in your company who manage your security and to view incidents and reports in the Microsoft Defender portal. Also enables you to set up and manage device groups to onboard your company's devices and assign threat protection policies. |
| Settings | Enables you to edit settings for the Microsoft Defender portal and Defender for Business. For example, you can onboard (or offboard) your company's devices (also referred to as endpoints). You can also define rules, such as alert-suppression rules, and set up indicators to block or allow certain files or processes. |
| More resources | Navigate to other portals, such as Microsoft Entra ID. But keep in mind that the Microsoft Defender portal should meet your needs without requiring you to navigate to other portals. |
| Customize your navigation pane | Select this option to hide or display options in your navigation bar. |
Next steps
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for