Use Preservation Lock to restrict changes to retention policies and retention label policies
Important
Currently, adaptive policy scopes don't support Preservation Lock.
Preservation Lock locks a retention policy or retention label policy so that no one—including a global admin—can turn off the policy, delete the policy, or make it less restrictive. This configuration might be needed for regulatory requirements and can help safeguard against rogue administrators.
When a retention policy is locked:
- No one can disable the policy or delete it
- Locations can be added but not removed
- You can extend the retention period but not decrease it
When a retention label policy is locked:
- No one can disable the policy or delete it
- Locations can be added but not removed
- Labels can be added but not removed
In summary, a locked policy can be increased or extended, but it can't be reduced or turned off.
Important
Before you lock a retention policy or retention label policy, it's critical that you understand the impact and confirm whether it's required for your organization. For example, it might be needed to meet regulatory requirements. Administrators won't be able to disable or delete these policies after the preservation lock is applied.
Configure Preservation Lock after you've created a retention policy, or a retention label policy that you publish and contains only labels that mark items as regulatory records.
Tip
If you're not an E5 customer, use the 90-day Microsoft Purview solutions trial to explore how additional Purview capabilities can help your organization manage data security and compliance needs. Start now at the Microsoft Purview compliance portal trials hub. Learn details about signing up and trial terms.
How to lock a retention policy or retention label policy
You must use PowerShell if you need to use Preservation Lock. Because administrators can't disable or delete a policy for retention after this lock is applied, enabling this feature is not available in the UI to safeguard against accidental configuration.
All retention policies with any configuration support Preservation Lock. To apply Preservation Lock on a retention label policy, it must contain only labels that mark items as regulatory records.
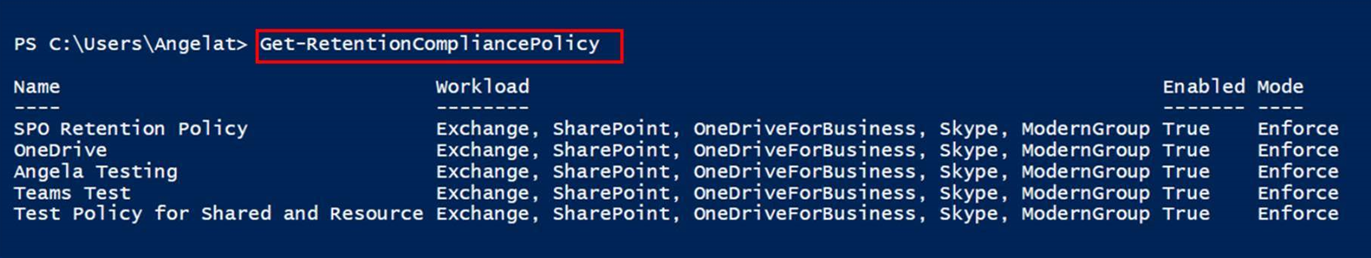
Find the name of the policy that you want to lock by running Get-RetentionCompliancePolicy. For example:
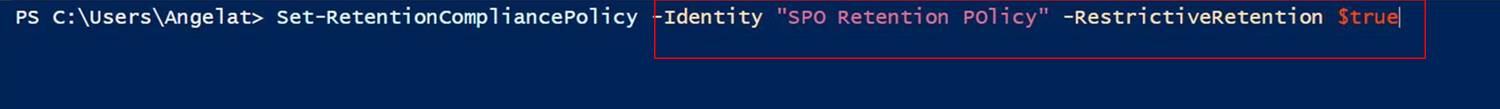
To place a Preservation Lock on your policy, run the Set-RetentionCompliancePolicy cmdlet with the name of the policy, and the RestrictiveRetention parameter set to true:
Set-RetentionCompliancePolicy -Identity "<Name of Policy>" -RestrictiveRetention $trueFor example:
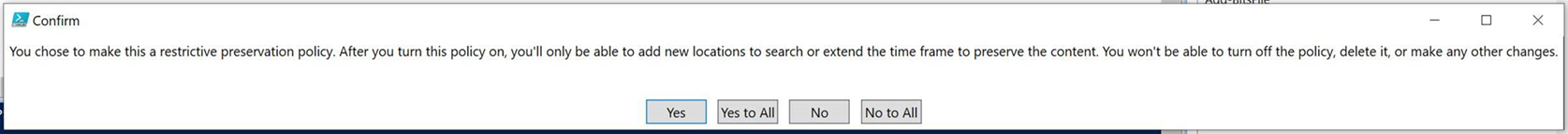
When prompted, read and acknowledge the restrictions that come with this configuration by entering Y:
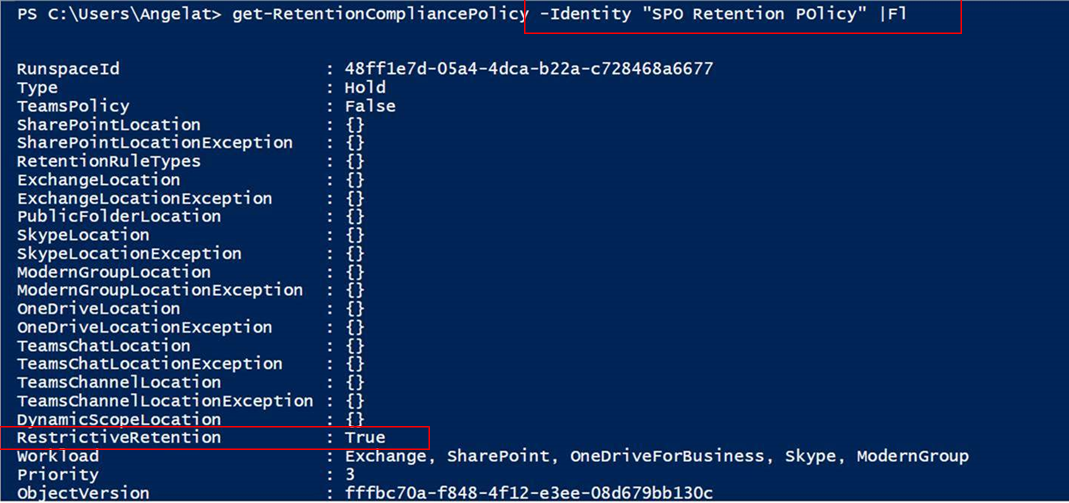
A Preservation Lock is now placed on the policy. To confirm, run Get-RetentionCompliancePolicy again, but specify the policy name and display the policy parameters:
Get-RetentionCompliancePolicy -Identity "<Name of Policy>" |Fl
You should see RestrictiveRetention is set to True. For example:
See also
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for