Tutorial: Configure SAP SuccessFactors to Microsoft Entra user provisioning
The objective of this tutorial is to show the steps you need to perform to provision worker data from SuccessFactors Employee Central into Microsoft Entra ID, with optional write-back of email address to SuccessFactors.
Note
Use this tutorial if the users you want to provision from SuccessFactors are cloud-only users who don't need an on-premises AD account. If the users require only on-premises AD account or both AD and Microsoft Entra account, then please refer to the tutorial on configure SAP SuccessFactors to Active Directory user provisioning.
The following video provides a quick overview of the steps involved when planning your provisioning integration with SAP SuccessFactors.
Overview
The Microsoft Entra user provisioning service integrates with the SuccessFactors Employee Central in order to manage the identity life cycle of users.
The SuccessFactors user provisioning workflows supported by the Microsoft Entra user provisioning service enable automation of the following human resources and identity lifecycle management scenarios:
Hiring new employees - When a new employee is added to SuccessFactors, a user account is automatically created in Microsoft Entra ID and optionally Microsoft 365 and other SaaS applications supported by Microsoft Entra ID, with write-back of the email address to SuccessFactors.
Employee attribute and profile updates - When an employee record is updated in SuccessFactors (such as their name, title, or manager), their user account will be automatically updated Microsoft Entra ID and optionally Microsoft 365 and other SaaS applications supported by Microsoft Entra ID.
Employee terminations - When an employee is terminated in SuccessFactors, their user account is automatically disabled in Microsoft Entra ID and optionally Microsoft 365 and other SaaS applications supported by Microsoft Entra ID.
Employee rehires - When an employee is rehired in SuccessFactors, their old account can be automatically reactivated or re-provisioned (depending on your preference) to Microsoft Entra ID and optionally Microsoft 365 and other SaaS applications supported by Microsoft Entra ID.
Who is this user provisioning solution best suited for?
This SuccessFactors to Microsoft Entra user provisioning solution is ideally suited for:
Organizations that desire a pre-built, cloud-based solution for SuccessFactors user provisioning
Organizations that require direct user provisioning from SuccessFactors to Microsoft Entra ID
Organizations that require users to be provisioned using data obtained from the SuccessFactors Employee Central (EC)
Organizations using Microsoft 365 for email
Solution Architecture
This section describes the end-to-end user provisioning solution architecture for cloud-only users. There are two related flows:
Authoritative HR Data Flow – from SuccessFactors to Microsoft Entra ID: In this flow worker events (such as New Hires, Transfers, Terminations) first occur in the cloud SuccessFactors Employee Central and then the event data flows into Microsoft Entra ID. Depending on the event, it may lead to create/update/enable/disable operations in Microsoft Entra ID.
Email Writeback Flow – from Microsoft Entra ID to SuccessFactors: Once the account creation is complete in Microsoft Entra ID, the email attribute value or UPN generated in Microsoft Entra ID can be written back to SuccessFactors.

End-to-end user data flow
- The HR team performs worker transactions (Joiners/Movers/Leavers or New Hires/Transfers/Terminations) in SuccessFactors Employee Central
- The Microsoft Entra provisioning service runs scheduled synchronizations of identities from SuccessFactors EC and identifies changes that need to be processed for sync with Microsoft Entra ID.
- The Microsoft Entra provisioning service determines the change and invokes create/update/enable/disable operation for the user in Microsoft Entra ID.
- If the SuccessFactors Writeback app is configured, then the user's email address is retrieved from Microsoft Entra ID.
- Microsoft Entra provisioning service writes back email attribute to SuccessFactors, based on the matching attribute used.
Planning your deployment
Configuring Cloud HR driven user provisioning from SuccessFactors to Microsoft Entra ID requires considerable planning covering different aspects such as:
- Determining the Matching ID
- Attribute mapping
- Attribute transformation
- Scoping filters
Please refer to the cloud HR deployment plan for comprehensive guidelines around these topics. Please refer to the SAP SuccessFactors integration reference to learn about the supported entities, processing details and how to customize the integration for different HR scenarios.
Configuring SuccessFactors for the integration
A common requirement of all the SuccessFactors provisioning connectors is that they require credentials of a SuccessFactors account with the right permissions to invoke the SuccessFactors OData APIs. This section describes steps to create the service account in SuccessFactors and grant appropriate permissions.
- Create/identify API user account in SuccessFactors
- Create an API permissions role
- Create a Permission Group for the API user
- Grant Permission Role to the Permission Group
Create/identify API user account in SuccessFactors
Work with your SuccessFactors admin team or implementation partner to create or identify a user account in SuccessFactors that will be used to invoke the OData APIs. The username and password credentials of this account will be required when configuring the provisioning apps in Microsoft Entra ID.
Create an API permissions role
Log in to SAP SuccessFactors with a user account that has access to the Admin Center.
Search for Manage Permission Roles, then select Manage Permission Roles from the search results.
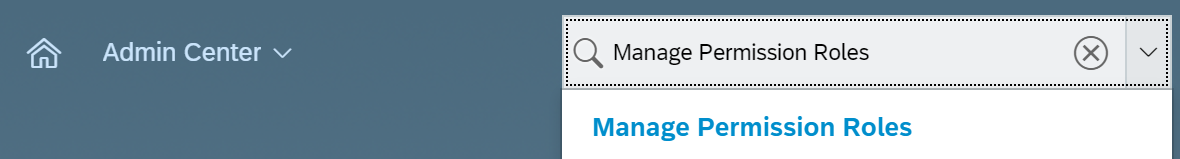
From the Permission Role List, click Create New.

Add a Role Name and Description for the new permission role. The name and description should indicate that the role is for API usage permissions.
Under Permission settings, click Permission..., then scroll down the permission list and click Manage Integration Tools. Check the box for Allow Admin to Access to OData API through Basic Authentication.

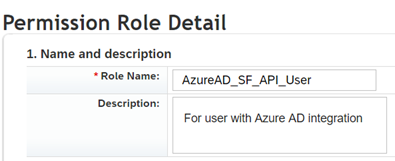
Scroll down in the same box and select Employee Central API. Add permissions as shown below to read using ODATA API and edit using ODATA API. Select the edit option if you plan to use the same account for the Writeback to SuccessFactors scenario.
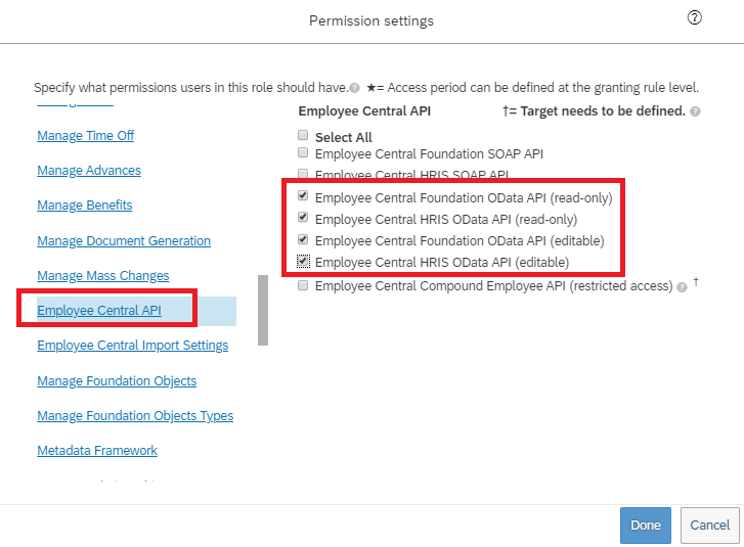
In the same permissions box, go to User Permissions -> Employee Data and review the attributes that the service account can read from the SuccessFactors tenant. For example, to retrieve the Username attribute from SuccessFactors, ensure that "View" permission is granted for this attribute. Similarly review each attribute for view permission.
Note
For the complete list of attributes retrieved by this provisioning app, please refer to SuccessFactors Attribute Reference
Click on Done. Click Save Changes.
Create a Permission Group for the API user
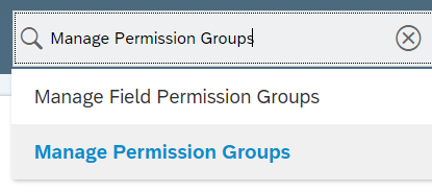
- In the SuccessFactors Admin Center, search for Manage Permission Groups, then select Manage Permission Groups from the search results.
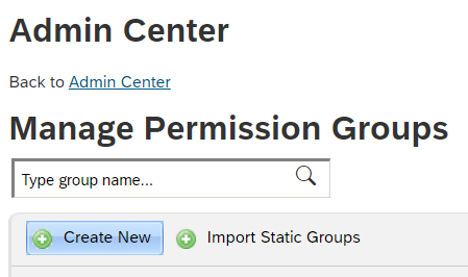
- From the Manage Permission Groups window, click Create New.
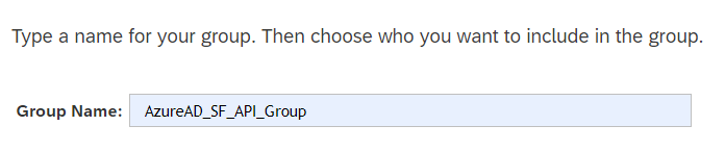
- Add a Group Name for the new group. The group name should indicate that the group is for API users.
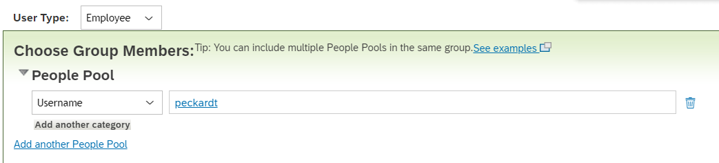
- Add members to the group. For example, you could select Username from the People Pool drop-down menu and then enter the username of the API account that will be used for the integration.
- Click Done to finish creating the Permission Group.
Grant Permission Role to the Permission Group
- In SuccessFactors Admin Center, search for Manage Permission Roles, then select Manage Permission Roles from the search results.
- From the Permission Role List, select the role that you created for API usage permissions.
- Under Grant this role to..., click Add... button.
- Select Permission Group... from the drop-down menu, then click Select... to open the Groups window to search and select the group created above.
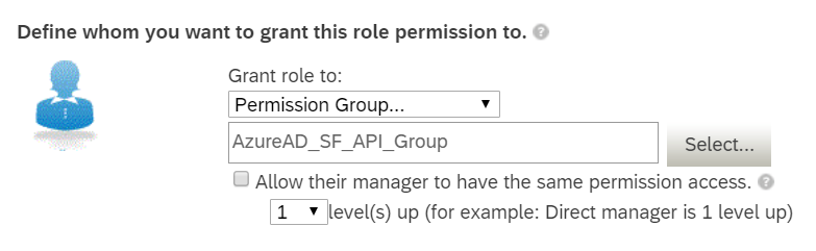
- Review the Permission Role grant to the Permission Group.
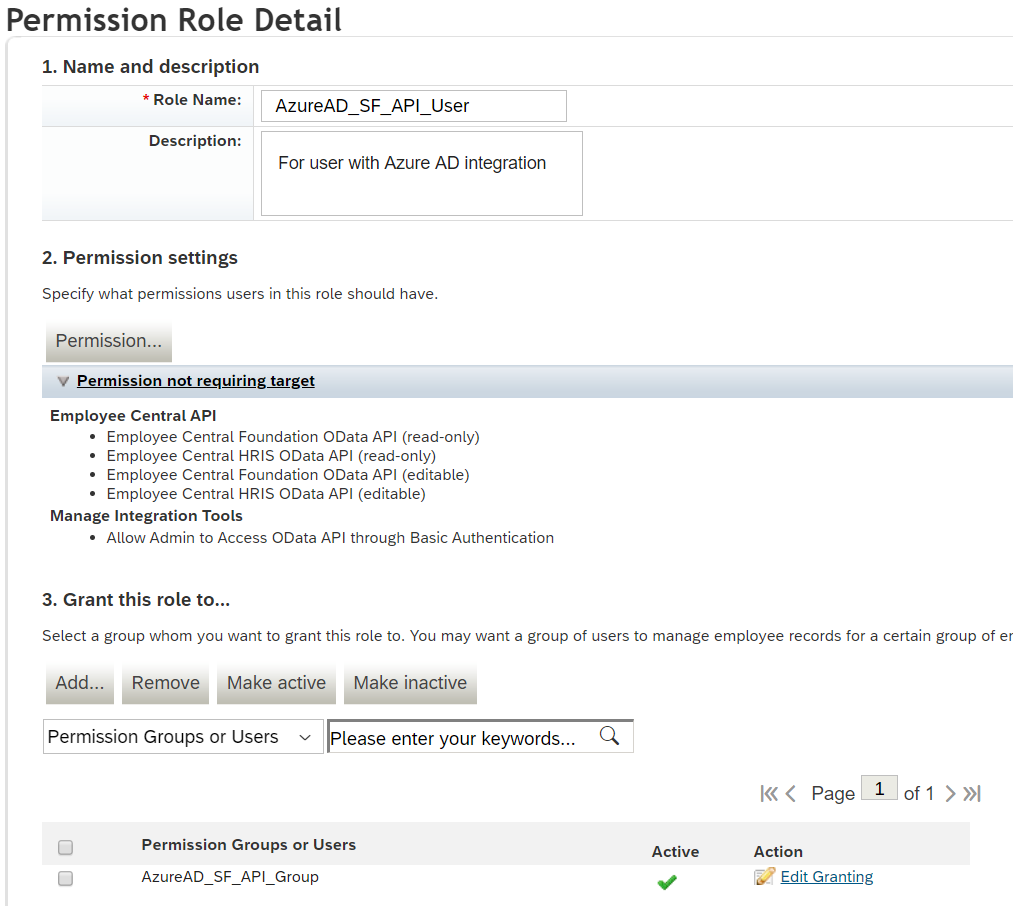
- Click Save Changes.
Configuring user provisioning from SuccessFactors to Microsoft Entra ID
This section provides steps for user account provisioning from SuccessFactors to Microsoft Entra ID.
- Add the provisioning connector app and configure connectivity to SuccessFactors
- Configure attribute mappings
- Enable and launch user provisioning
Part 1: Add the provisioning connector app and configure connectivity to SuccessFactors
To configure SuccessFactors to Microsoft Entra provisioning:
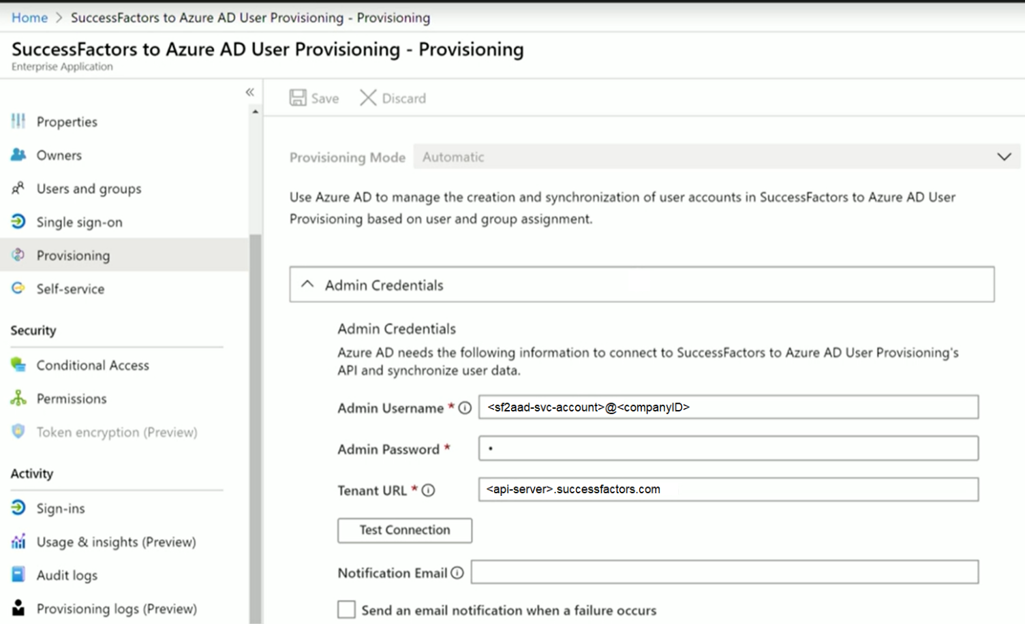
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
Browse to Identity > Applications > Enterprise applications > New application.
Search for SuccessFactors to Microsoft Entra user provisioning, and add that app from the gallery.
After the app is added and the app details screen is shown, select Provisioning
Change the Provisioning Mode to Automatic
Complete the Admin Credentials section as follows:
Admin Username – Enter the username of the SuccessFactors API user account, with the company ID appended. It has the format: username@companyID
Admin password – Enter the password of the SuccessFactors API user account.
Tenant URL – Enter the name of the SuccessFactors OData API services endpoint. Only enter the host name of server without http or https. This value should look like: api-server-name.successfactors.com.
Notification Email – Enter your email address, and check the "send email if failure occurs" checkbox.
Note
The Microsoft Entra provisioning service sends email notification if the provisioning job goes into a quarantine state.
- Click the Test Connection button. If the connection test succeeds, click the Save button at the top. If it fails, double-check that the SuccessFactors credentials and URL are valid.
- Once the credentials are saved successfully, the Mappings section displays the default mapping Synchronize SuccessFactors Users to Microsoft Entra ID
Part 2: Configure attribute mappings
In this section, you'll configure how user data flows from SuccessFactors to Microsoft Entra ID.
On the Provisioning tab under Mappings, click Synchronize SuccessFactors Users to Microsoft Entra ID.
In the Source Object Scope field, you can select which sets of users in SuccessFactors should be in scope for provisioning to Microsoft Entra ID, by defining a set of attribute-based filters. The default scope is "all users in SuccessFactors". Example filters:
Example: Scope to users with personIdExternal between 1000000 and 2000000 (excluding 2000000)
Attribute: personIdExternal
Operator: REGEX Match
Value: (1[0-9][0-9][0-9][0-9][0-9][0-9])
Example: Only employees and not contingent workers
Attribute: EmployeeID
Operator: IS NOT NULL
Tip
When you are configuring the provisioning app for the first time, you'll need to test and verify your attribute mappings and expressions to make sure that it's giving you the desired result. Microsoft recommends using the scoping filters under Source Object Scope to test your mappings with a few test users from SuccessFactors. Once you've verified that the mappings work, then you can either remove the filter or gradually expand it to include more users.
Caution
The default behavior of the provisioning engine is to disable/delete users that go out of scope. This may not be desirable in your SuccessFactors to Microsoft Entra integration. To override this default behavior refer to the article Skip deletion of user accounts that go out of scope
In the Target Object Actions field, you can globally filter what actions are performed in Microsoft Entra ID. Create and Update are most common.
In the Attribute mappings section, you can define how individual SuccessFactors attributes map to Microsoft Entra attributes.
Note
For the complete list of SuccessFactors attribute supported by the application, please refer to SuccessFactors Attribute Reference
Click on an existing attribute mapping to update it, or click Add new mapping at the bottom of the screen to add new mappings. An individual attribute mapping supports these properties:
Mapping Type
Direct – Writes the value of the SuccessFactors attribute to the Microsoft Entra attribute, with no changes
Constant - Write a static, constant string value to the Microsoft Entra attribute
Expression – Allows you to write a custom value to the Microsoft Entra attribute, based on one or more SuccessFactors attributes. For more info, see this article on expressions.
Source attribute - The user attribute from SuccessFactors
Default value – Optional. If the source attribute has an empty value, the mapping will write this value instead. Most common configuration is to leave this blank.
Target attribute – The user attribute in Mirosoft Microsoft Entra ID.
Match objects using this attribute – Whether or not this mapping should be used to uniquely identify users between SuccessFactors and Microsoft Entra ID. This value is typically set on the Worker ID field for SuccessFactors, which is typically mapped to one of the Employee ID attributes in Mirosoft Microsoft Entra ID.
Matching precedence – Multiple matching attributes can be set. When there are multiple, they are evaluated in the order defined by this field. As soon as a match is found, no further matching attributes are evaluated.
Apply this mapping
Always – Apply this mapping on both user creation and update actions
Only during creation - Apply this mapping only on user creation actions
To save your mappings, click Save at the top of the Attribute-Mapping section.
Once your attribute mapping configuration is complete, you can now enable and launch the user provisioning service.
Enable and launch user provisioning
Once the SuccessFactors provisioning app configurations have been completed, you can turn on the provisioning service.
Tip
By default when you turn on the provisioning service, it will initiate provisioning operations for all users in scope. If there are errors in the mapping or SuccessFactors data issues, then the provisioning job might fail and go into the quarantine state. To avoid this, as a best practice, we recommend configuring Source Object Scope filter and testing your attribute mappings with a few test users before launching the full sync for all users. Once you have verified that the mappings work and are giving you the desired results, then you can either remove the filter or gradually expand it to include more users.
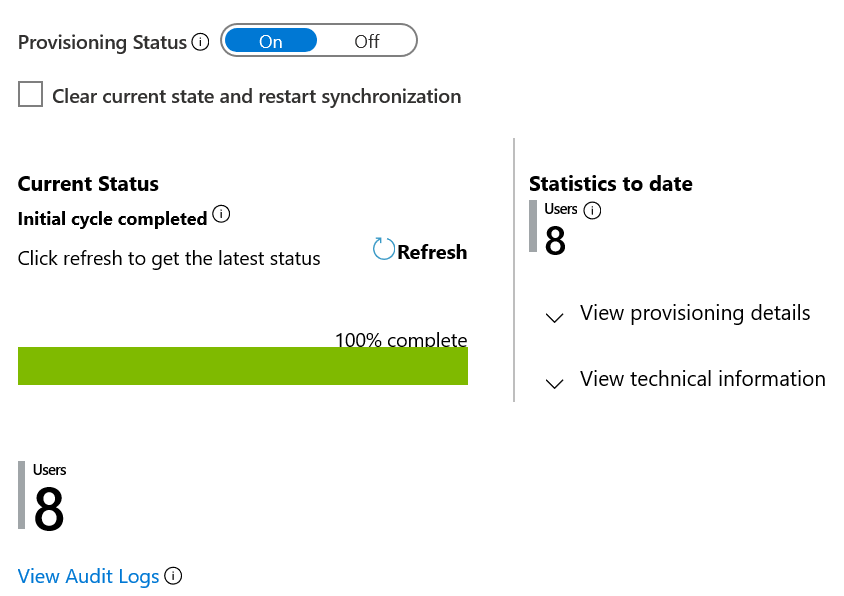
In the Provisioning tab, set the Provisioning Status to On.
Click Save.
This operation will start the initial sync, which can take a variable number of hours depending on how many users are in the SuccessFactors tenant. You can check the progress bar to the track the progress of the sync cycle.
At any time, check the Audit logs tab in the Azure portal to see what actions the provisioning service has performed. The audit logs lists all individual sync events performed by the provisioning service, such as which users are being read out of SuccessFactors and then subsequently added or updated to Microsoft Entra ID.
Once the initial sync is completed, it will write an audit summary report in the Provisioning tab, as shown below.
Next steps
- Learn more about supported SuccessFactors Attributes for inbound provisioning
- Learn how to configure email writeback to SuccessFactors
- Learn how to review logs and get reports on provisioning activity
- Learn how to configure single sign-on between SuccessFactors and Microsoft Entra ID
- Learn how to integrate other SaaS applications with Microsoft Entra ID
- Learn how to export and import your provisioning configurations
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for