Hi,
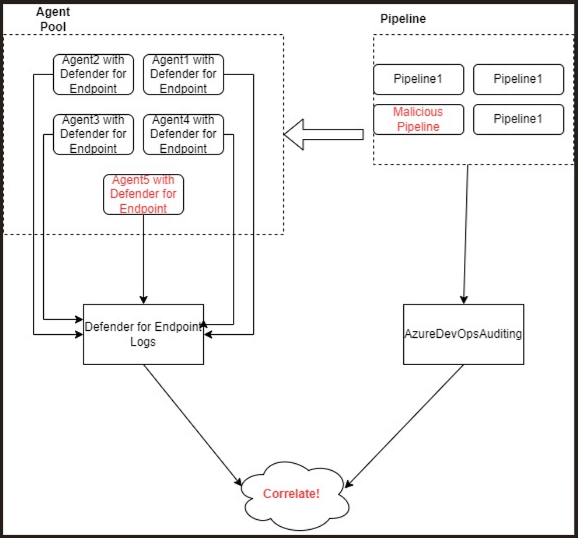
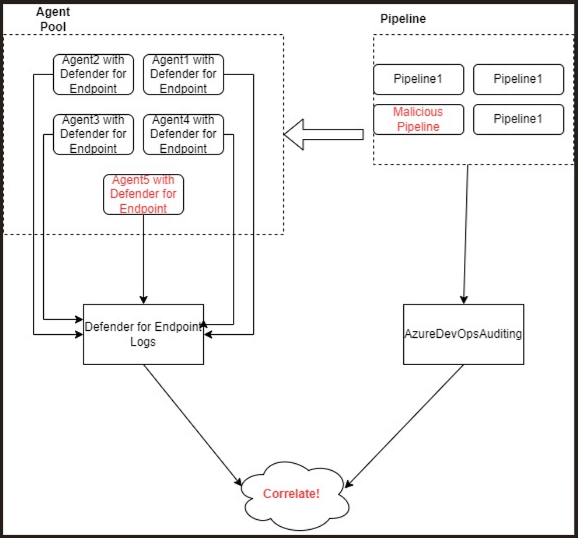
I am creating some detections specifically for the scope of pipeline agent pool runners, I have a couple of agent pools, each pool consists of many agents (host1, host2, host3), these agents have Defender for Endpoint running on them.
I have Azure DevOps auditing enabled with the below categories
Execute
Modify
Remove
Create
I identified a couple of use cases that can be a sign of malicious activity and I created the needed detection. But, the detection is only as useful as its context, so I need to correlate events happening on the agent runner (e.g host5 in below figure) with the pipeline that ran on this machine and specify the the runId that executed these actions.
Was trying to correlate these events using AzureDevOpsAuditing events but these don't contain any information about the agent.
Is there anyway to achieve this correlation? Any specific auditing config that I can enable to see such information?