Hello @MaBa217
Thank you for reaching out to us.
In reference to your questions please find the answers below
Is the SupportMultipleDomain Switch really required ? I don't want to make this my primary domain.
When you attempt to convert the new managed domain to be federated domain, without using SupportMultipleDomain an error will occurs. The reason is, Azure AD has a constraint that does not allow the IssuerUri property to have the same value for more than one domain.
To work around this constraint, you need to add a different IssuerUri, which can be done by using the -SupportMultipleDomain parameter. That is the reason SupportMultipleDomain is required.
Is this the only thing i need to do for converting it into the federated domain ?
In order to use the -SupportMultipleDomain switch when attempting to add new or convert already existing domains, your federated trust needs to have already been set up to support them.
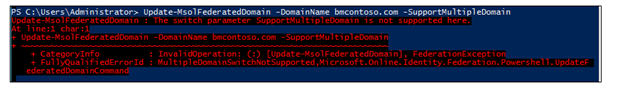
If you did not set up the federated trust between AD FS and your instance of Azure AD, you may need to re-create this trust. The reason is, when it is originally set up without the -SupportMultipleDomain parameter, the IssuerUri is set with the default value. In the screenshot below, you can see the IssuerUri is set to https://adfs.bmcontoso.com/adfs/services/trust.
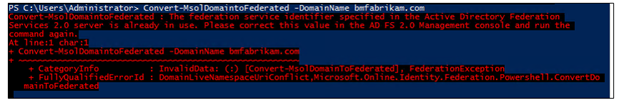
If you have successfully added a new domain in the Azure AD portal and then attempt to convert it using Convert-MsolDomaintoFederated -DomainName <your domain>, you will get the following error.
If you try to add the -SupportMultipleDomain switch, you will receive the following error:
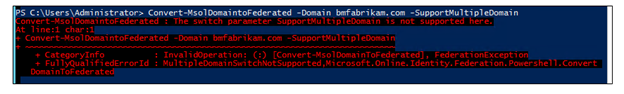
Simply trying to run Update-MsolFederatedDomain -DomainName <your domain> -SupportMultipleDomain on the original domain will also result in an error.
Use the steps below to add an additional top-level domain. If you have already added a domain, and did not use the -SupportMultipleDomain parameter, start with the steps for removing and updating your original domain. If you have not added a top-level domain yet, you can start with the steps for adding a domain using PowerShell of Azure AD Connect.
Use the following steps to remove the Microsoft Online trust and update your original domain.
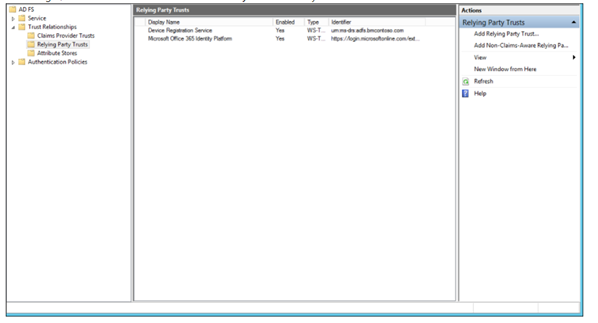
- On your AD FS federation server open AD FS Management.
- On the left, expand Trust Relationships and Relying Party Trusts
- On the right, delete the Microsoft Office 365 Identity Platform entry.
- On a machine that has Azure Active Directory Module for Windows PowerShell installed on it run the following: $cred=Get-Credential.
- Enter the username and password of a global administrator for the Azure AD domain you are federating with.
- In PowerShell, enter Connect-MsolService -Credential $cred
- In PowerShell, enter Update-MSOLFederatedDomain -DomainName <Federated Domain Name> -SupportMultipleDomain. This update is for the original domain. So using the above domains it would be: Update-MsolFederatedDomain -DomainName bmcontoso.com -SupportMultipleDomain
Use the following steps to add the new top-level domain using PowerShell
- On a machine that has Azure Active Directory Module for Windows PowerShell installed on it run the following: $cred=Get-Credential.
- Enter the username and password of a global administrator for the Azure AD domain you are federating with
- In PowerShell, enter Connect-MsolService -Credential $cred
- In PowerShell, enter New-MsolFederatedDomain –SupportMultipleDomain –DomainName
Use the following steps to add the new top-level domain using Azure AD Connect.
- Launch Azure AD Connect from the desktop or start menu
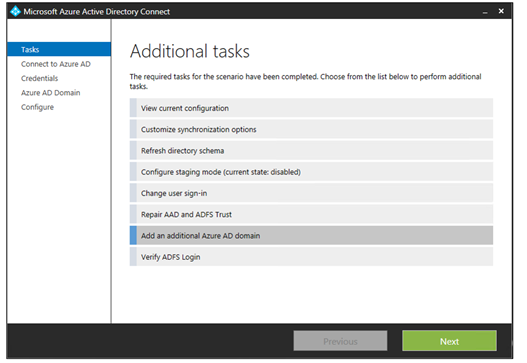
- Choose “Add an additional Azure AD Domain”
- Enter your Azure AD and Active Directory credentials
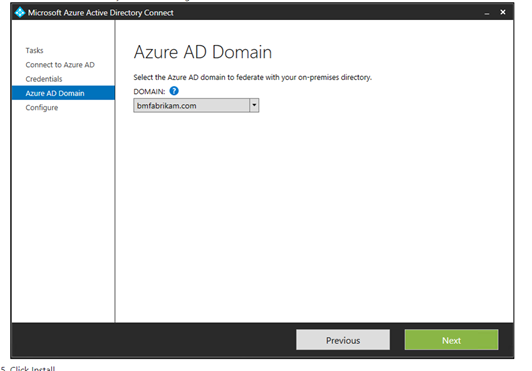
- Select the second domain you wish to configure for federation.
More information about this process can be found in this link.
In case you have any questions on the same, you can surely let us know and we will be happy to help you further. If this post provides you the answer you were looking for, do accept it as an answer in the interest of community members with similar queries. If this does not answer, please ask further in the comments and we will happy to address your concerns.
Thank you.