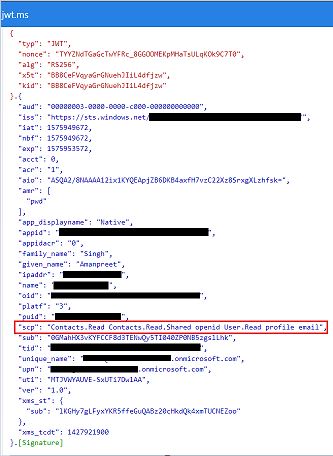
@displayName~~ I don't see any problem with the request. I just updated the client_id and redirect_uri parameters in the same call that you have shared and I was able to get a valid access token with all the required scopes. Below is the call and a snip of the token that I got:
https://login.microsoftonline.com/common/oauth2/v2.0/authorize?client_id=f0d5befe-xxxx-xxxx-xxxx-xxxxxxxxxxxx&response_type=token&redirect_uri=https://jwt.ms/&scope=offline_access openid contacts.read contacts.read.shared user.read&nonce=89289&response_mode=fragment
Are you using federated account? I am suspecting that you are capturing the token issued by federated IDP and not by Azure AD. If that is the case, please try with cloud only account and see if you get a valid access token.
-----------------------------------------------------------------------------------------------------------
Please "mark as answer" or "vote as helpful" wherever the information provided helps you to help others in the community.
