I was able to look into your question and will provide some links below that will hopefully help.
When it comes to a CASB specific feature, there's Microsoft Cloud App Security, which is a Cloud Access Security Broker(CASB) that supports various deployment models including log collection, API connectors, and reverse proxy. I wasn't able to find proxy specific documentation, however, you can find out more using the links below.
Links:
- Microsoft Cloud App Security Documentation
- Get Started with Microsoft Cloud App Security
- Cloud App Security Best Practices
- Connect Office365 to Microsoft Cloud App Security
- Connect G Suite to Microsoft Cloud App Security
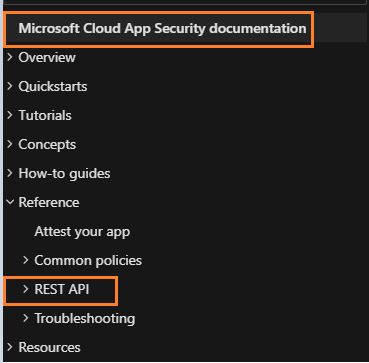
Lastly, you should be able to navigate through the Microsoft Cloud App Security Documentation using the left tile page if you need more info: 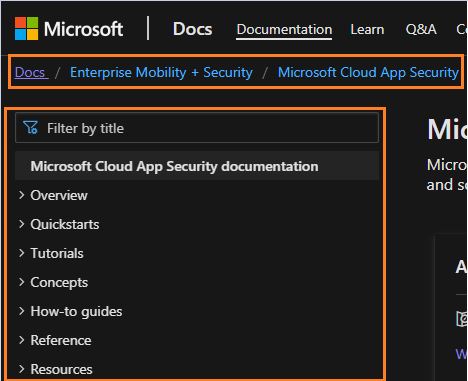
Hopefully this helps answer questions, if after reading through the docs you have any more questions please let me know!
Please do not forget to "Accept the answer", whenever the information provided helps you. This will help others in the community.