Hi @Prem ,
>Where is the fallback certificate stored? Is it in-memory, is it in master.sys.certificates or somewhere else.
Quote from this thread ;
By default, the certificate is located in the registry, at:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Microsoft SQL Server\MSSQL.x\MSSQLServer\SuperSocketNetLib
(Where the MSSQL.x is MSSQL.x is a placeholder for the corresponding value of the instance of SQL Server.)
If SQL server cannot find a certificate at that location, it will fall back to searching the certificate store for a certificate with the FQDN of the computer it is installed on. By default, that certificate would be the machine certificate, found in Local Computer -> Personal -> Certificates through the MMC Certificates snap-in.
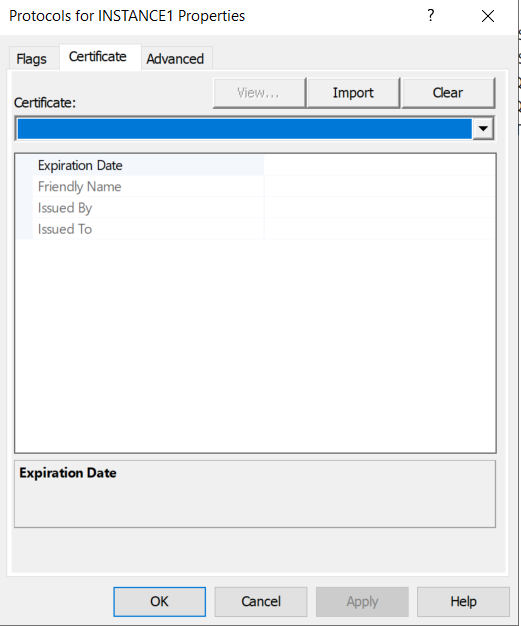
You would check the key length (and other properties) of this (or any) certificate through the MMC Certificates snap-in, by browsing to it, double clicking on it, and then hitting the Details tab in the ensuing dialogue box that comes up for the certificate.
>When "Force Encryption" is set to Yes on the SQL Server instance and we don't have our own certificate and instead rely on the SQL fallback certificate, why do clients trust this certificate even if the "Trust Server Certificate" option (in SSMS) is unchecked.
Quote from MS document;
To enable encryption when a certificate has not been provisioned on the server, the Force Protocol Encryption and the Trust Server Certificate options must be set in SQL Server Configuration Manager. In this case, encryption will use a self-signed server certificate without validation if no verifiable certificate has been provisioned on the server.
If the answer is helpful, please click "Accept Answer" and kindly upvote it. If you have extra questions about this answer, please click "Comment".