Hi ,
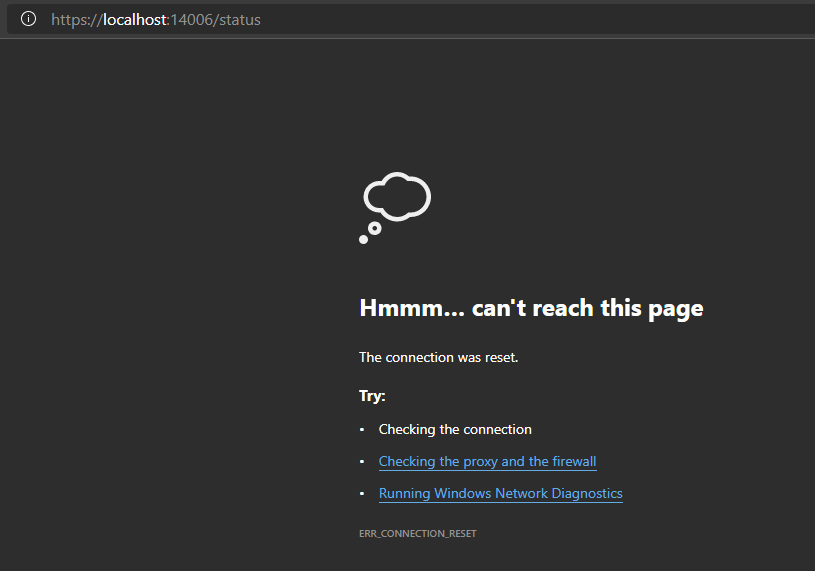
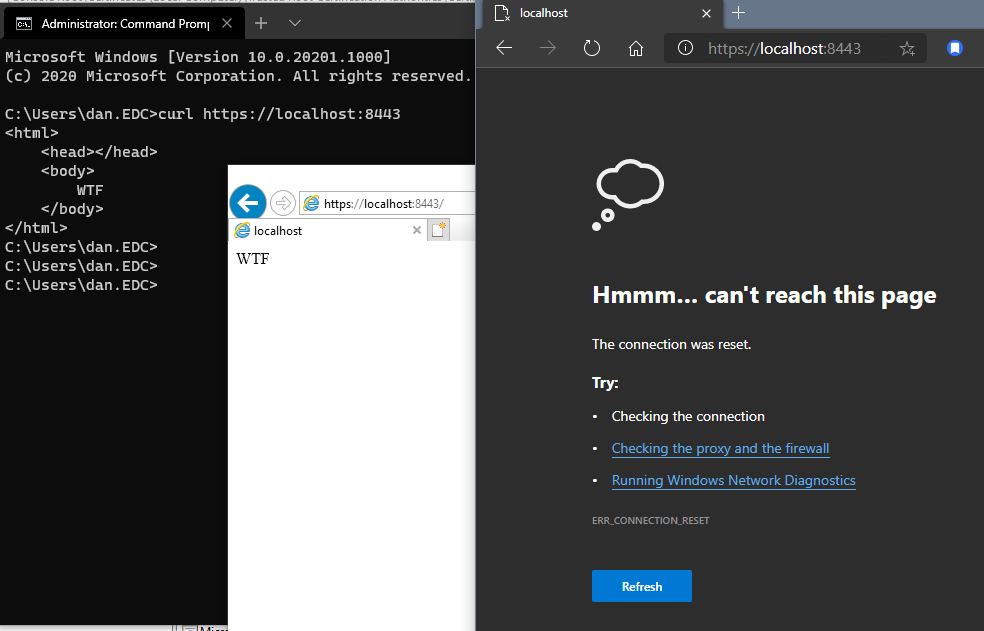
>>Both computers I tested on are running Windows 10 Pro for Workstations Insider Preview version 2004. The desktop is running 20201.1000 and the laptop 20190.1000.
The Feedback Hub app lets you tell Microsoft about any problems you run in to while using Windows 10. You can report this issue to Microsoft directly with the Feedback Hub app.
For more information on using the app, click here:
There might be some early adopter issues at this time with Windows 10 2004, if possible, I would recommend you wait a bit until Windows 10 2004 matures with future cumulative updates.
If this issue is urgent, I would also suggest you contact Microsoft Customer Support and Services where more in-depth investigation can be done so that you would get a more satisfying explanation and solution to this issue.
You may find phone number for your region accordingly from the link below:
https://support.microsoft.com/en-us/help/4051701/global-customer-service-phone-numbers
Best Regards,
Candy