Hi Fadil CK (@Fadil Ck ),
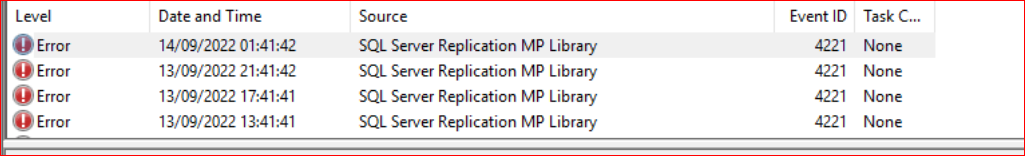
so the cause is clear - The agent is running under Local System, but Local System has no SQL permissions by default (I think since SQL 2012 if I am not mistaken).
So, the solution here is: distribute your SQL Monitoring account to the respective agent health service.
Now to your question: "SQL run as account not distributed to this agent. can we choose the Less secure option, so that it can distribute to all sql servers? any major impact if we give this option?"
Yes, you can chose the "less secure" option and "Yes" there will be some impact idf you do so - all the servers, which do not have this account (cannot leverage it) will start generating alerts, beause they are getting the account. So, you will need to do some grouping and overriding if you chose "Less Secure".
There is one more thing, it is described in the office documentation here:
Comparing more secure and less secure distribution
https://learn.microsoft.com/en-us/system-center/scom/manage-security-dist-target-runas-profiles?view=sc-om-2022#comparing-more-secure-and-less-secure-distribution
If Operations Manager automatically distributed the Runs As account according to discovery a security risk would be introduced into your environment as illustrated in the following example. This is why an automatic distribution option was not included in Operations Manager.
and the risk is (again from the same article):
For example, Operations Manager identifies a computer as hosting SQL Server 2014 based on the presence of a registry key. It is possible to create that same registry key on a computer that is not actually running an instance of SQL Server 2014. If Operations Manager were to automatically distribute the credentials to all agent managed computers that have been identified as SQL Server 2014 computers, then the credentials would be sent to the imposter SQL Server and they would be available to someone with administrator rights on that server.
Last, but not least, many security auditors are labeling this also as a Security Risk:
Manually configured SCOM Run As accounts must be set to More Secure distribution.
https://www.stigviewer.com/stig/microsoft_scom/2021-03-15/finding/V-237424
So, my recommendation would be to chose "More Secure" and distribute the account to the systems that need it. But if you decide to chose "Less Secure" you will also solve the original problem of this post.
A small tip: You can also go the other way - monitorwithout service accounts. This is something i do in most oof the environments. This is very easily done with the help of Kevin Holmans MP:
SQL MP Run As Accounts – NO LONGER REQUIRED
https://kevinholman.com/2016/08/25/sql-mp-run-as-accounts-no-longer-required/
Take five minutes to read it and then you can deciode if this somethng for you or not.
I hope I could be of help!
----------
(If the reply was helpful please don't forget to upvote and/or accept as answer, thank you)
Regards
Stoyan Chalakov