What is ADFS, and why you should care?
Active Directory Federated Services (ADFS) doesn’t sound like the most exciting topic for a post, but I am going to post on it anyway precisely because it is boring.
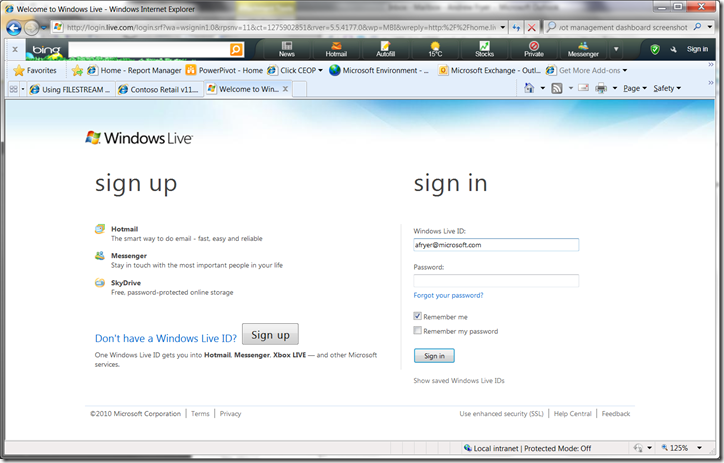
First let me log in to windows with a Live ID..
You’ll notice I have used my Microsoft alias to sign in, and I haven’t entered my password yet (my cursor is still in the Windows Live ID dialog box. What password should I enter? Putting my domain password in here might seem like a good choice, or it could be a password I have set up for this site like we all do on some social media sites. None of these is a good story for the user and it would be better not to have to enter a password at all. This is what I get when I tab to the password field..
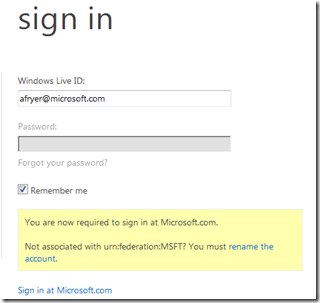
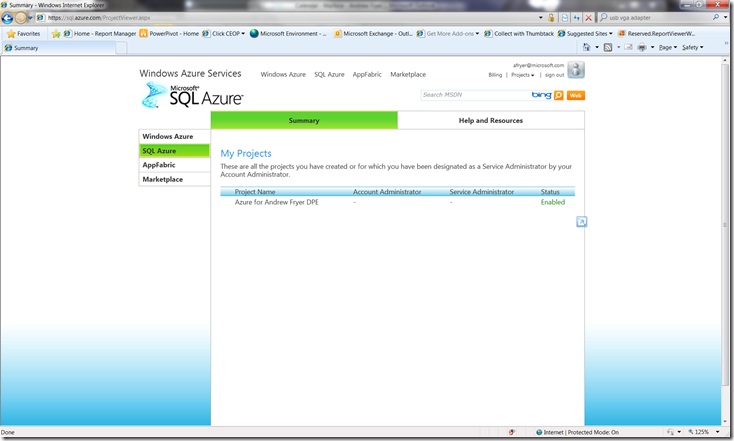
.. the Live service is asking me to sign in at Microsoft.com which is my domain. I click on this and I get to my SQL Azure account screen.
What you have just seen is ADFS in action. Essentially Live has been told to trust the Microsoft domain to authenticate users rather than have all the Microsoft logins duplicated in Live. Live is still responsible for authorisation i.e. deciding what I can do once I get in , and in this case the only Live service I can use with this account is Azure.
In the real (non-Microsoft world) this is very useful stuff..
- Today you want to allow users from another business to access your resources (SharePoint sites , e-mail etc), for example when trading with them or because they are contractors , or because you have outsourced some business function to them.
- In future as you move some parts of your IT to private or public cloud infrastructure you want all the security to be seamless for the users. A good example of this in Microsoft is that some of our agency staff have been moved over to use BPOS (the catchily named Business Productivity Online Suite) for Exchange etc. but are not aware that this has happened. For your own applications Access Control services in Azure will be integrated with ADFS v2
Of course this technology isn’t much use unless you can also pass identity information across platforms as well as federating credentials across different active directory domains. ADFS can also be integrated with other federation platforms including IBM Tivoli, Novell Access manager, Sun Open SSO and CA (Site Minder and Federation Manager) using SAML (Security Assertion Mark-up Language). Also Microsoft’s is one of the co founders of OpenID, the organisation that is promoting standards in identity management.
Exactly where is ADFS? The first version of this was simply a role that you configured in Windows Server 2008 /2008 R2, and to store any additional data above and beyond active directory there is a separate data store which is of course SQL Server (Express is fine for this). The latest version that does all the stuff I have described here is a separate download from here along with all the whitepapers step by step guides you’ll need to get started.
To conclude, ADFS is boring for the users because there’s nothing to see, but is a good example of the sort of work that will continue to be done by IT professionals over the next few years as business transitions between traditional on premise solutions and a mix of these plus private / public cloud based services.