Safely setting autologon for Windows
When configuring Microsoft Windows to auto-logon, most people just modify the following keys in the registry:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\AutoAdminLogon
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\DefaultUserName
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\DefaultPassword
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\DefaultDomain
However, the problem with doing it that way is that the password for the user account is stored in the registry as unencrypted text, which means that anyone with enough rights to view the registry, be it locally or remotely, can view the password easily and potentially compromise the system. This also applies if the computer was infected with a virus or malware, which could also potentially read the configured auto-logon user credentials and then send them over the internet for future malicious use.
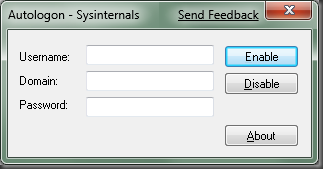
However, if you use the Sysinternals tool AutoLogons to configure the auto-logon then the password string value is stored encrypted in the registry as an LSA secret. Which means that, once the autologon is configured, the unencrypted version of the password used cannot be viewed by anyone/anything at all.
The tool couldn’t be simpler to use, and most importantly, it helps to maintain the security of your systems.