TMG Enhanced NAT – considerations when using the Default IP Address
With TMG we introduced a feature called “Enhanced NAT” (ENAT). ENAT enables you to configure the IP address you want to use as source IP when you NAT the traffic between 2 networks. The IP address has to be configured on the Interface, which is connected to the Destination Network, before you can select it as source IP.
The default configuration of a Network Rule with NAT in TMG is to “Use the default IP address” of the network adapter as source address. With this configuration TMG behaves similar to ISA Server.
I didn’t say that TMG behaves the same way as ISA in this regards, because the difference between ISA Server and TMG in this case can be very important in some scenarios.
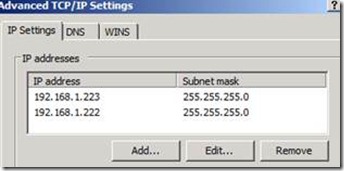
ISA Server did use the IP which had been configured in the first properties page of your network adapter TCP/IPv4 Properties:
In this case ISA would always use the 192.168.1.223 as source address when you configured a NAT relationship.
With TMG and ENAT things slightly change…
For all traffic handled by the Web Proxy Filter, TMG will still use the 192.168.1.223 in this scenario. It’s not possible to change this behavior because of the internal design of the Web Proxy Filter.
Please be aware, that the TMG Web Proxy Filter behavior in this regards doesn’t depend and cannot be modified by any Network Rule setting you configure.
For all other protocols, TMG will not always use the IP which had been configured on the “main property” page of the TCP/IPv4 settings, BUT TMG will use the smallest IP configured on this interface if you choose the “Use the default IP Address” setting.
Whats the smallest IP?
Consider the scenario, where you did configure the 192.168.1.223 on the main property page, and afterwards add the IP 192.168.1.222 in the Advanced Settings:
On the first TCP/IPv4 property page in Windows, you’ll still see the 192.168.1.223.
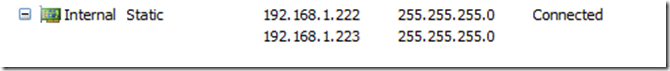
When you open the TMG MMC and open Networking -> Network Adapters, you’ll see this:
As 222 is smaller than 223, TMG chooses the 222 as Default IP.
To be aware of this change of the Default IP Addresses selection is very important, in scenarios with IPSec Site-2-Site where you expect the traffic with specific Source IP addresses, or in scenarios where the routing or firewall setup “expects” specific IP addresses in order to properly handle the traffic.
If you configure the NAT rule using the “Default IP address”, and add another smaller IP to your interface, TMG will automatically use the smaller IP address as source IP. If you didn’t modify your infrastructure configuration, this change can break IPSec connections or accidently block traffic send from TMG on the next Firewall, where you didn’t expect this change in IP.
Best Practices for ENAT
1. Avoid using the Default IP Address Setting when configuring NAT rules for interfaces with multiple IP addresses, or where you plan to add additional IP addresses later.
Try to use the “Use the specified IP address” or “Use multiple IP addresses” NAT Address Selection settings, whenever possible.
2. If you want to use the same “NAT” IP for Web Traffic handled by the Web Proxy Filter and for all other protocols, select the IP address specified on the first TCP/IPv4 property page when configuring a specified IP address.
Why did this behavior change from ISA to TMG?
The main cause for this change in behavior is a change in the Windows Pubic API GetAdaptersAddresses (http://msdn.microsoft.com/en-us/library/aa365915(VS.85).aspx ) which returns the IP addresses from the structure IP_ADAPTER_ADDRESSES (http://msdn.microsoft.com/en-us/library/aa366058(v=vs.85).aspx ) to determine the first IP address of an interface.
From the description of IP_ADAPTER_ADDRESSES we can see, that this structure changed from 2003 to 2008 or 2008 R2:
Quote:
The order of linked IP_ADAPTER_UNICAST_ADDRESS structures pointed to by the FirstUnicastAddress member that are returned by the GetAdaptersAddresses function does not reflect the order that IP addresses were added to an adapter and may vary between versions of Windows
This means that TMG only relies on the order of IP addresses returned by GetAdaptersAddresses, and will consider the first IP found in the list as the Primary IP (from a TMG perspective).
Author
Philipp Sand
Microsoft CSS Forefront Security Edge Team
Technical Reviewer
Eric Detoc
Microsoft CSS Forefront Security Edge Team