How to collect a good boot trace on Windows 7
Assume the following: You have a Windows 7 host that you want to collect a trace from. A good trace. One that you know other people will be able to decipher as well as yourself. Maybe I’ve asked you to collect a boot trace so I can look at it and pointed you to this blog. Maybe your Sherpa of IT has decided you should learn this and you are doing it to learn….
(edited 11-2)
[You may also use xperf's xbootmgr with a syntax similar to this:
xbootmgr -trace boot -traceflags base+latency+dispatcher -stackwalk profile+cswitch+readythread+threadcreate -notraceflagsinfilename -postbootdelay 30
]
In any event, you have a Windows 7 host.
Lets cover a few basic rules here as we get started:
1. If host = Windows 7 AND bitness = amd64 THEN Set DisablePagingExecutive to 1 and reboot:
2. Make sure the user account we want to trace is local administrator, even temporarily.
3. Set AutoLogon up in the registry for this user so we don’t flub a password input and invalidate a trace with bogus data:
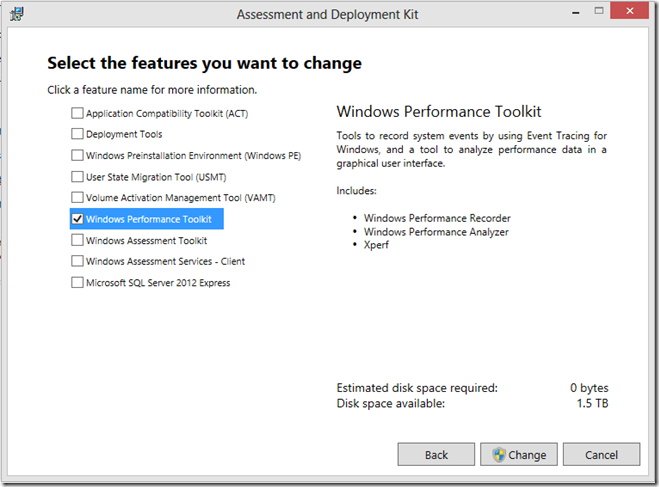
After we have that, install the Windows 8 ADK on the target machine, or copy the Windows Performance Toolkit from a machine it has already been installed on onto our target machine. (link https://www.microsoft.com/en-us/download/details.aspx?id=30652)
(We can install by running ADK Setup and deselecting EVERYTHING except Windows Performance Toolkit, by the way.)
So, its there, somewhere.
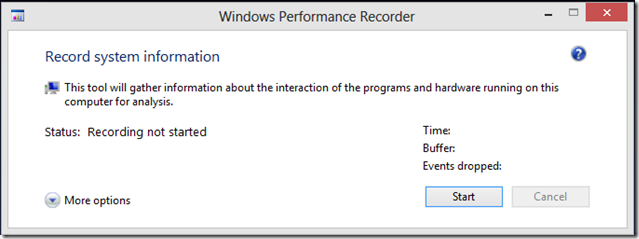
1. Run WPRUI elevated/as administrator
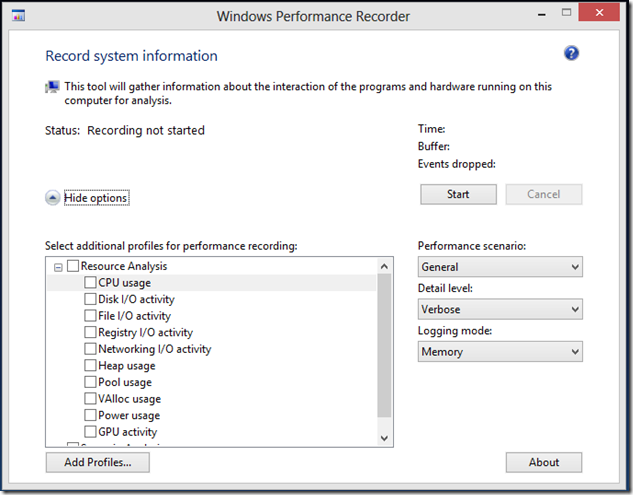
2. For a boot trace, click More Options on the bottom left, revealing the window that looks like this:
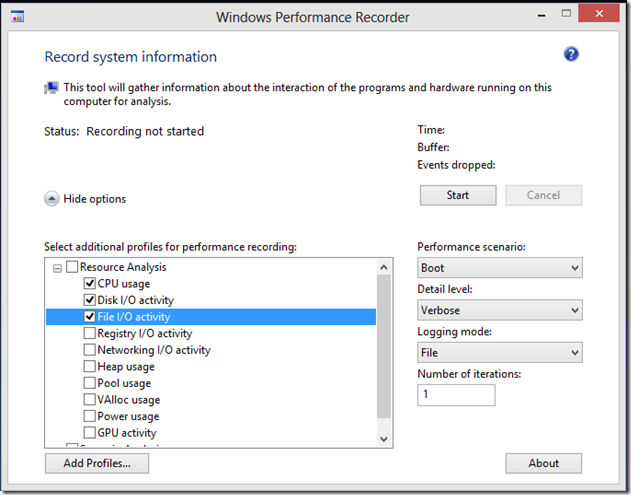
3. For the boot trace, I would like to see CPU Usage, Disk I/O Activity and File I/O Activity. I would like you to change the Performance Scenario to “Boot” and number of iterations to “1”, as so:
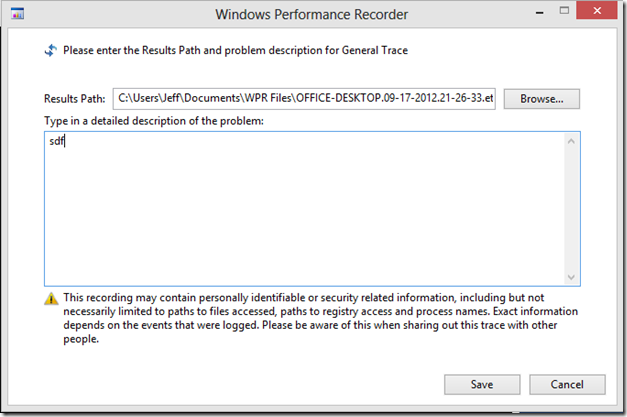
4. Click “Start” and then type something into the box and select a convenient place to store your trace and then hit “Save” which will reboot your machine and collect the trace.
5. Let it reboot, let it logon as the user you specified in the auto logon, let it count down the normal boot process and end with the ETL trace in the directory you specified. Get me that trace, stat! Or if you are doing this to learn, poke around in it in XperfView.exe and WPA.exe, two entirely different ways to view the data set.
Hope this helps, after I stand up a VM or two I’m going to do some WPA examples….