Creating a site-to-site VPN with Windows Azure and Mikrotik ( RouterOS )
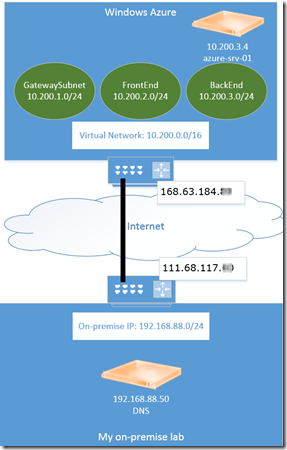
As many of you I have a small lab in my home, to test different solutions. I had been playing around with running virtual machines in Windows Azure, and I needed to connect them to my home lab using site-to-site VPN.
A word of caution: Virtual Machines and Network is still in preview. Everything in this article is based on the preview version.
If you have Cisco or Juniper VPN devices, you could download the configuration from the Windows Azure portal. However, this do not mean that you cannot connect other VPN devices, like in my case, the cheap Mikrotik 751 based on the RouterOS.
You can follow this guide to create the Virtual Network in Windows Azure:
https://www.windowsazure.com/en-us/manage/services/networking/cross-premises-connectivity/
Configuring the Mikrotik 751 router (RouterOS)
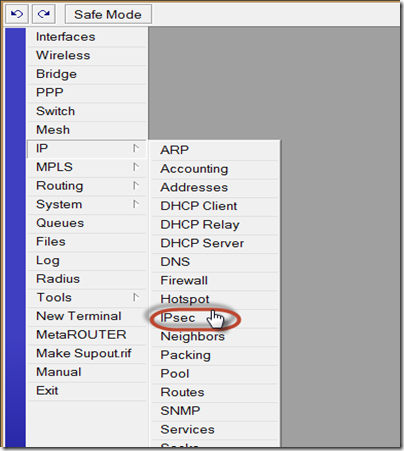
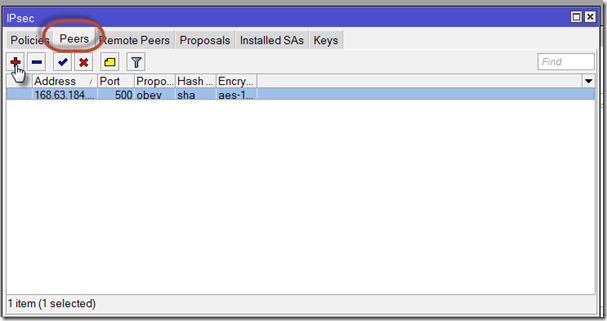
Step 1 – Configure Peers:
On the Peers tab, click the plus sign to add a new peer:
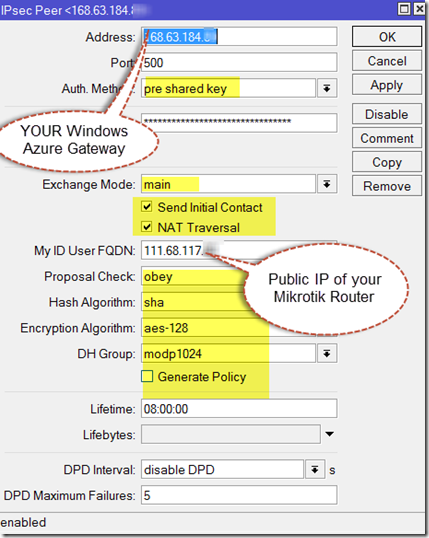
Here you need to add your Secret key generated by Windows Azure.
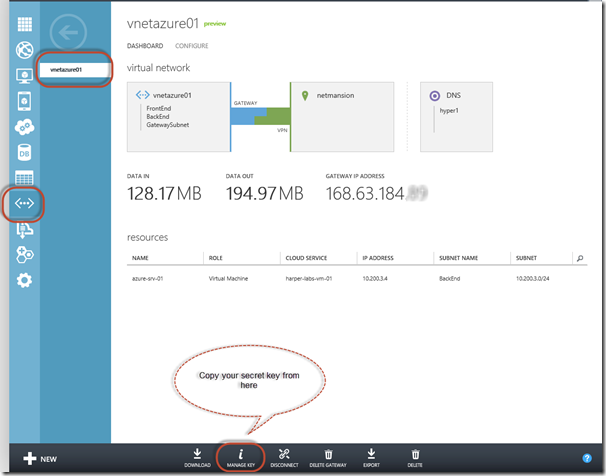
Log on to the WIndows Azure management portal, and get your key. To do that, go to your Virtual Network, and select manage key.
Step 2: Define the policy
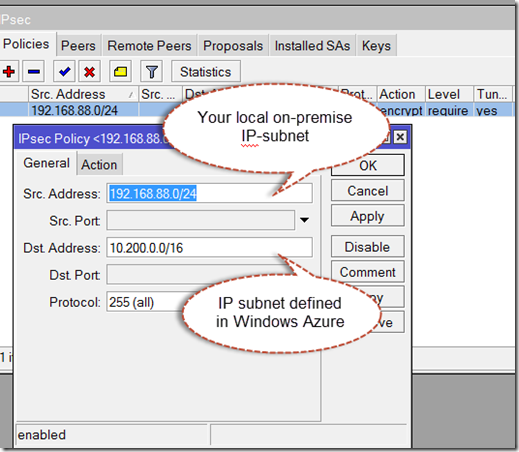
Next up is to define the policy. As I understand it, the MIkrotik router uses the policies to route traffic through the tunnel.
On the General tab I define the source and destination IP-subnets like this:
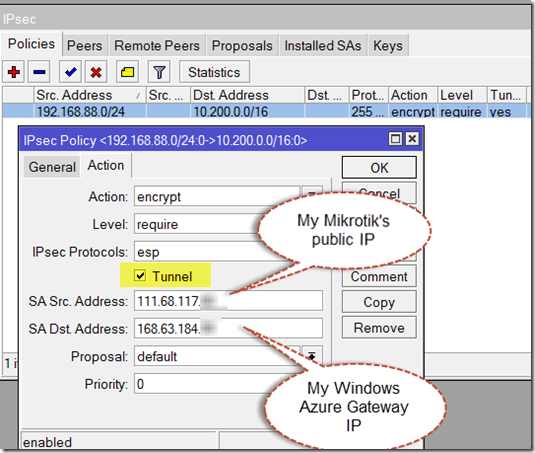
For the Action tab, I define the SA Source and destination addresses, and also that it should be a IPSec tunnel :
Step 3: Configure your proposal
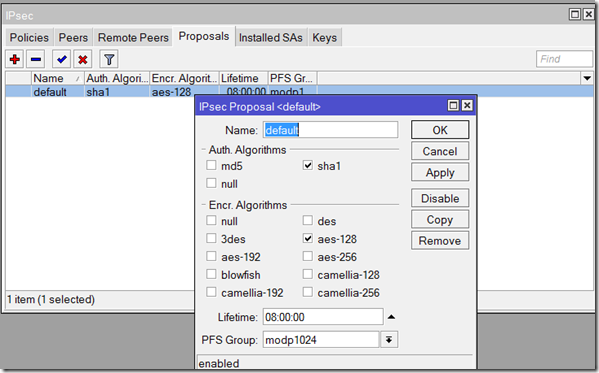
If you look at my proposal tab, I have the default proposal defined like this:
Step 4: Configure firewall
In my configuration I am using NAT (masqurade) when accessing Internet. However, I have to override this rule for my IPSec tunnel. Open up the Firewall configuration from IP->Firewall:
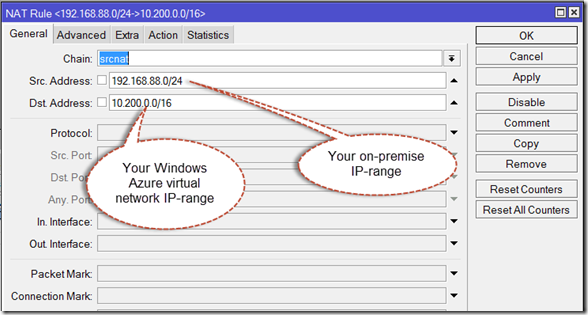
Next, configure the firewall to not NAT traffic destinated for the IPSec tunnel.
Open the NAT tab, and click the + sign to add the following:
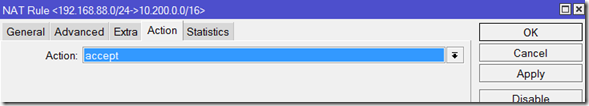
Make sure the Action is set to Accept
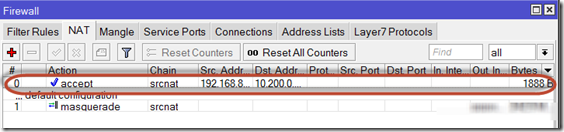
And make sure that this rule is above any conflicting rules you might have defined.
Step 5: Test connectivity
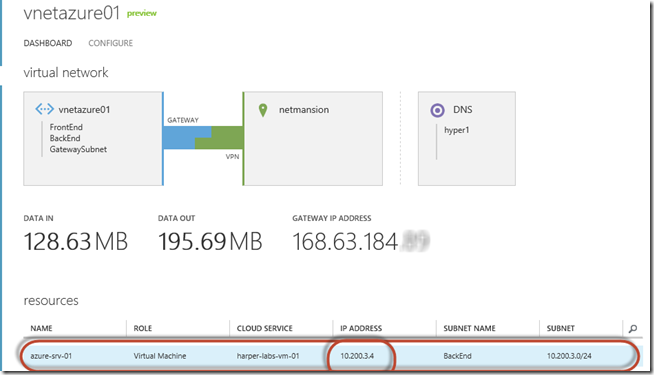
The only thing left now is to test the connectivity. I do know my virtual machine in Windows Azure is configured with the IP of 10.200.3.4:
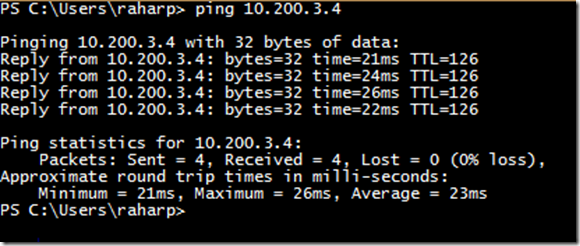
From my workstation, I open Powershell, and I try to ping 10.200.3.4:
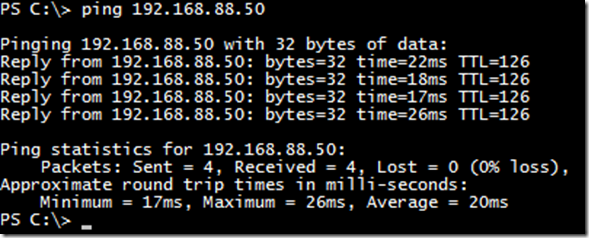
Then I RDP into my Windows Azure virtual machine, and try to ping my onpremise DNS host (192.168.88.50) :
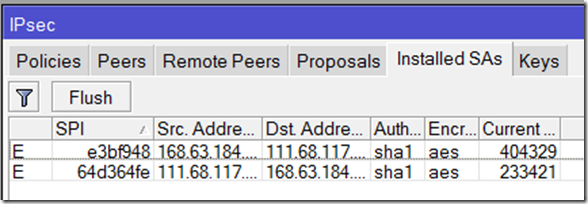
If I check my router for security associations under the Installed SAs tab, I can see the following:
If you want to try Windows Azure – you can get yourself a 90 days free trial at www.windowsazure.com