Microsoft Entra join a new Windows device during the out of box experience
Windows 11 users can join new Windows devices to Microsoft Entra ID during the first-run out-of-box experience (OOBE). This functionality enables you to distribute shrink-wrapped devices to your employees or students.
This functionality pairs well with mobile device management platforms like Microsoft Intune and tools like Windows Autopilot to ensure devices are configured according to your standards.
Prerequisites
To Microsoft Entra join a Windows device, the device registration service must be configured to enable you to register devices. For more information about prerequisites, see the article How to: Plan your Microsoft Entra join implementation.
Tip
Windows Home Editions do not support Microsoft Entra join. These editions can still access many of the benefits by using Microsoft Entra registration.
For information about how complete Microsoft Entra registration on a Windows device see the support article Register your personal device on your work or school network.
Join a new Windows 11 device to Microsoft Entra ID
Your device might restart several times as part of the setup process. Your device must be connected to the Internet to complete Microsoft Entra join.
- Turn on your new device and start the setup process. Follow the prompts to set up your device.
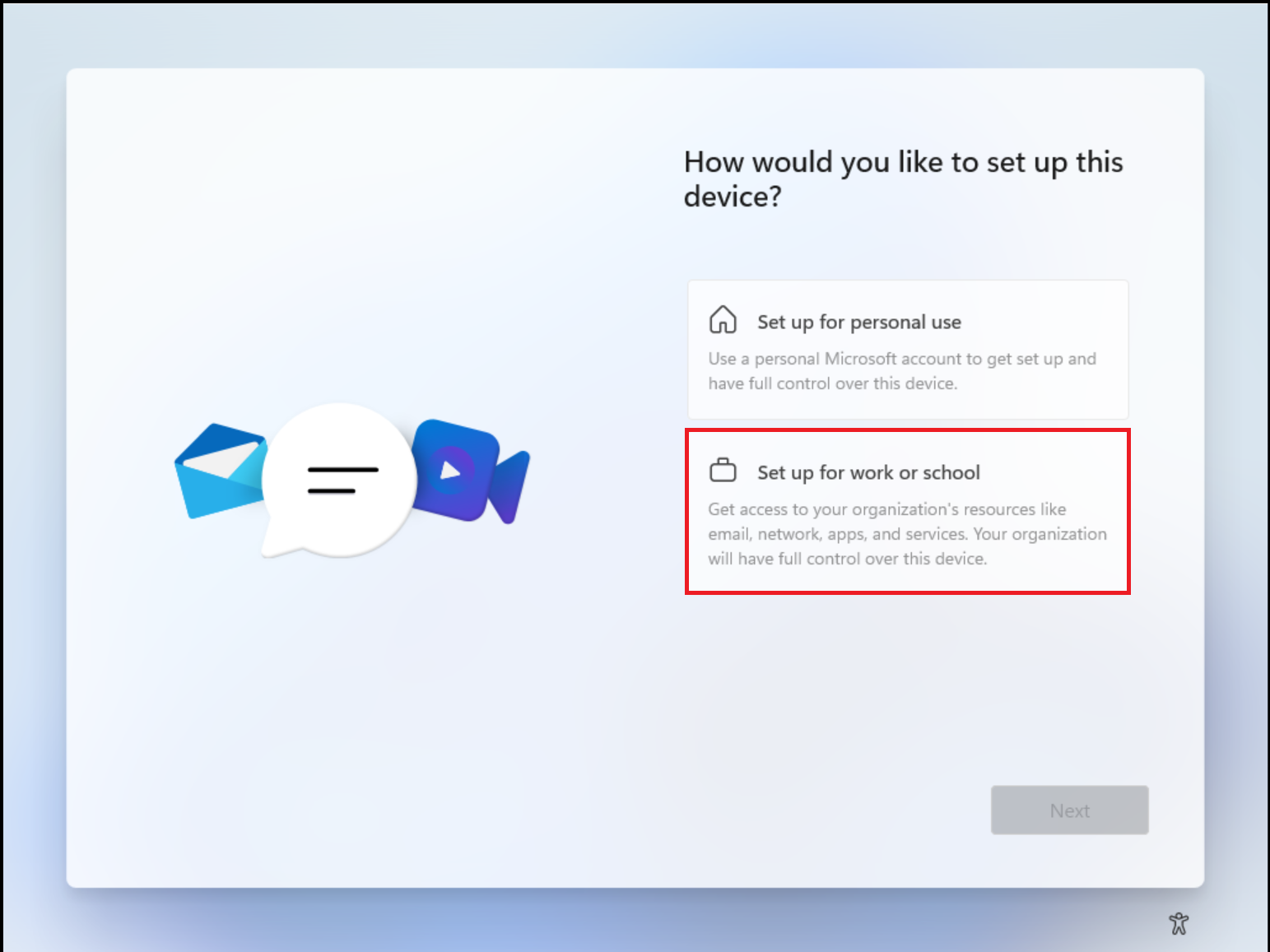
- When prompted How would you like to set up this device?, select Set up for work or school.
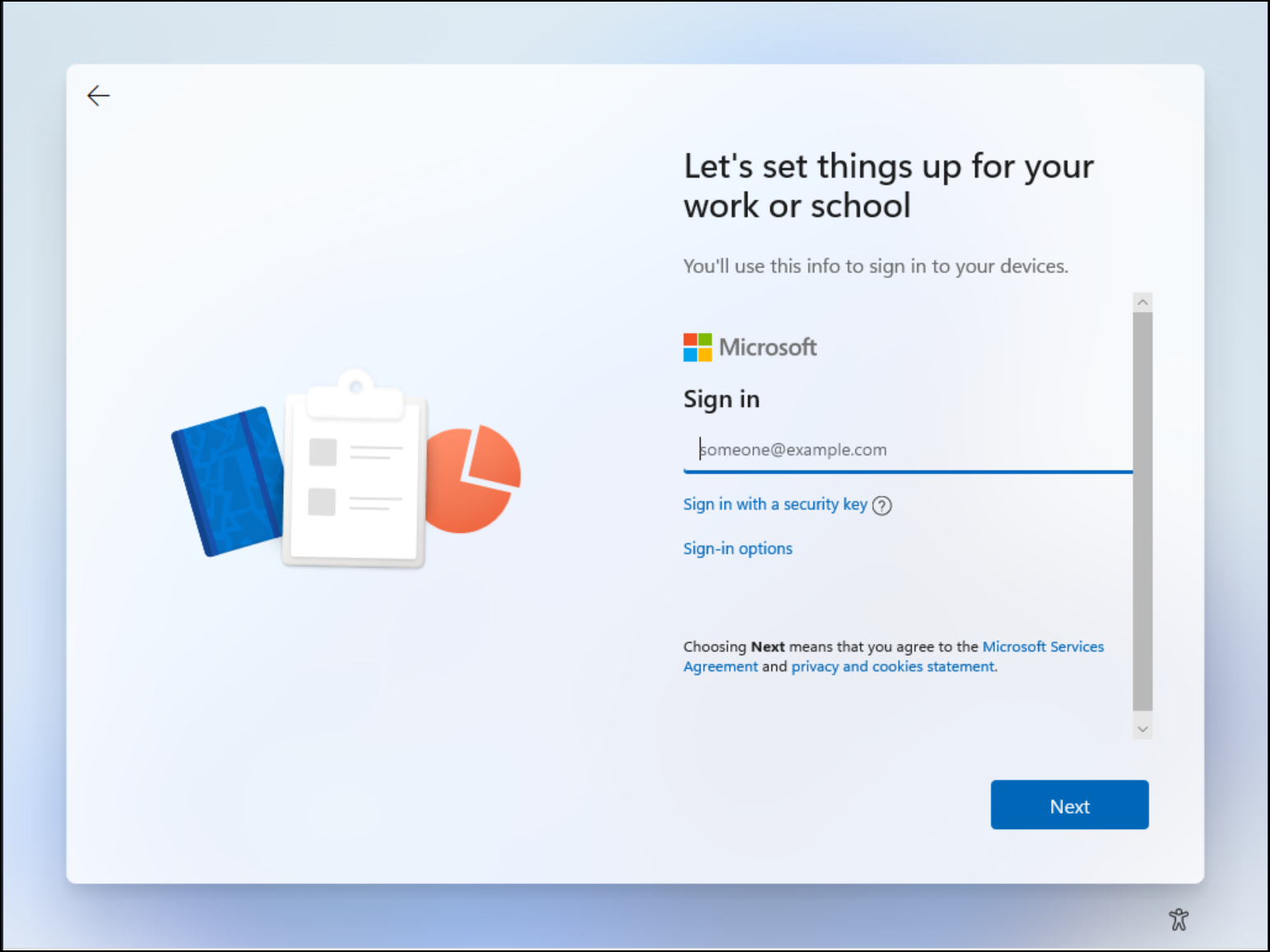
- On the Let's set things up for your work or school page, provide the credentials that your organization provided.
- Optionally you can choose to Sign in with a security key if one was provided to you.
- If your organization requires it, you might be prompted to perform multifactor authentication.
- Continue to follow the prompts to set up your device.
- Microsoft Entra ID checks if an enrollment in mobile device management is required and starts the process.
- Windows registers the device in the organization's directory and enrolls it in mobile device management, if applicable.
- If you sign in with a managed user account, Windows takes you to the desktop through the automatic sign-in process. Federated users are directed to the Windows sign-in screen to enter your credentials.

For more information about the out-of-box experience, see the support article Join your work device to your work or school network.
Verification
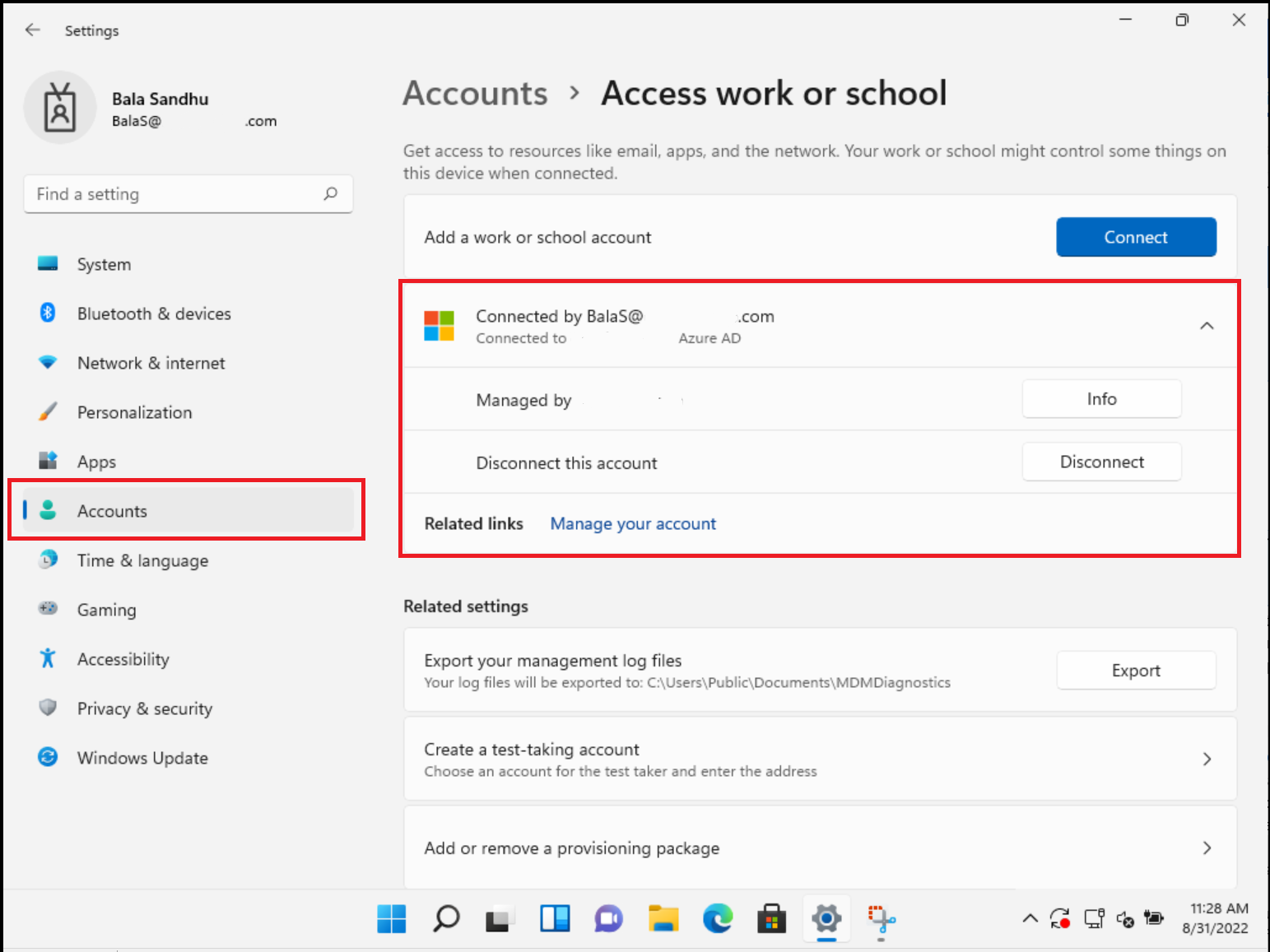
To verify whether a device is joined to your Microsoft Entra ID, review the Access work or school dialog on your Windows device found in Settings > Accounts. The dialog should indicate that you're connected to Microsoft Entra ID, and provides information about areas managed by your IT staff.
Next steps
- For more information about managing devices, see Managing device identities.
- What is Microsoft Intune?
- Overview of Windows Autopilot
- Passwordless authentication options for Microsoft Entra ID
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for