Tutorial: Microsoft Entra SSO integration with a GitHub Enterprise Cloud Organization
In this tutorial, you'll learn how to integrate a GitHub Enterprise Cloud Organization with Microsoft Entra ID. When you integrate a GitHub Enterprise Cloud Organization with Microsoft Entra ID, you can:
- Control in Microsoft Entra ID who has access to your GitHub Enterprise Cloud Organization.
- Manage access to your GitHub Enterprise Cloud Organization in one central location.
Prerequisites
To get started, you need the following items:
- A Microsoft Entra subscription. If you don't have a subscription, you can get a free account.
- A GitHub organization created in GitHub Enterprise Cloud, which requires the GitHub Enterprise billing plan.
Scenario description
In this tutorial, you configure and test Microsoft Entra single sign-on in a test environment.
GitHub supports SP initiated SSO.
GitHub supports Automated user provisioning (organization invitations).
Adding GitHub from the gallery
To configure the integration of GitHub into Microsoft Entra ID, you need to add GitHub from the gallery to your list of managed SaaS apps.
- Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
- Browse to Identity > Applications > Enterprise applications > New application.
- In the Add from the gallery section, type GitHub in the search box.
- Select GitHub Enterprise Cloud - Organization from results panel and then add the app. Wait a few seconds while the app is added to your tenant.
Alternatively, you can also use the Enterprise App Configuration Wizard. In this wizard, you can add an application to your tenant, add users/groups to the app, assign roles, as well as walk through the SSO configuration as well. Learn more about Microsoft 365 wizards.
Configure and test Microsoft Entra SSO for GitHub
Configure and test Microsoft Entra SSO with GitHub using a test user called B.Simon. For SSO to work, you need to establish a link relationship between a Microsoft Entra user and the related user in GitHub.
To configure and test Microsoft Entra SSO with GitHub, perform the following steps:
- Configure Microsoft Entra SSO - to enable your users to use this feature.
- Create a Microsoft Entra test user - to test Microsoft Entra single sign-on with B.Simon.
- Assign the Microsoft Entra test user - to enable B.Simon to use Microsoft Entra single sign-on.
- Configure GitHub SSO - to configure the single sign-on settings on application side.
- Create GitHub test user - to have a counterpart of B.Simon in GitHub that is linked to the Microsoft Entra representation of user.
- Test SSO - to verify whether the configuration works.
Configure Microsoft Entra SSO
Follow these steps to enable Microsoft Entra SSO.
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
Browse to Identity > Applications > Enterprise applications > GitHub > Single sign-on.
On the Select a single sign-on method page, select SAML.
On the Set up single sign-on with SAML page, click the pencil icon for Basic SAML Configuration to edit the settings.
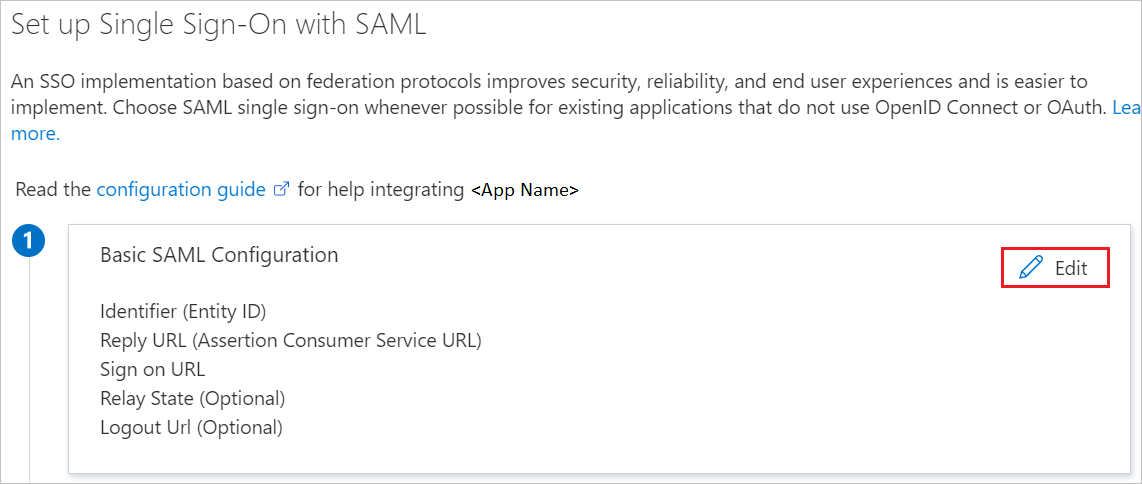
On the Basic SAML Configuration section, enter the values for the following fields:
a. In the Identifier (Entity ID) text box, type a URL using the following pattern:
https://github.com/orgs/<Organization ID>b. In the Reply URL text box, type a URL using the following pattern:
https://github.com/orgs/<Organization ID>/saml/consumec. In the Sign on URL text box, type a URL using the following pattern:
https://github.com/orgs/<Organization ID>/ssoNote
Please note that these are not the real values. You have to update these values with the actual Identifier,Reply URL and Sign on URL. Here we suggest you to use the unique value of string in the Identifier. Go to GitHub Admin section to retrieve these values.
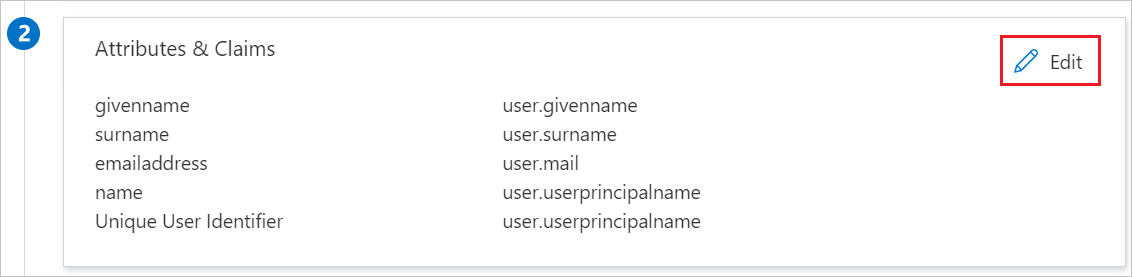
Your GitHub application expects the SAML assertions in a specific format, which requires you to add custom attribute mappings to your SAML token attributes configuration. The following screenshot shows the list of default attributes, where as Unique User Identifier (Name ID) is mapped with user.userprincipalname. GitHub application expects Unique User Identifier (Name ID) to be mapped with user.mail, so you need to edit the attribute mapping by clicking on Edit icon and change the attribute mapping.
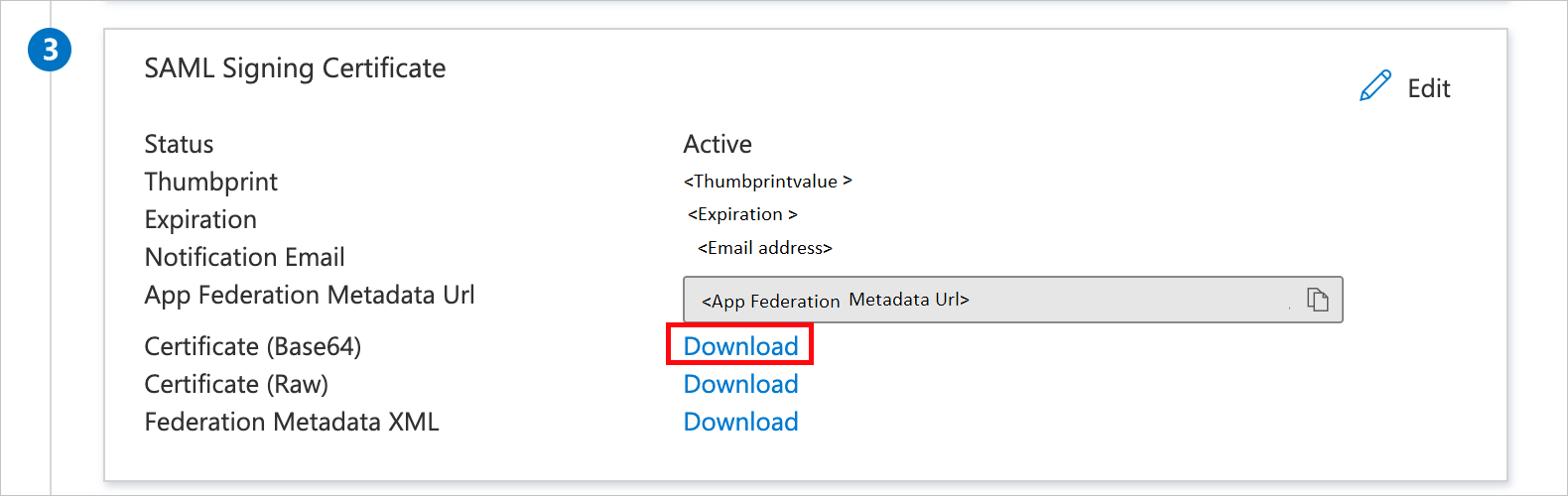
On the Set up Single Sign-On with SAML page, in the SAML Signing Certificate section, click Download to download the Certificate (Base64) from the given options as per your requirement and save it on your computer.
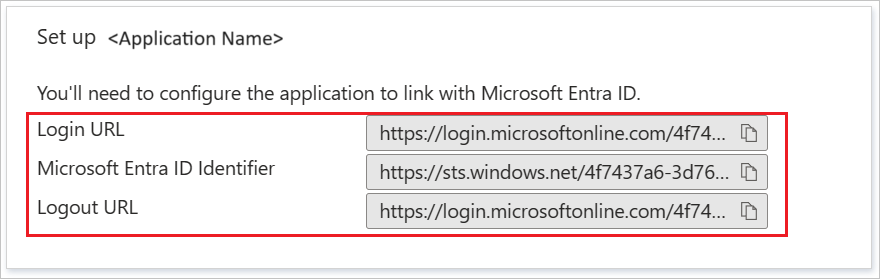
On the Set up GitHub section, copy the appropriate URL(s) as per your requirement.
Create a Microsoft Entra test user
In this section, you'll create a test user called B.Simon.
- Sign in to the Microsoft Entra admin center as at least a User Administrator.
- Browse to Identity > Users > All users.
- Select New user > Create new user, at the top of the screen.
- In the User properties, follow these steps:
- In the Display name field, enter
B.Simon. - In the User principal name field, enter the username@companydomain.extension. For example,
B.Simon@contoso.com. - Select the Show password check box, and then write down the value that's displayed in the Password box.
- Select Review + create.
- In the Display name field, enter
- Select Create.
Assign the Microsoft Entra test user
In this section, you'll enable B.Simon to use single sign-on by granting access to GitHub.
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
Browse to Identity > Applications > Enterprise applications > GitHub.
In the app's overview page, find the Manage section and select Users and groups.
Select Add user, then select Users and groups in the Add Assignment dialog.
In the Users and groups dialog, select B.Simon from the Users list, then click the Select button at the bottom of the screen.
If you are expecting a role to be assigned to the users, you can select it from the Select a role dropdown. If no role has been set up for this app, you see "Default Access" role selected.
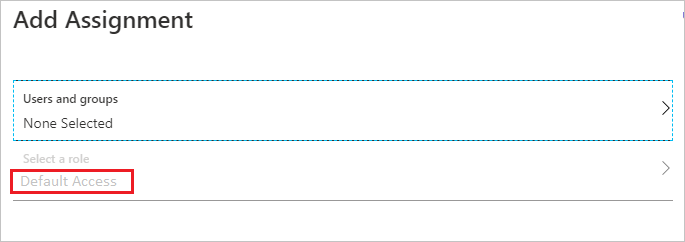
In the Add Assignment dialog, click the Assign button.
Configure GitHub SSO
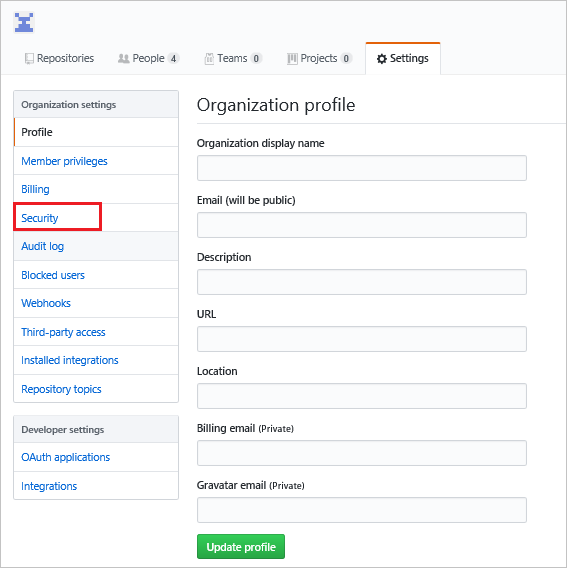
In a different web browser window, sign into your GitHub organization site as an administrator.
Navigate to Settings and click Security.
Check the Enable SAML authentication box, revealing the Single Sign-on configuration fields, perform the following steps:
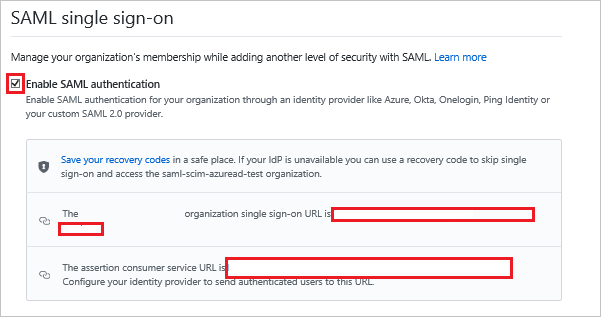
a. Copy single sign-on URL value and paste this value into the Sign on URL text box in the Basic SAML Configuration.
b. Copy assertion consumer service URL value and paste this value into the Reply URL text box in the Basic SAML Configuration.
Configure the following fields:
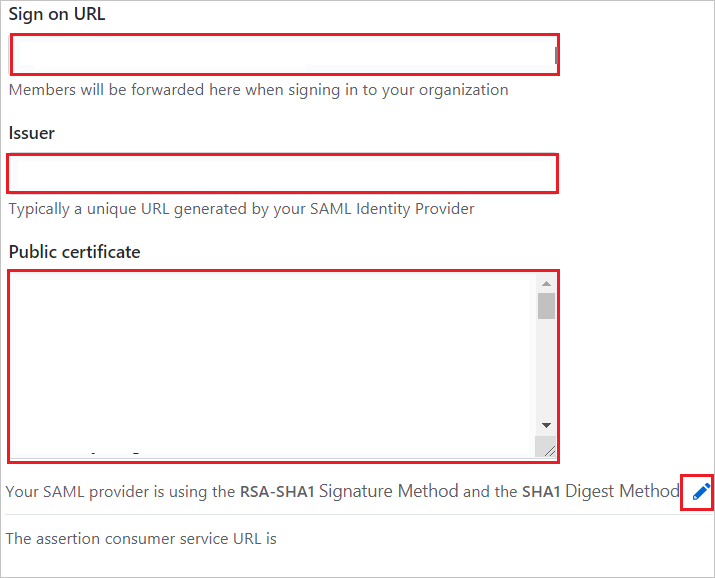
a. In the Sign on URL textbox, paste Login URL value which you copied previously.
b. In the Issuer textbox, paste Microsoft Entra Identifier value which you copied previously.
c. Open the downloaded certificate from Azure portal in notepad, paste the content into the Public Certificate textbox.
d. Click on Edit icon to edit the Signature Method and Digest Method from RSA-SHA1 and SHA1 to RSA-SHA256 and SHA256 as shown below.
e. Update the assertion consumer service URL (Reply URL) from the default URL so that it the URL in GitHub matches the URL in the Azure app registration.

Click on Test SAML configuration to confirm that no validation failures or errors during SSO.
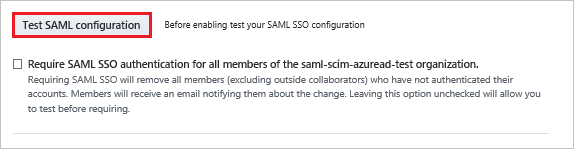
Click Save
Note
Single sign-on in GitHub authenticates to a specific organization in GitHub and does not replace the authentication of GitHub itself. Therefore, if the user's github.com session has expired, you may be asked to authenticate with GitHub's ID/password during the single sign-on process.
Create GitHub test user
The objective of this section is to create a user called Britta Simon in GitHub. GitHub supports automatic user provisioning, which is by default enabled. You can find more details here on how to configure automatic user provisioning.
If you need to create user manually, perform following steps:
Log in to your GitHub company site as an administrator.
Click People.
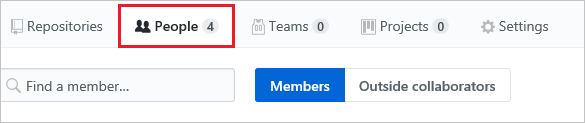
Click Invite member.
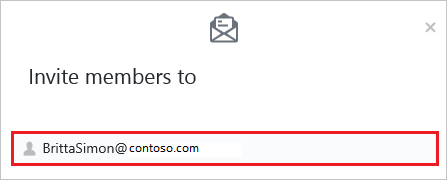
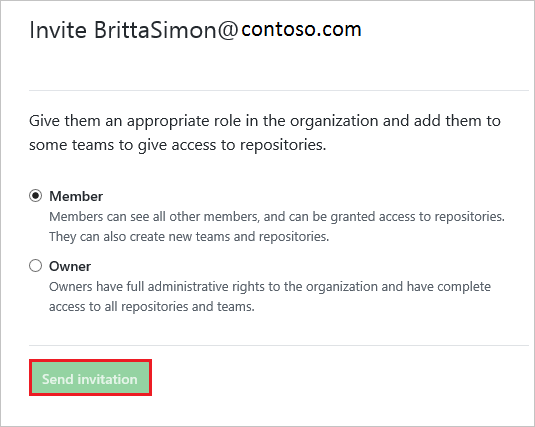
On the Invite member dialog page, perform the following steps:
a. In the Email textbox, type the email address of Britta Simon account.

b. Click Send Invitation.
Note
The Microsoft Entra account holder will receive an email and follow a link to confirm their account before it becomes active.
Test SSO
In this section, you test your Microsoft Entra single sign-on configuration with following options.
Click on Test this application, this will redirect to GitHub Sign-on URL where you can initiate the login flow.
Go to GitHub Sign-on URL directly and initiate the login flow from there.
You can use Microsoft My Apps. When you click the GitHub tile in the My Apps, this will redirect to GitHub Sign-on URL. For more information about the My Apps, see Introduction to the My Apps.
Next steps
Once you configure GitHub you can enforce Session control, which protects exfiltration and infiltration of your organization’s sensitive data in real time. Session control extends from Conditional Access. Learn how to enforce session control with Microsoft Defender for Cloud Apps.
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for