Managed identities for Azure SignalR Service
In Azure SignalR Service, you can use a managed identity from Microsoft Entra ID to:
- Obtain access tokens.
- Access secrets in Azure Key Vault.
The service supports only one managed identity. You can create either a system-assigned or a user-assigned identity. A system-assigned identity is dedicated to your Azure SignalR Service instance and is deleted when you delete the instance. A user-assigned identity is managed independently of your Azure SignalR Service resource.
This article shows you how to create a managed identity for Azure SignalR Service and how to use it in serverless scenarios.
Prerequisites
To use a managed identity, you must have the following items:
- An Azure subscription. If you don't have an Azure subscription, create a free account before you begin.
- An Azure SignalR Service resource.
- Upstream resources that you want to access, such as an Azure Key Vault resource.
- An Azure Functions app (function app).
Add a managed identity to Azure SignalR Service
You can add a managed identity to Azure SignalR Service in the Azure portal or the Azure CLI. This article shows you how to add a managed identity to Azure SignalR Service in the Azure portal.
Add a system-assigned identity
To add a system-assigned managed identity to your Azure SignalR Service instance:
In the Azure portal, browse to your Azure SignalR Service instance.
Select Identity.
On the System assigned tab, switch Status to On.

Select Save.
Select Yes to confirm the change.
Add a user-assigned identity
To add a user-assigned identity to your Azure SignalR Service instance, you need to create the identity and then add it to the service.
Create a user-assigned managed identity resource according to these instructions.
In the Azure portal, browse to your Azure SignalR Service instance.
Select Identity.
On the User assigned tab, select Add.
On the User assigned managed identities dropdown menu, select the identity.
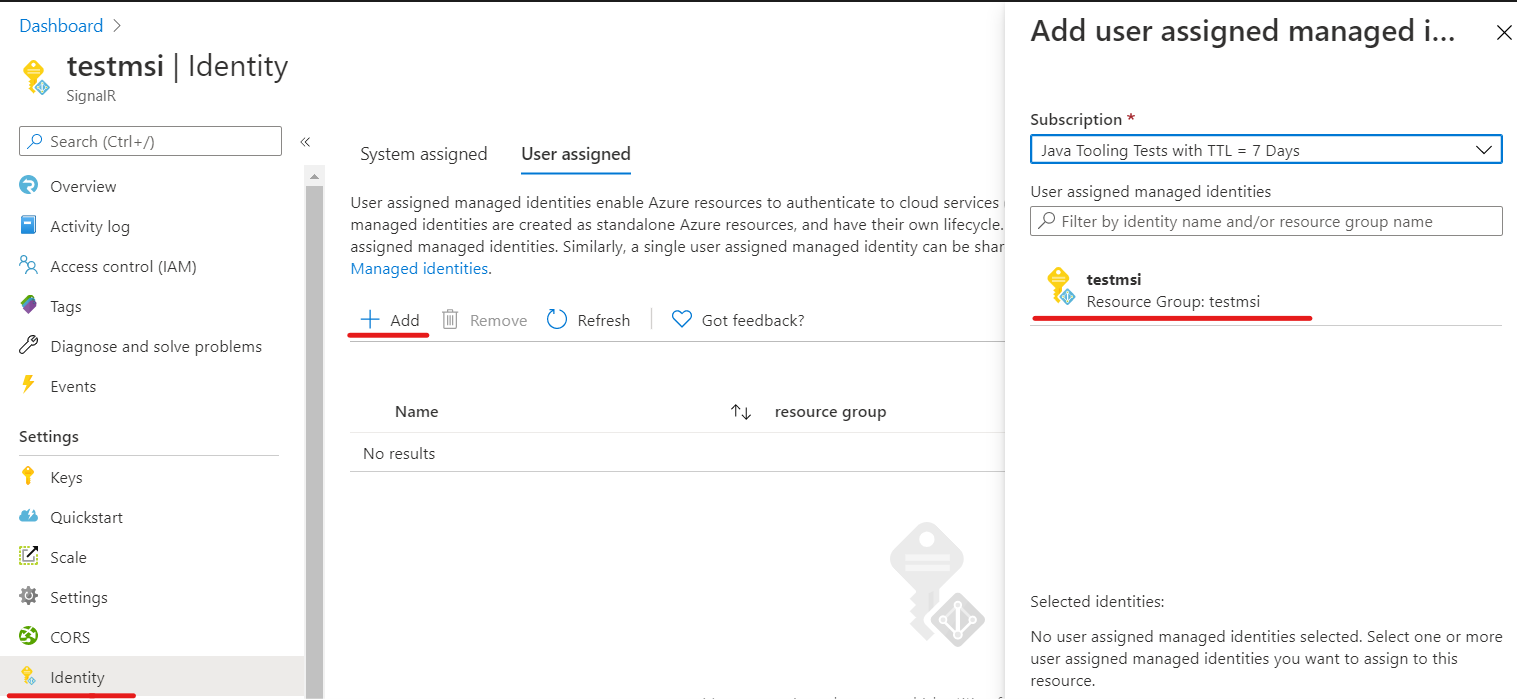
Select Add.
Use a managed identity in serverless scenarios
Azure SignalR Service is a fully managed service. It uses a managed identity to obtain an access token. In serverless scenarios, the service adds the access token into the Authorization header in an upstream request.
Enable managed identity authentication in upstream settings
After you add a system-assigned identity or user-assigned identity to your Azure SignalR Service instance, you can enable managed identity authentication in the upstream endpoint settings:
In the Azure portal, browse to your Azure SignalR Service instance.
Select Settings from the menu.
Select the Serverless service mode.
In the Add an upstream URL pattern text box, enter the upstream endpoint URL pattern. See URL template settings.
Select Add one Upstream Setting, and then select any asterisk.
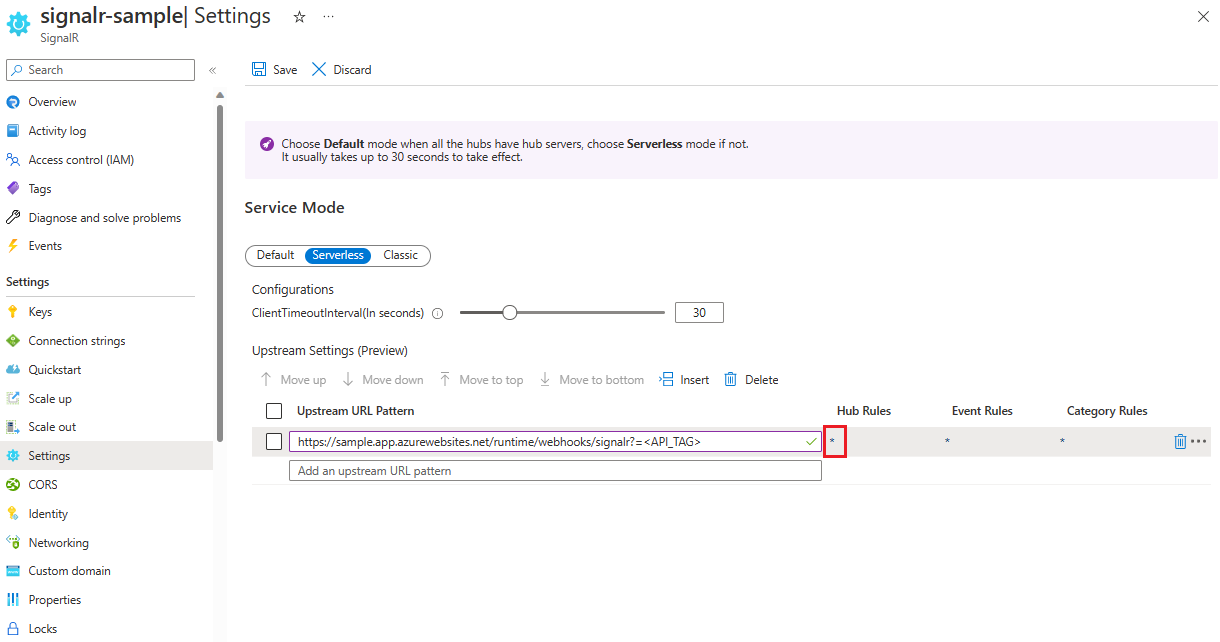
In Upstream Settings, configure your upstream endpoint settings.
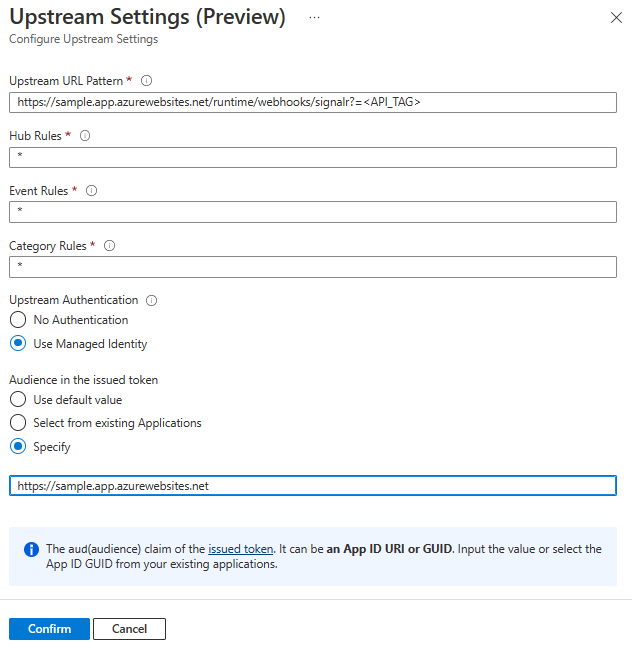
In the managed identity authentication settings, for Audience in the issued token, you can specify the target resource. The resource will become an
audclaim in the obtained access token, which can be used as a part of validation in your upstream endpoints. The resource can be in one of the following formats:- Application (client) ID of the service principal.
- Application ID URI of the service principal.
Important
Using empty resource actully acquire a token targets to Microsoft Graph. As today, Microsoft Graph enables token encryption so it's not available for application to authenticate the token other than Microsoft Graph. In common practice, you should always create a service principal to represent your upstream target. And set the Application ID or Application ID URI of the service principal you've created.
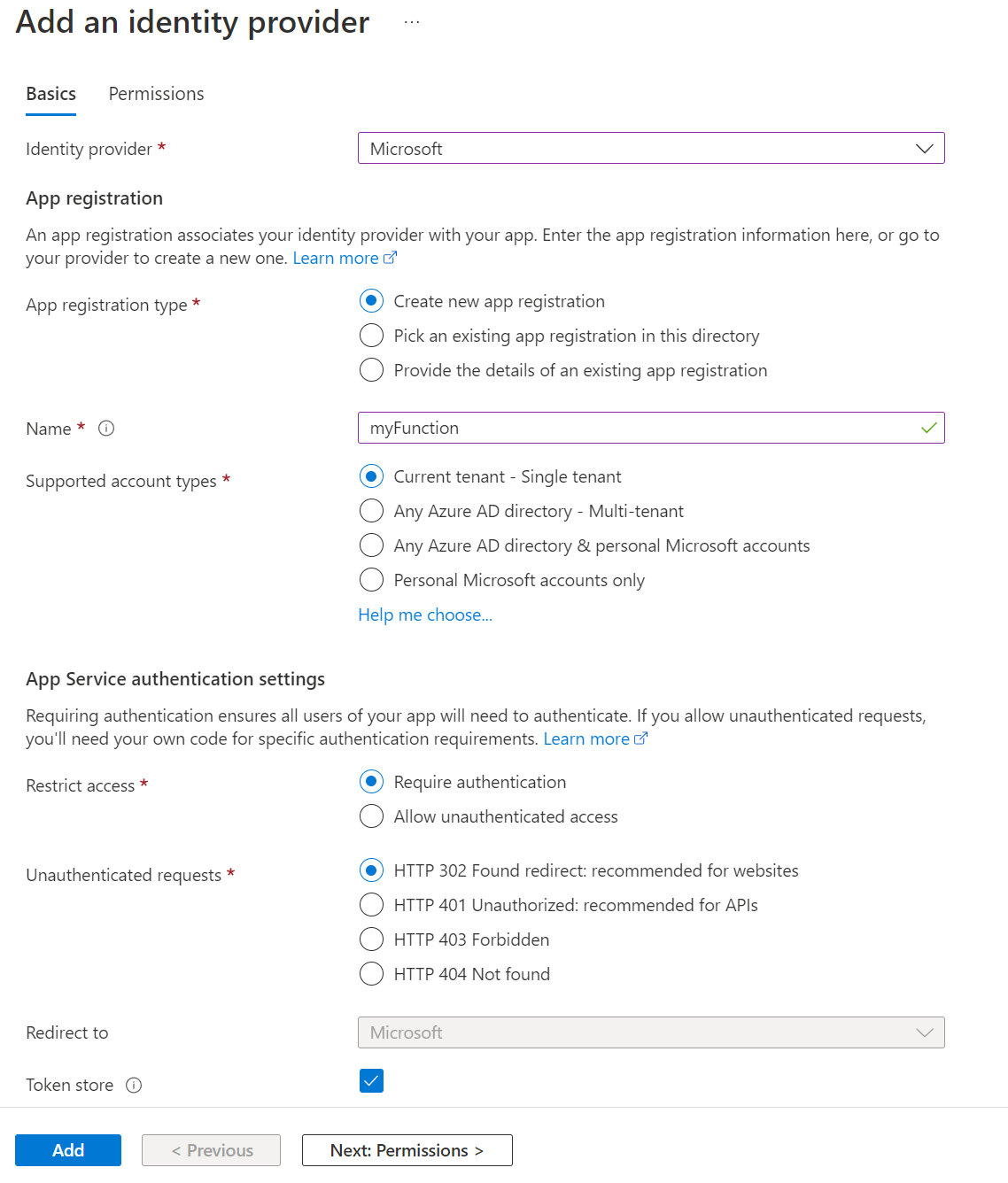
Authentication in a function app
You can easily set access validation for a function app without code changes by using the Azure portal:
In the Azure portal, go to the function app.
Select Authentication from the menu.
Select Add identity provider.
On the Basics tab, in the Identity provider dropdown list, select Microsoft.
In Action to take when request is not authenticated, select Log in with Microsoft Entra ID.
The option to create a new registration is selected by default. You can change the name of the registration. For more information on enabling a Microsoft Entra provider, see Configure your App Service or Azure Functions app to use a Microsoft Entra ID sign-in.
Go to Azure SignalR Service and follow the steps to add a system-assigned identity or user-assigned identity.
In Azure SignalR Service, go to Upstream settings, and then select Use Managed Identity and Select from existing Applications. Select the application that you created previously.
After you configure these settings, the function app will reject requests without an access token in the header.
Validate access tokens
If you're not using WebApp or Azure Function, you can also validate the token.
The token in the Authorization header is a Microsoft identity platform access token.
To validate access tokens, your app should also validate the audience and the signing tokens. These tokens need to be validated against the values in the OpenID discovery document. For an example, see the tenant-independent version of the document.
The Microsoft Entra middleware has built-in capabilities for validating access tokens. You can browse through the Microsoft identity platform code samples to find one in the language of your choice.
Libraries and code samples that show how to handle token validation are available. Several open-source partner libraries are also available for JSON Web Token (JWT) validation. There's at least one option for almost every platform and language. For more information about Microsoft Entra authentication libraries and code samples, see Microsoft identity platform authentication libraries.
Use a managed identity for a Key Vault reference
Azure SignalR Service can access Key Vault to get secrets by using the managed identity.
- Add a system-assigned identity or user-assigned identity to your Azure SignalR Service instance.
- Grant secret read permission for the managed identity in the access policies in Key Vault. See Assign a Key Vault access policy by using the Azure portal.
Currently, you can use this feature to reference a secret in the upstream URL pattern.
Next steps
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for