Review remediation actions in the Action center
As threats are detected, remediation actions come into play. Depending on the particular threat and how your security settings are configured, remediation actions might be taken automatically or only upon approval. Examples of remediation actions include stopping a process from running or removing a scheduled task.
All remediation actions are tracked in the Action center.
This article describes:
How to use the Action center
Go to the Microsoft Defender portal (https://security.microsoft.com) and sign in.
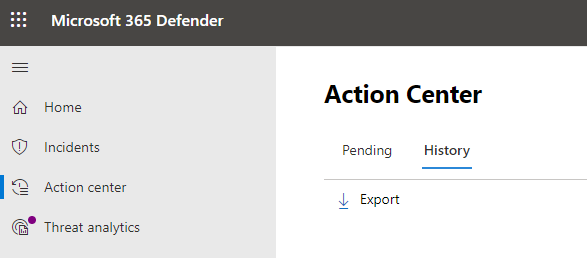
In the navigation pane, choose Action center.
Select the Pending tab to view and approve (or reject) any pending actions. Actions can arise from antivirus/antimalware protection, automated investigations, manual response activities, or live response sessions.
Select the History tab to view a list of completed actions.
Remediation actions
Defender for Business includes several remediation actions. These actions include manual response actions, actions following automated investigation, and live response actions.
The following table lists remediation actions that are available.
| Source | Actions |
|---|---|
| Automatic attack disruption | - Contain a device - Contain a user - Disable a user account |
| Automated investigations | - Quarantine a file - Remove a registry key - Kill a process - Stop a service - Disable a driver - Remove a scheduled task |
| Manual response actions | - Run antivirus scan - Isolate a device - Add an indicator to block or allow a file |
| Live response | - Collect forensic data - Analyze a file - Run a script - Send a suspicious entity to Microsoft for analysis - Remediate a file - Proactively hunt for threats |
Next steps
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for