API 자격 증명 및 자격 증명 관리자 정보
적용 대상: 모든 API Management 계층
백 엔드 API에 대한 액세스를 관리하는 데 도움이 되도록 API Management 인스턴스에는 자격 증명 관리자가 포함되어 있습니다. 자격 증명 관리자를 사용하여 API Management 인스턴스에서 API 자격 증명에 대한 액세스를 관리, 저장 및 제어합니다.
참고 항목
- 현재, 자격 증명 관리자를 사용하여 백 엔드 OAuth 2.0 API에 대한 연결(이전의 권한 부여)을 구성하고 관리할 수 있습니다.
- 자격 증명 관리자에는 호환성이 손상되는 변경이 도입되지 않았습니다. OAuth 2.0 자격 증명 공급자 및 연결은 기존 API Management 권한 부여 API 및 리소스 공급자를 사용합니다.
OAuth 2.0 API에 대한 관리형 연결
자격 증명 관리자를 사용하면 OAuth 2.0을 사용하는 하나 이상의 백 엔드 또는 SaaS 서비스에서 사용자, 그룹 및 서비스 주체를 인증하고 권한을 부여하는 프로세스를 크게 간소화할 수 있습니다. API Management의 자격 증명 관리자를 사용하여 코드 한 줄도 작성하지 않고 OAuth 2.0을 쉽게 구성하고, 동의하고, 토큰을 획득하고, 자격 증명 저장소에 토큰을 캐시하고, 토큰을 새로 고칩니다. 액세스 정책을 사용하여 API Management 인스턴스, 서비스 주체, 사용자 또는 그룹에 인증을 위임합니다. OAuth 2.0에 대한 배경 정보는 Microsoft ID 플랫폼 및 OAuth 2.0 인증 코드 흐름을 참조하세요.
이 기능을 사용하면 구독 키 사용 여부에 관계없이 API를 노출하고, 백 엔드 서비스에 OAuth 2.0 권한 부여를 사용하고, 서비스 통합을 통해 보안 기능을 강화, 구현 및 유지 관리하는 데 드는 개발 비용을 줄일 수 있습니다.
사용 사례 예
API Management에서 관리되는 OAuth 연결을 사용하여 고객은 OAuth 2.0을 사용하는 SaaS 공급자 또는 백 엔드 서비스에 쉽게 연결할 수 있습니다. 다음 몇 가지 예를 참조하세요.
저장된 권한 부여 토큰 및 프록시 요청을 연결하여 SaaS 백 엔드에 쉽게 연결
나중에 변환 논리를 적용하는 SaaS 백 엔드에 요청을 보낼 수 있는 권한 부여 토큰을 연결하여 Azure App Service 웹앱 또는 Azure Functions 백 엔드로 요청 프록시
페더레이션을 쉽게 수행하기 위해 여러 액세스 토큰을 연결하여 GraphQL 페더레이션 백 엔드에 대해 요청 프록시
검색 토큰 엔드포인트를 노출하고, 캐시된 토큰을 획득하고, 콘솔 앱 또는 Kubernetes 디먼과 같은 모든 컴퓨팅에서 사용자를 대신하여 SaaS 백 엔드를 호출합니다. 지원되는 언어로 즐겨 찾는 SaaS SDK를 결합합니다.
여러 SaaS 백 엔드에 연결할 때 Azure Functions 무인 시나리오
Durable Functions는 SaaS 연결을 사용하여 Logic Apps에 더 가까워집니다.
OAuth 2.0 연결을 사용하면 API Management의 모든 API가 Logic Apps 사용자 지정 커넥터 역할을 할 수 있습니다.
자격 증명 관리자는 어떻게 작동하나요?
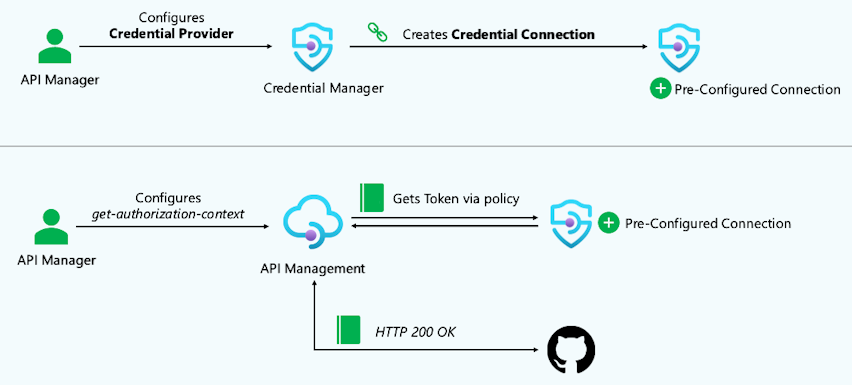
자격 증명 관리자의 토큰 자격 증명은 관리 및 런타임의 두 부분으로 구성됩니다.
자격 증명 관리자의 관리 부분은 OAuth 2.0 토큰에 대한 자격 증명 공급자를 설정 및 구성하고, ID 공급자에 대한 동의 흐름을 사용하도록 설정하고, 자격 증명에 액세스하기 위해 자격 증명 공급자에 대한 하나 이상의 연결을 설정하는 작업을 담당합니다. 자세한 내용은 연결 관리를 참조하세요.
런타임 부분은
get-authorization-context정책을 사용하여 연결의 액세스 및 새로 고침 토큰을 가져오고 저장합니다. 호출이 API Management로 들어오고get-authorization-context정책이 실행되면 먼저 기존 권한 부여 토큰이 유효한지 유효성을 검사합니다. 권한 부여 토큰이 만료된 경우 API Management는 OAuth 2.0 흐름을 사용하여 ID 공급자에서 저장된 토큰을 새로 고칩니다. 그런 다음, 액세스 토큰을 사용하여 백 엔드 서비스에 대한 액세스 권한을 부여합니다. 자세한 내용은 연결 런타임을 참조하세요.
자격 증명 관리자는 언제 사용해야 하나요?
다음은 자격 증명 관리자를 사용하는 세 가지 시나리오입니다.
구성 시나리오
자격 증명 공급자 및 연결을 구성한 후 API 관리자는 연결을 테스트할 수 있습니다. API 관리자는 인스턴스의 관리 ID를 사용하여 get-authorization-context 정책을 사용하도록 테스트 백 엔드 OAuth API를 구성합니다. 그런 다음, API 관리자는 테스트 API를 호출하여 연결을 테스트할 수 있습니다.
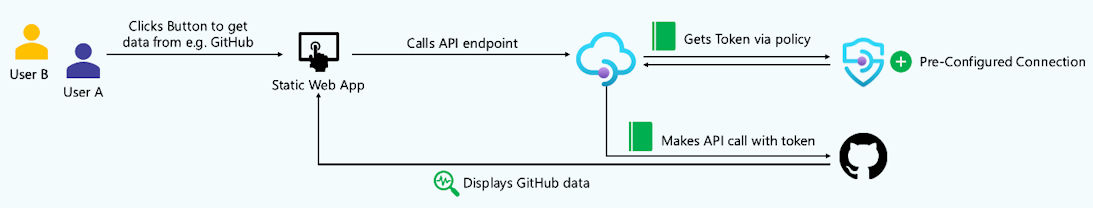
무인 시나리오
기본적으로 연결이 만들어지면 API Management 인스턴스의 관리 ID에 대한 액세스 정책 및 연결이 미리 구성됩니다. 이러한 연결을 사용하려면 다른 사용자가 정적 웹앱과 같은 클라이언트 애플리케이션에 로그인한 다음, API Management를 통해 노출된 백 엔드 API를 호출합니다. 이 호출을 수행하려면 get-authorization-context 정책을 사용하여 연결이 적용됩니다. API 호출은 사용자 컨텍스트와 관련이 없는 미리 구성된 연결을 사용하므로 모든 사용자에게 동일한 데이터가 반환됩니다.
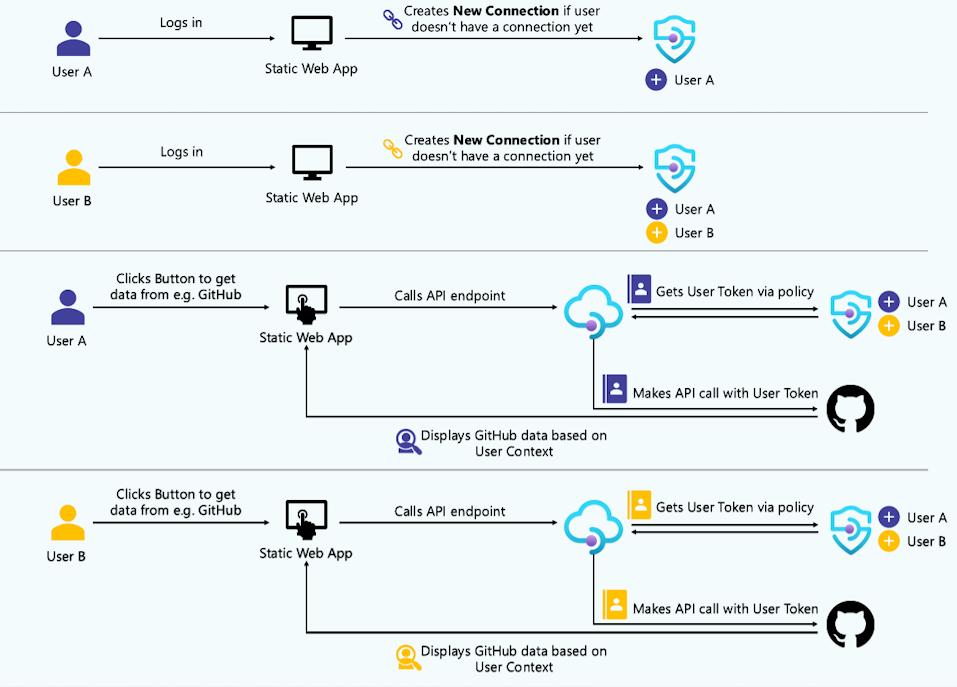
참석(사용자 위임) 시나리오
사용자 컨텍스트가 필요한 백 엔드 SaaS API를 호출하는 정적 웹앱과 같은 클라이언트 애플리케이션의 사용자를 위한 간소화된 인증 환경을 사용하도록 설정하려면 Microsoft Entra 사용자 또는 그룹 ID를 대신하여 연결에 대한 액세스를 사용하도록 설정할 수 있습니다. 이 경우 구성된 사용자는 로그인하고 동의를 한 번만 제공하면 되며, 그 후에는 API Management 인스턴스가 연결을 만들고 관리합니다. API Management는 외부 서비스로 전달될 수신 호출을 받으면 연결에서 요청으로 액세스 토큰을 연결합니다. 이는 API 요청 및 응답이 개인(예: 사용자별 프로필 정보 검색)을 기준으로 하는 경우에 적합합니다.
자격 증명 관리자를 구성하는 방법
요구 사항
API Management 인스턴스에 대해 관리형 시스템 할당 ID를 사용하도록 설정해야 합니다.
API Management 인스턴스는 포트 443(HTTPS)에서 인터넷에 대한 아웃바운드 연결이 있어야 합니다.
가용성
모든 API Management 서비스 계층
자체 호스팅 게이트웨이에서 지원되지 않음
소버린 클라우드 또는 다음 지역에서 지원되지 않음: australiacentral, australiacentral2, indiacentral
단계별 예제
보안 고려 사항
액세스 토큰 및 기타 비밀(예: 클라이언트 비밀)은 봉투 암호화로 암호화되고 내부 다중 테넌트 스토리지에 저장됩니다. 데이터는 데이터당 고유한 키를 사용하여 AES-128로 암호화됩니다. 이러한 키는 Azure Key Vault에 저장되고 매달 순환되는 마스터 인증서를 사용하여 비대칭적으로 암호화됩니다.
제한
| 리소스 | 제한 |
|---|---|
| 서비스 인스턴스당 최대 자격 증명 공급자 수 | 1,000 |
| 자격 증명 공급자당 최대 연결 수 | 10,000 |
| 연결당 최대 액세스 정책 수 | 100 |
| 연결당 분당 최대 권한 부여 요청 수 | 250 |
질문과 대답(FAQ)
액세스 토큰은 언제 새로 고쳐지나요?
형식 권한 부여 코드 연결의 경우 액세스 토큰은 다음과 같이 새로 고쳐집니다. 런타임에 get-authorization-context 정책이 실행되면 API Management는 저장된 액세스 토큰이 유효한지 확인합니다. 토큰이 만료되었거나 만료에 가까운 경우 API Management는 새로 고침 토큰을 사용하여 구성된 ID 공급자에서 새 액세스 토큰 및 새 새로 고침 토큰을 가져옵니다. 새로 고침 토큰이 만료되면 오류가 throw되고 연결이 다시 인증되어야 작동합니다.
ID 공급자에서 클라이언트 암호가 만료되면 어떻게 되나요?
런타임에 API Management는 새 토큰을 가져올 수 없으며 오류가 발생합니다.
연결이 인증 코드 형식인 경우 자격 증명 공급자 수준에서 클라이언트 비밀을 업데이트해야 합니다.
연결이 클라이언트 자격 증명 형식인 경우 연결 수준에서 클라이언트 비밀을 업데이트해야 합니다.
이 기능은 VNet 내에서 실행되는 API Management를 사용하여 지원되나요?
예, 포트 443의 아웃바운드 연결이 AzureConnectors 서비스 태그에 사용하도록 설정되면 됩니다. 자세한 내용은 가상 네트워크 구성 참조를 참조하세요.
자격 증명 공급자가 삭제되면 어떻게 되나요?
모든 기본 연결 및 액세스 정책도 삭제됩니다.
API Management에서 액세스 토큰을 캐시하나요?
클래식 및 v2 서비스 계층에서 액세스 토큰은 토큰 만료 시간 3분 전까지 API Management 인스턴스에 의해 캐시됩니다. 액세스 토큰이 3분 미만이 경과되면 만료되는 경우 캐시된 시간은 액세스 토큰이 만료될 때까지입니다.
액세스 토큰은 소비 계층에 캐시되지 않습니다.
관련 콘텐츠
- 연결에 대한 자격 증명 공급자 구성
- Microsoft Graph API 또는 GitHub API에 대한 연결 구성 및 사용
- 사용자가 위임한 액세스에 대한 연결 구성
- 자격 증명 공급자에 대한 여러 연결 구성