사용자 할당 기반 청구, 기본 액세스 수준 및 일일 청구 - Sprint 158 업데이트
Azure DevOps의 Sprint 158 업데이트에서는 사용자 할당 기반 청구를 추가했습니다. 이 기능으로 많은 Basic 또는 Basic + Test Plan 라이선스가 사용자를 추가 또는 제거할 때 변경됩니다. 즉, 사용 중인 라이선스에 대해서만 비용을 지불하게 됩니다. 또한 조직에 새 사용자를 추가하여 전체 기본 액세스 또는 제한된/무료 이해 관계자 액세스를 가져올지 여부를 선택할 수 있는 새 설정이 추가되었습니다.
또한 월간에서 일간 청구로 전환했습니다. 즉, 사용자에게 유료 액세스를 몇 주 또는 며칠 동안만 부여할 경우 월 전체가 아닌 유료 액세스가 할당된 시간에 대해서만 결제하게 됩니다.
자세한 내용은 아래 기능 목록을 확인하세요.
Azure DevOps의 새로운 기능
기능
일반:
Azure Boards:
Azure Repos:
- 서비스 계정 기반 인증을 사용하여 AKS에 연결
- 끌어오기 요청의 Markdown 파일 미리 보기 병렬 차이
- 수동 빌드에 대한 빌드 정책 만료
- 커밋 작성자 메일에 기반한 커밋 차단을 위한 정책 추가
Azure Pipelines:
- 재시도 실패 단계
- YAML 파이프라인의 승인을 위한 고급 기능
- Azure Pipelines의 컨테이너 구조 테스트 지원
- Flaky 버그 관리 및 해결 방법
- Slack 및 Microsoft Teams용 Azure Pipelines 앱의 고급 기능
- 호스트된 파이프라인 이미지 업데이트
- Open Policy Agent 설치 프로그램 작업
- 릴리스 파이프라인용 파이프라인 데코레이터
Azure Test Plans:
보고:
Wiki:
일반
사용자 할당 기반의 청구 및 기본 액세스 수준
사용자 할당 기반 청구
이 업데이트를 통해 사용자 할당 기반 청구를 추가했습니다. 조직에서 할당할 수 있는 유료 기본 또는 기본 + 테스트 계획 라이선스 수를 늘리거나 줄이는 대신, 이제 사용자를 추가 또는 제거하거나 액세스 수준을 변경할 때 자동으로 수행됩니다. 즉, 사용 중인 것보다 더 많은 라이선스에 대한 비용을 지불하지 않으며 액세스 수준 할당을 훨씬 쉽게 자동화할 수 있습니다. 예를 들어 팀에 자동으로 가입하는 새 사용자에게 할당되는 액세스 수준을 제어하는 그룹 규칙을 설정할 수 있었습니다. 그러나 과거에는 아직 사용자에게 할당되지 않은 추가 라이선스가 있는 경우에만 작동했으며, 부족 하면 그룹 규칙이 실패했습니다. 청구에 사용하는 Azure 구독이 활성 상태로 유지되는 한 이러한 유형의 오류는 더 이상 발생하지 않습니다.
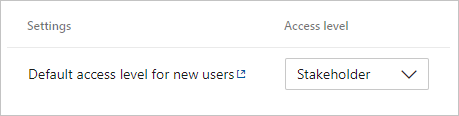
새 사용자의 기본 액세스 수준
또한 조직에 새 사용자를 추가하여 전체 기본 액세스 또는 제한된/무료 이해 관계자 액세스를 가져올지 여부를 선택할 수 있는 새 설정이 추가되었습니다. 과거에는 할당되지 않은 기본 라이선스를 사용할 수 있는 경우 새 사용자가 Basic을 받았지만, 그렇지 않은 경우 이해 관계자가 있었습니다. 모든 조직은 기본 액세스 수준을 이해 관계자로 설정하여 시작하므로 새 사용자에 대한 예기치 않은 요금이 발생하지 않습니다. 조직에서 일반적으로 할당되지 않은 추가 라이선스를 유지하여 프로젝트에 추가된 새 사용자가 전체 기본 액세스 권한을 얻은 경우 기본 액세스 수준을 기본으로 변경해야 합니다.
일일 청구
할당 기반 청구 변경의 일환으로 월별 청구에서 일일 청구로 전환했습니다. 이제 사용자에게 몇 주 또는 며칠 동안 유료 액세스 권한을 부여하는 경우 한 달이 아닌 유료 액세스 권한이 할당된 시간에 대해서만 요금을 지불합니다. 조직을 매월 청구에서 일별 청구로 전환하면 다음 Azure 청구서가 이전보다 낮아질 수 있습니다. 다음 달은 누적 된 일일 요금의 전체 달이되면 정상으로 돌아갑니다.
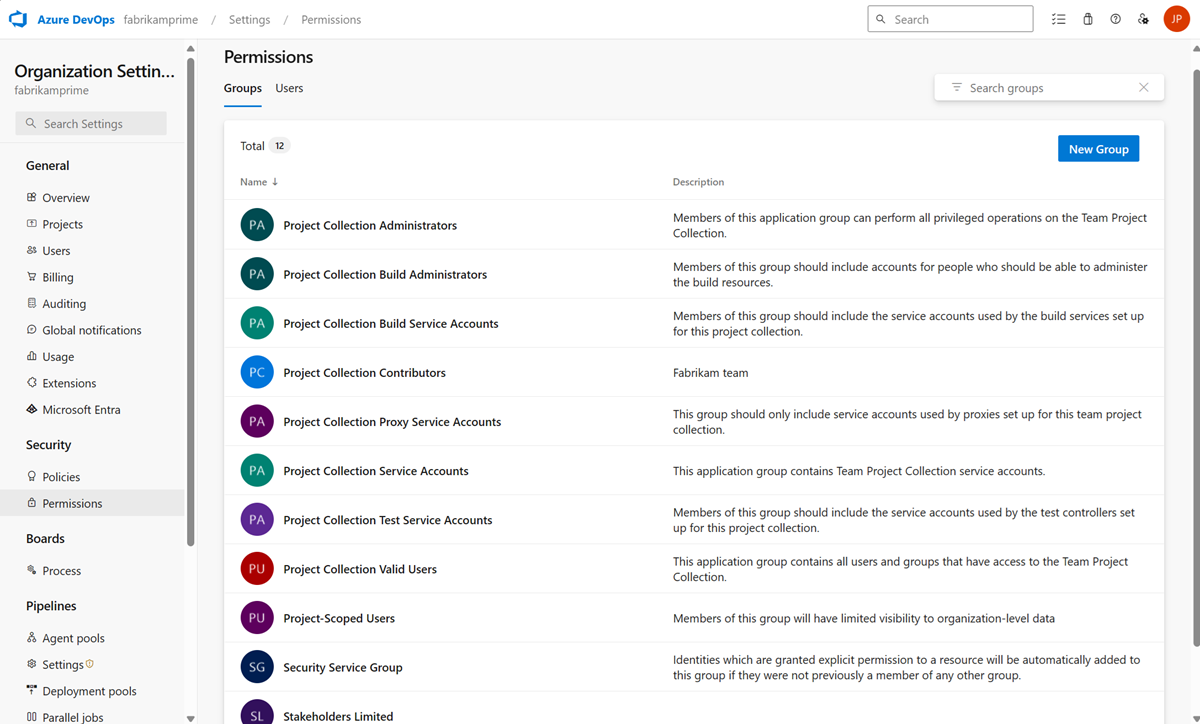
조직 및 프로젝트 사용 권한을 관리할 수 있는 새로운 UI
조직 및 프로젝트 권한 관리에 새로운 모양과 성능이 향상되었습니다. 이제 강제 페이지 새로 고침 없이 새 그룹 구성원이 추가될 때 목록에 표시됩니다. 조직 설정 살펴보고 살펴보세요.
Azure Boards
롤업 열의 사용자 지정 필드 지원
이제 사용자 지정 필드를 비롯한 모든 필드에서 롤업을 수행할 수 있습니다. 롤업 열을 추가할 때 빠른 목록에서 롤업 열을 선택할 수 있지만 기본 프로세스 템플릿의 일부가 아닌 숫자 필드를 롤업하려는 경우 다음과 같이 직접 구성할 수 있습니다.
- 백로그에서 "열 옵션"을 클릭합니다. 그런 다음 패널에서 "롤업 열 추가" 를 클릭하고 사용자 지정 롤업을 구성합니다.

- 진행률 표시줄과 합계 중에서 선택합니다.
- 작업 항목 유형 또는 백로그 수준을 선택합니다(일반적으로 백로그는 여러 작업 항목 유형을 집계합니다).
- 집계 유형을 선택합니다. 작업 항목 또는 합계의 수입니다. 합계의 경우 요약할 필드를 선택해야 합니다.
- 확인 단추를 사용하면 새 사용자 지정 열의 순서를 변경할 수 있는 열 옵션 패널로 돌아갑니다.
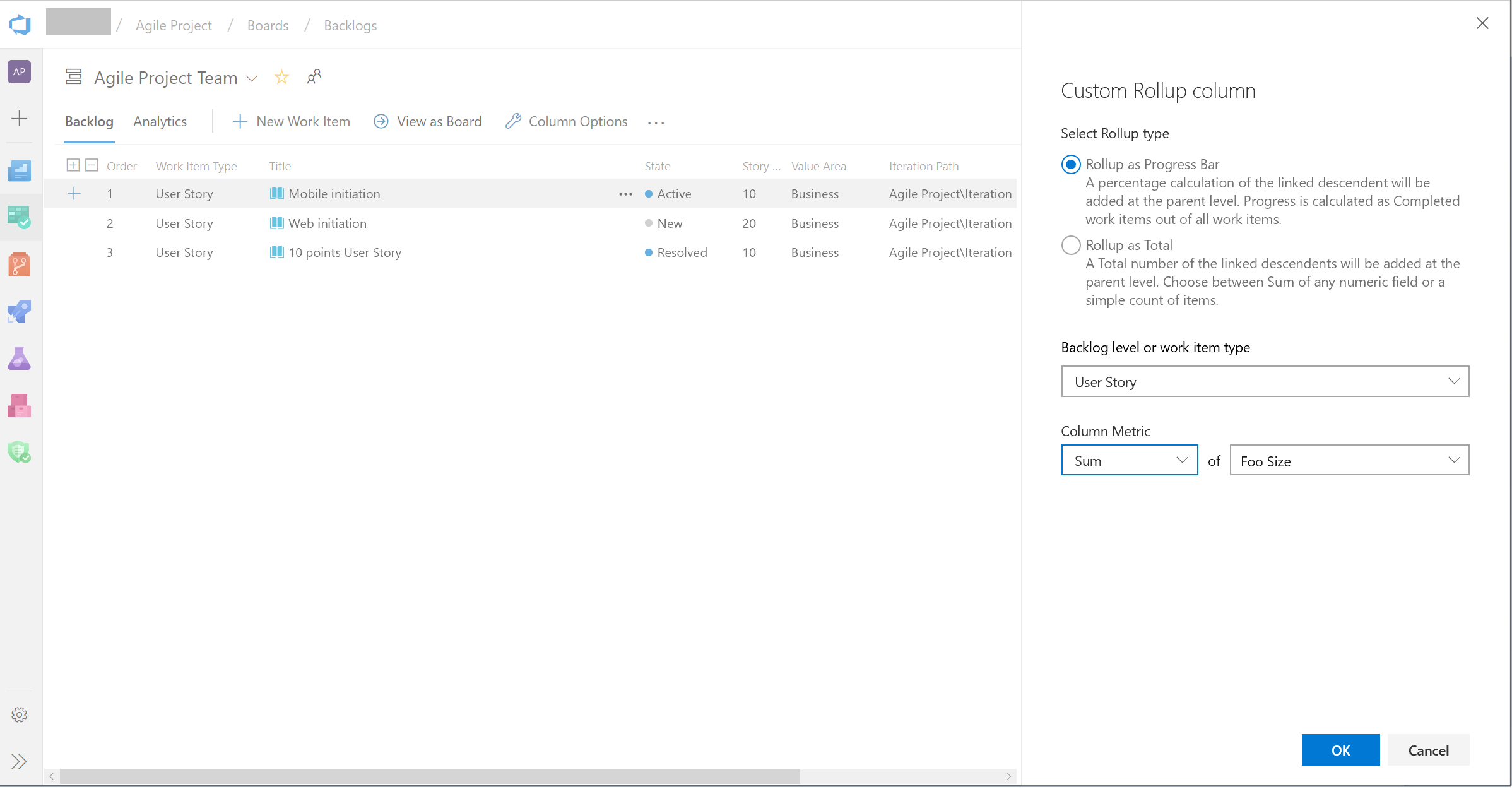
확인을 클릭한 후에는 사용자 지정 열을 편집할 수 없습니다. 변경해야 하는 경우 사용자 지정 열을 제거하고 원하는 대로 다른 열을 추가합니다.
조건에 기반한 작업 항목 폼에서 필드 숨기기의 새로운 규칙
작업 항목 양식에서 필드를 숨길 수 있도록 상속된 규칙 엔진에 새 규칙을 추가했습니다. 이 규칙은 사용자 그룹 멤버 자격에 따라 필드를 숨깁니다. 예를 들어 사용자가 "제품 소유자" 그룹에 속하는 경우 개발자 특정 필드를 숨길 수 있습니다. 자세한 내용은 여기 설명서를 참조하세요.
사용자 지정 작업 항목 알림 설정
사용자 또는 팀과 관련된 작업 항목을 최신 상태로 유지하는 것은 매우 중요합니다. 이는 팀이 공동 작업하고 프로젝트를 계속 진행하는 데 도움이 되며 모든 올바른 당사자가 참여하도록 합니다. 그러나 다양한 이해 관계자가 다양한 노력에 대해 서로 다른 수준의 투자를 하고 있으며, 작업 항목의 상태 따르는 능력에 반영되어야 한다고 생각합니다.
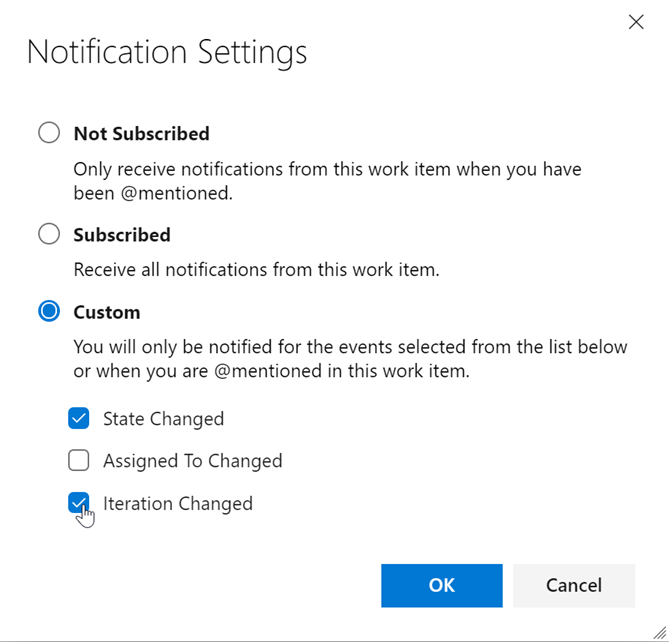
이전에는 작업 항목을 따르고 변경 내용에 대한 알림을 받으려면 작업 항목의 모든 변경 내용에 대한 메일 알림 받습니다. 피드백을 고려한 후에는 모든 이해 관계자가 작업 항목을 보다 유연하게 수행할 수 있도록 하고 있습니다. 이제 작업 항목의 오른쪽 위 모서리에 팔로우 단추 옆에 새 설정 단추가 표시됩니다. 그러면 다음 옵션을 구성할 수 있는 팝업으로 이동합니다.
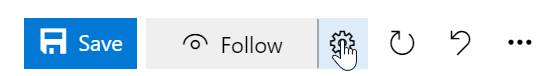
알림 설정 세 가지 알림 옵션 중에서 선택할 수 있습니다. 첫째, 구독을 완전히 취소할 수 있습니다. 둘째, 모든 작업 항목 변경에 대한 알림을 받을 수 있는 완전히 구독할 수 있습니다. 마지막으로, 상위 및 중요한 작업 항목 변경 이벤트 중 일부에 대한 알림을 받도록 선택할 수 있습니다. 하나 또는 세 가지 옵션 모두를 선택할 수 있습니다. 이렇게 하면 팀 구성원이 더 높은 수준에서 작업 항목을 따르고 모든 변경 내용에 주의를 빼앗기지 않습니다. 이 기능을 사용하면 불필요한 전자 메일을 제거하고 현재 진행 중인 중요한 작업에 집중할 수 있습니다.
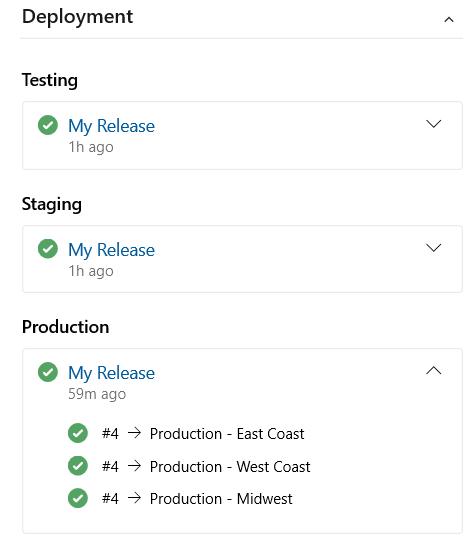
배포에 작업 항목 연결
작업 항목 양식에서 배포 컨트롤의 미리 보기를 릴리스하게 되어 기쁩니다. 이 컨트롤은 작업 항목을 릴리스에 연결하고 작업 항목이 배포된 위치를 쉽게 추적할 수 있도록 합니다. 자세한 내용은 여기에서 설명서를 참조하세요.
Azure Repos
AKS로 연결하는 서비스 계정 기반 인증 사용
이전에는 AKS 배포 센터에서 Azure Pipelines를 구성할 때 Azure Resource Manager 커넥트ion을 사용했습니다. 이 연결은 파이프라인이 구성된 네임스페이스뿐만 아니라 전체 클러스터에 액세스할 수 있었습니다. 이 업데이트를 통해 파이프라인은 서비스 계정 기반 인증을 사용하여 클러스터에 연결하므로 파이프라인과 연결된 네임스페이스에만 액세스할 수 있습니다.
끌어오기 요청의 Markdown 파일 미리 보기 병렬 차이
이제 새 미리 보기 단추를 사용하여 Markdown 파일의 모양을 미리 볼 수 있습니다. 또한 보기 단추를 선택하여 나란히 차이에서 파일의 전체 콘텐츠를 볼 수 있습니다.

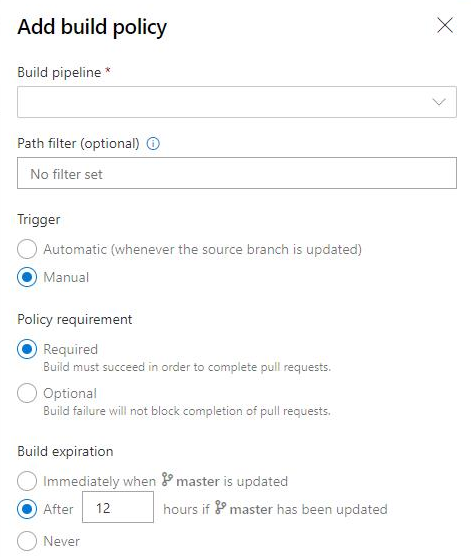
수동 빌드에 대한 빌드 정책 만료
정책은 팀의 코드 품질을 적용하고 관리 표준을 변경합니다. 이전에는 자동화된 빌드에 대한 빌드 만료 정책을 설정할 수 있습니다. 이제 빌드 만료 정책을 수동 빌드로 설정할 수도 있습니다.
커밋 작성자 메일에 기반한 커밋 차단을 위한 정책 추가
이제 관리 담당자는 커밋 작성자 전자 메일이 제공된 패턴과 일치하지 않는 리포지토리로 커밋이 푸시되지 않도록 푸시 정책을 설정할 수 있습니다.
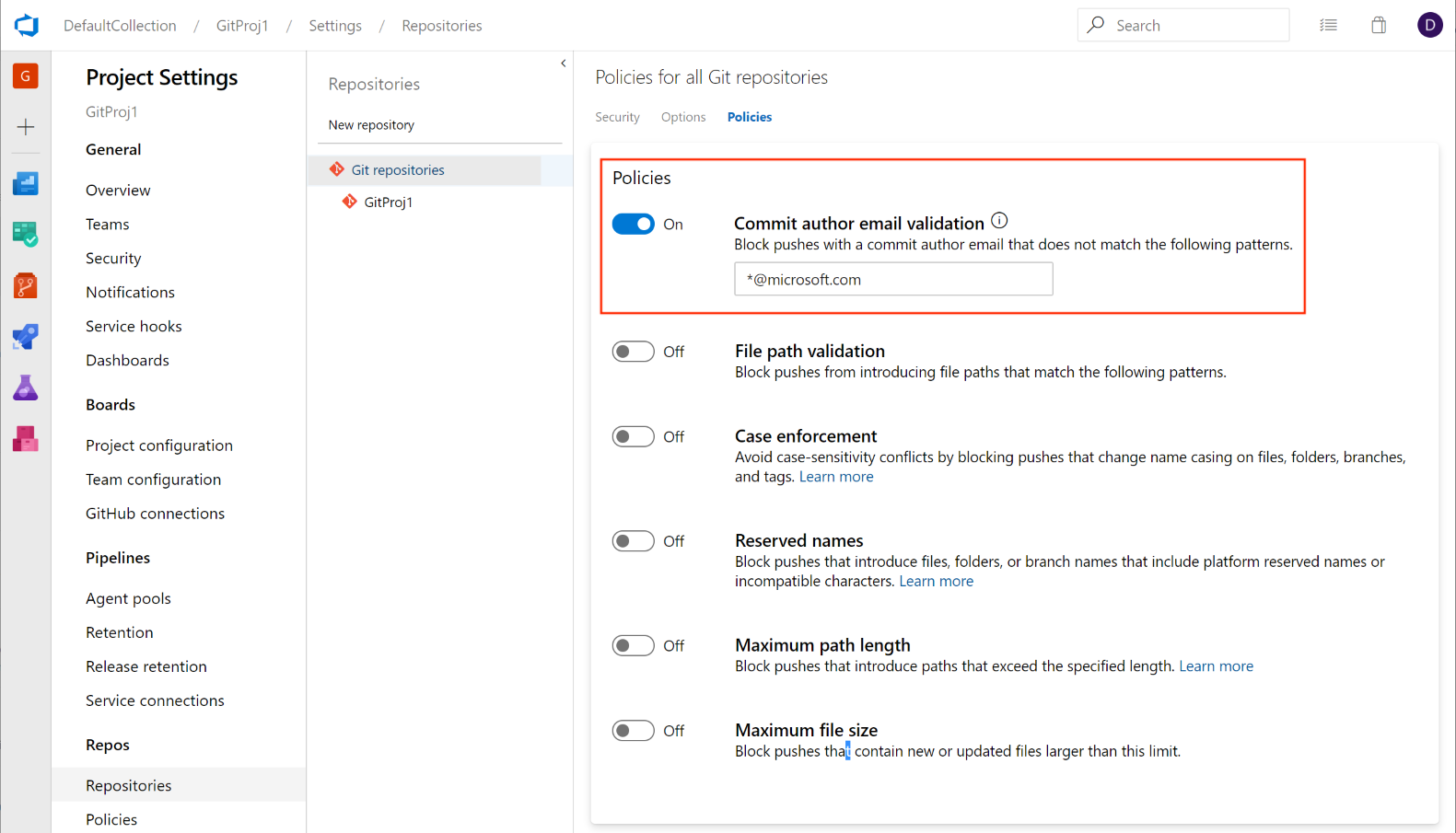
이 기능은 유사한 환경을 제공하기 위해 개발자 커뮤니티의 제안에 따라 우선 순위가 지정되었습니다. 계속해서 티켓을 열어 두고 사용자가 보고 싶은 다른 유형의 푸시 정책을 알려줄 것을 권장합니다.
Azure Pipelines
재시도 실패 단계
참고 항목
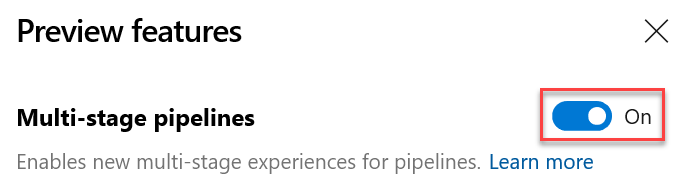
이 기능을 사용하려면 미리 보기 기능 다단계 파이프라인을 사용하도록 설정해야 합니다.
다단계 파이프라인에서 가장 많이 요청된 기능 중 하나는 처음부터 시작하지 않고도 실패한 단계를 다시 시도하는 기능입니다. 이 업데이트를 통해 이 기능의 큰 부분을 추가하고 있습니다.
이제 실행이 실패할 때 파이프라인 단계를 다시 시도할 수 있습니다. 첫 번째 시도에서 실패한 작업과 실패한 작업에 전이적으로 의존하는 작업은 모두 다시 시도됩니다.
이렇게 하면 여러 가지 방법으로 시간을 절약할 수 있습니다. 예를 들어 한 단계에서 여러 작업을 실행하는 경우 각 스테이지가 다른 플랫폼에서 테스트를 실행하도록 할 수 있습니다. 다른 플랫폼이 통과하는 동안 한 플랫폼의 테스트가 실패하는 경우 통과한 작업을 다시 실행하지 않으면 시간을 절약할 수 있습니다. 또 다른 예로, 네트워크 연결이 흐리기 때문에 배포 단계가 실패했을 수 있습니다. 해당 단계를 다시 시도하면 다른 빌드를 생성할 필요가 없으므로 시간을 절약할 수 있습니다.
이 기능에는 몇 가지 알려진 간격이 있습니다. 예를 들어 명시적으로 취소하는 단계를 다시 시도할 수 없습니다. 향후 업데이트에서 이러한 격차를 해소하기 위해 노력하고 있습니다.
YAML 파이프라인의 승인을 위한 고급 기능
참고 항목
이 기능을 사용하려면 다단계 파이프라인 및 새 서비스 연결 환경 미리 보기 기능이 활성화되어 있어야 합니다.
다단계 YAML 파이프라인을 지속적으로 개선하고 있습니다. 이 업데이트를 통해 서비스 연결 및 에이전트 풀에 대한 승인을 구성할 수 있습니다. 승인을 위해 인프라 소유자와 개발자 간의 역할 분리를 따릅니다. 환경, 서비스 연결 및 에이전트 풀과 같은 리소스에 대한 승인을 구성하면 리소스를 사용하는 모든 파이프라인 실행에 먼저 승인이 필요합니다.
환경은 환경에 대한 승인을 구성하는 것과 유사합니다. 단계에서 참조된 리소스에 대한 승인이 보류 중인 경우 파이프라인이 수동으로 승인될 때까지 파이프라인 실행이 대기합니다.

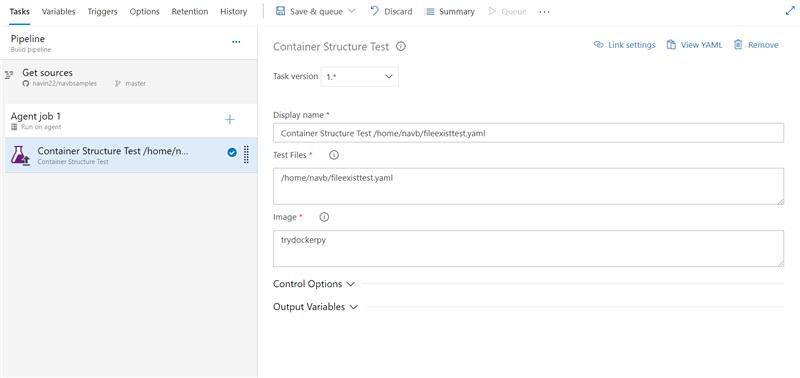
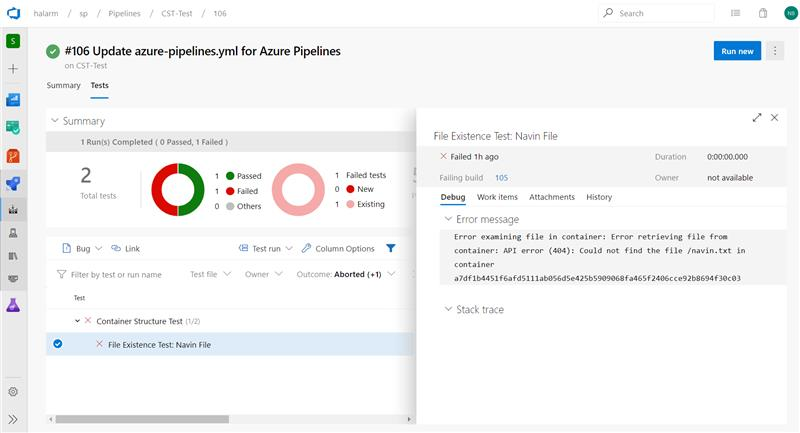
Azure Pipelines의 컨테이너 구조 테스트 지원
애플리케이션에서 컨테이너의 사용량이 증가하고 있으므로 강력한 테스트 및 유효성 검사가 필요합니다. 이제 Azure Pipelines는 컨테이너 구조 테스트를 지원 합니다. 이 프레임워크는 컨테이너의 내용과 구조를 확인하는 편리하고 강력한 방법을 제공합니다.
명령 테스트, 파일 존재 테스트, 파일 콘텐츠 테스트 및 메타데이터 테스트 등 함께 실행할 수 있는 네 가지 테스트 범주를 기반으로 이미지 구조의 유효성을 검사할 수 있습니다. 파이프라인의 결과를 사용하여 이동/이동 결정을 내릴 수 있습니다. 테스트 데이터는 오류 메시지와 함께 파이프라인 실행에서 사용할 수 있으므로 오류 문제를 더 잘 해결할 수 있습니다.
구성 파일 및 이미지 세부 정보 입력
테스트 데이터 및 요약
Flaky 버그 관리 및 해결 방법
7월에는 감지, 보고 및 해결을 통해 종단 간 수명 주기를 지원하기 위해 벗겨진 테스트 관리를 도입했습니다. 더 향상하기 위해 벗겨진 테스트 버그 관리 및 해상도를 추가하고 있습니다.
벗겨진 테스트를 조사하는 동안 버그 작업을 사용하여 버그를 만들 수 있습니다. 그러면 개발자에게 할당하여 벗겨진 테스트의 근본 원인을 추가로 조사할 수 있습니다. 버그 보고서에는 오류 메시지, 스택 추적 및 테스트와 관련된 기타 정보와 같은 파이프라인에 대한 정보가 포함됩니다.
버그 보고서가 확인되거나 닫히면 테스트의 표시를 자동으로 취소합니다.
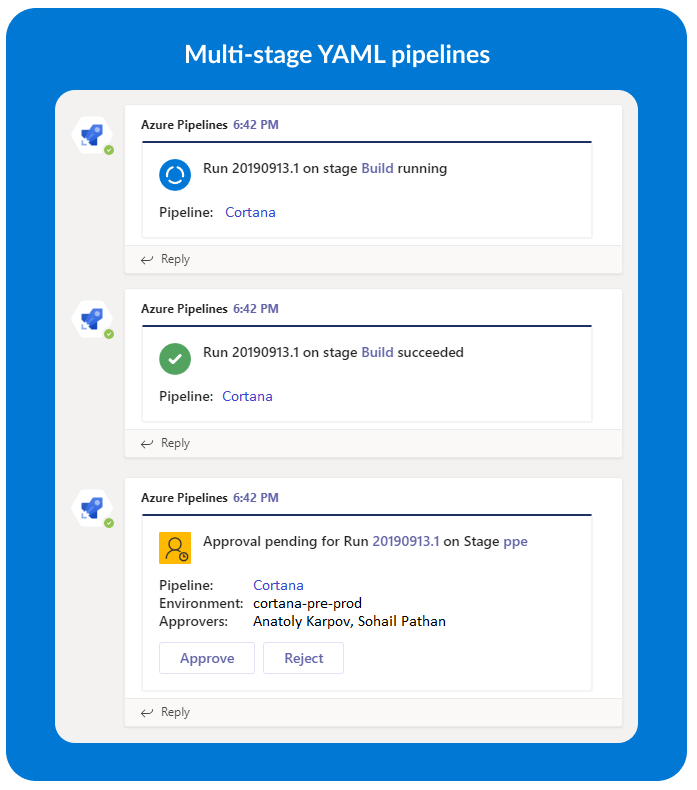
Slack 및 Microsoft Teams용 Azure Pipelines 앱의 고급 기능
다단계 YAML 기반 파이프라인
참고 항목
이 기능을 사용하려면 미리 보기 기능 다단계 파이프라인을 사용하도록 설정해야 합니다.
Slack 및 Microsoft Teams용 Azure Pipelines 앱은 이제 CI 및 CD에 대한 다단계 YAML 파이프라인을 지원합니다. 이 향상된 기능을 사용하면 YAML 파이프라인과 관련된 다양한 이벤트에 대한 알림을 받게 됩니다.
다단계 YAML 파이프라인에 대해 지원되는 이벤트
- 실행 상태가 변경됨
- 실행 단계 상태가 변경됨
- 승인을 기다리는 실행 단계
- 실행 단계 승인 완료
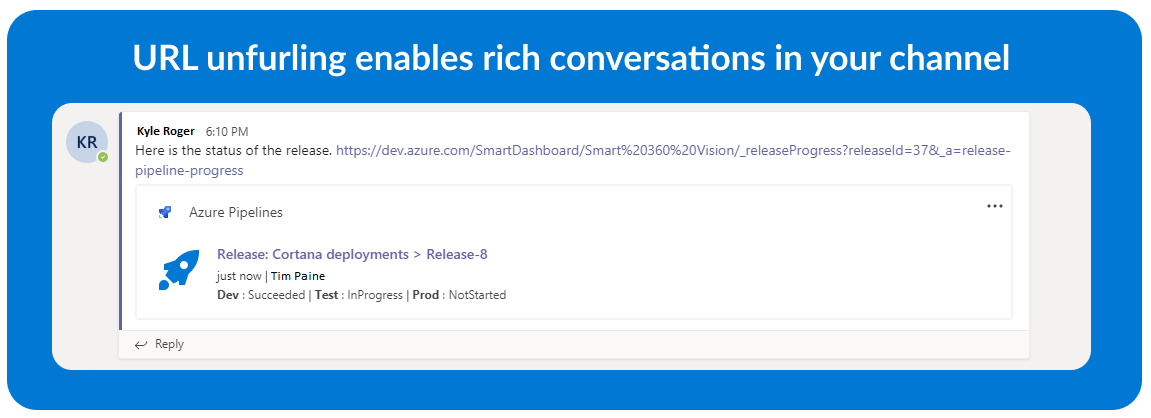
URL 풀기 및 메시징 확장
Microsoft Teams용 Azure Pipelines 앱에 대한 메시징 확장을 추가했습니다. 이제 파이프라인을 검색하고 파이프라인에 대한 관련 세부 정보를 채널에서 카드 공유할 수 있습니다. URL 해제를 사용하면 파이프라인에 대한 토론을 시작하고 의미 있는 상황별 대화를 할 수 있습니다.
호스트된 파이프라인 이미지 업데이트
여러 Azure Pipelines 호스팅 VM 이미지를 업데이트했습니다. 다음은 이 업데이트의 몇 가지 주요 내용입니다.
- Go 1.13을 Ubuntu 16.04, Ubuntu 18.04, VS2017 및 VS2019에 추가했습니다. 기본값으로 1.12를 다시 기본.
- Ubuntu 16.04, Ubuntu 18.04, VS2017 및 VS2019에 Android SDK 및 빌드 도구 29가 추가되었습니다.
- VS2017 및 VS2019에 Az Module 2.6.0이 추가되었습니다.
- 다양한 버그를 수정했습니다.
최신 릴리스에 대한 자세한 내용은 여기에서 확인할 수 있습니다.
참고 항목
2019년 3월 31일에 수명이 종료된 이후 향후 업데이트의 모든 이미지에서 Ruby 2.3을 제거합니다.
Open Policy Agent 설치 프로그램 작업
Open Policy Agent는 통합된 컨텍스트 인식 정책 적용을 가능하게 하는 오픈 소스 범용 정책 엔진입니다. 정책 에이전트 설치 관리자 열기 작업을 추가했습니다. 코드 공급자로서의 인프라와 관련하여 파이프라인 내 정책 적용에 특히 유용합니다.
예를 들어 Open Policy Agent는 파이프라인에서 Rego 정책 파일 및 Terraform 계획을 평가할 수 있습니다.
task: OpenPolicyAgentInstaller@0
inputs:
opaVersion: '0.13.5'
릴리스 파이프라인용 파이프라인 데코레이터
파이프라인 데코레이터를 사용하면 모든 작업의 시작과 끝에 단계를 추가할 수 있습니다. 이는 조직의 모든 파이프라인에 적용되므로 단일 정의에 단계를 추가하는 것과 다릅니다.
우리는 빌드 및 YAML 파이프라인에 대한 데코레이터를 지원하고 있으며, 고객은 이를 사용하여 작업의 단계를 중앙에서 제어합니다. 이제 파이프라인을 릴리스하도록 지원을 확장하고 있습니다. 확장을 만들어 새 기여 지점을 대상으로 하는 단계를 추가할 수 있으며 릴리스 파이프라인의 모든 에이전트 작업에 추가됩니다.
Azure Test Plans
새 Test Plans 페이지
이제 대부분의 계획, 작성, 실행 및 추적 기능을 새 테스트 계획 페이지에서 사용할 수 있습니다. 따라서 모든 테스트 계획 사용자가 피드백을 제공할 수 있도록 이 기능을 사용하도록 설정하고 있습니다. 이전 테스트 계획 페이지와 패리티에 도달하는 데 필요한 몇 가지 기능을 다시 기본 다음 몇 스프린트에서 사용하도록 설정됩니다. 필요한 경우 사용자는 미리 보기 기능 메뉴에서 테스트 계획 페이지를 사용하지 않도록 설정할 수 있습니다. 자세한 내용은 여기를 읽어보세요.
보고
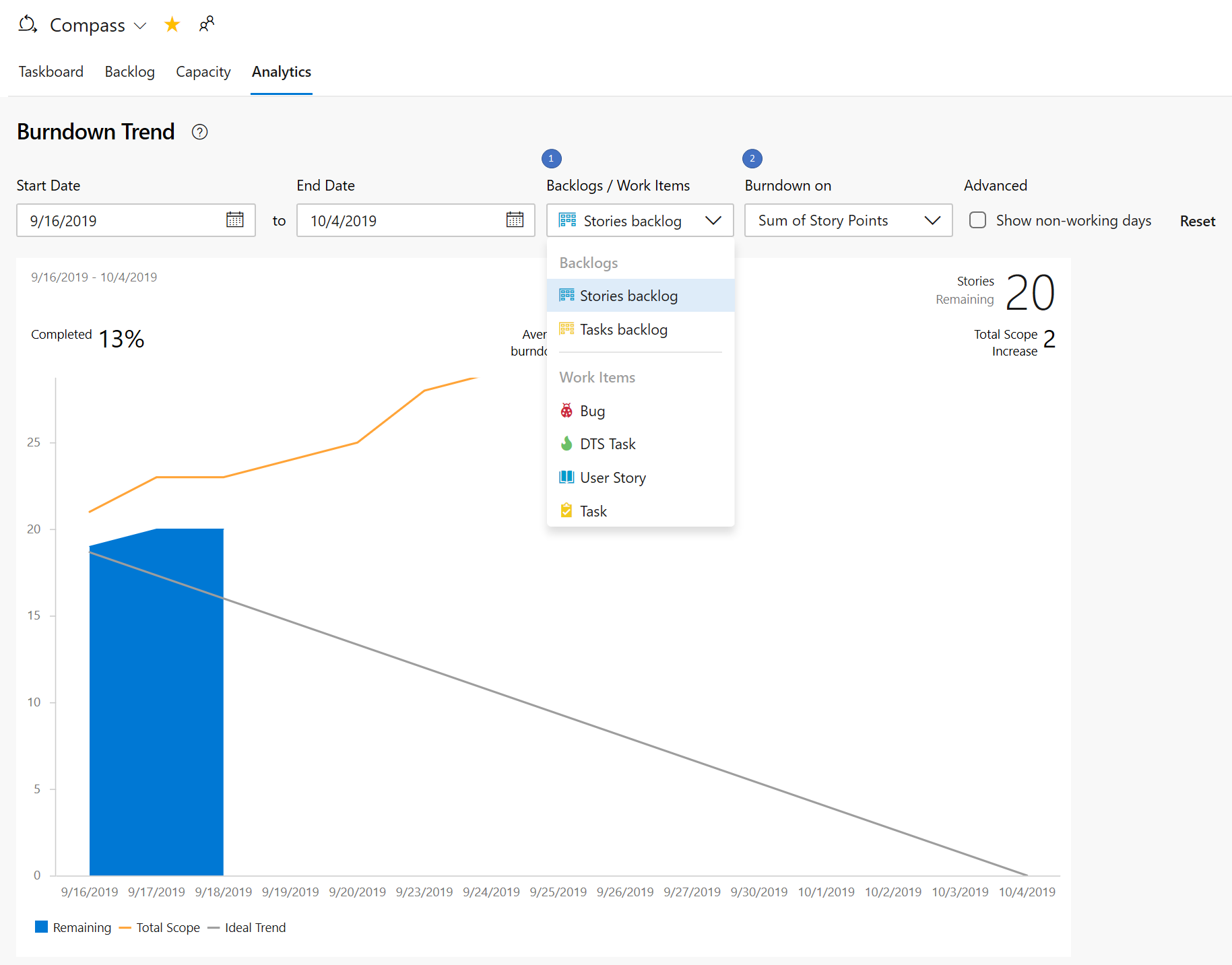
스토리 포인트를 사용한 인라인 스프린트 번다운
이제 스프린트 번다운은 스토리에 의해 번다운할 수 있습니다. 이렇게 하면 개발자 커뮤니티의 피드백이 해결됩니다.
스프린트 허브에서 분석 탭을 선택합니다. 그런 다음 다음과 같이 보고서를 구성합니다.
- 스토리 백로그 선택
- 스토리 포인트의 합계에서 번다운하려면 선택합니다.
Wiki
짧고 읽을 수 있는 Wiki 페이지 URL
더 이상 여러 줄 URL을 사용하여 위키 페이지 링크를 공유할 필요가 없습니다. URL의 페이지 ID를 활용하여 매개 변수를 제거하므로 URL을 더 짧고 읽기 쉽게 만듭니다.
URL의 새 구조는 다음과 같습니다.
https://dev.azure.com/{accountName}/{projectName}/_wiki/wikis/{wikiName}/{pageId}/{readableWiki PageName}
다음은 Azure DevOps Wiki 시작 페이지에 대한 새 URL의 예입니다.
https://dev.azure.com/microsoft/ AzureDevOps/_wiki/wikis/AzureDevOps.wiki/1/Welcome-to-Azure-DevOps-Wiki
개발자 커뮤니티의 이 기능 제안 티켓 에 따라 우선 순위가 지정되었습니다.
Wiki에서 Mermaid 다이어그램 지원
위키 페이지에 인어 다이어그램을 삽입하는 지원이 추가되었습니다. 이제 디자인 문서에서 흐름 차트, 시퀀스 다이어그램을 만들고, 편집하고, 관리하고, Azure DevOps Wiki의 계획 문서에 Gantt 차트를 추가할 수 있습니다.

개발자 커뮤니티의 이 기능 제안 티켓 에 따라 우선 순위가 지정되었습니다. 인어 다이어그램에 대한 자세한 내용은 여기 설명서를 참조하세요.
다음 단계
참고 항목
이러한 기능은 향후 2~3주 동안 출시될 예정입니다.
Azure DevOps로 이동하여 살펴보세요.
피드백을 제공하는 방법
이러한 기능에 대해 어떻게 생각하는지 듣고 싶습니다. 피드백 메뉴를 사용하여 문제를 보고하거나 제안을 제공합니다.
Stack Overflow에서 커뮤니티에서 조언과 질문에 답변할 수도 있습니다.
감사합니다,
라비 샨커
피드백
출시 예정: 2024년 내내 콘텐츠에 대한 피드백 메커니즘으로 GitHub 문제를 단계적으로 폐지하고 이를 새로운 피드백 시스템으로 바꿀 예정입니다. 자세한 내용은 다음을 참조하세요. https://aka.ms/ContentUserFeedback
다음에 대한 사용자 의견 제출 및 보기