Auditlogboeken openen, exporteren en filteren
Azure DevOps Services
Notitie
Controle is nog steeds beschikbaar als openbare preview.
Op de pagina Controle van uw organisatie Instellingen kunt u auditlogboeken openen, exporteren en filteren, waarmee de vele wijzigingen in uw Azure DevOps-organisatie(en) worden bijgehouden. Met deze logboeken kunt u ze gebruiken om te voldoen aan de nalevings- en governancedoelstellingen van uw organisatie.
Belangrijk
Controle is alleen beschikbaar voor organisaties die worden ondersteund door Microsoft Entra ID. Zie Verbinding maken uw organisatie naar Microsoft Entra-id voor meer informatie.
Controlewijzigingen treden op wanneer een gebruiker of service-identiteit binnen de organisatie de status van een artefact bewerkt. Mogelijk ziet u gebeurtenissen die zijn geregistreerd voor een van de volgende gebeurtenissen:
- machtigingen worden gewijzigd
- verwijderde resources
- wijzigingen in vertakkingsbeleid
- controle van logboektoegang en downloads
- en nog veel meer...
Gebeurtenissen worden 90 dagen opgeslagen, waarna ze worden verwijderd. U kunt echter een back-up maken van controlegebeurtenissen op een externe locatie om de gegevens langer dan de periode van 90 dagen te bewaren.
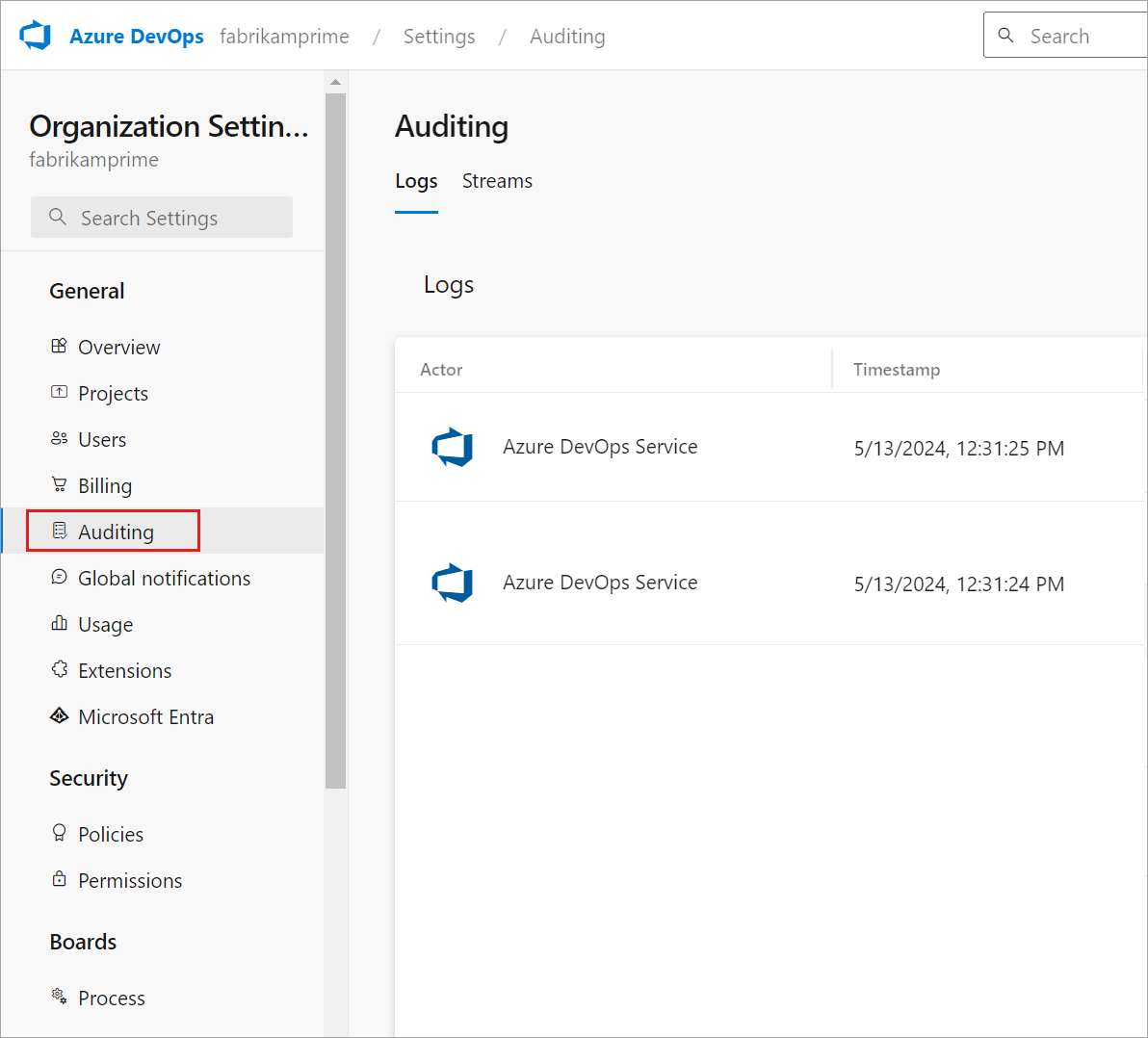
Controlegebeurtenissen kunnen worden geopend via twee methoden op de pagina Controle in uw organisatie Instellingen:
- Via de controlelogboeken die beschikbaar zijn op het hoofdtabblad Logboeken en
- via controlestromen die zijn ingesteld via het tabblad Streams .
Notitie
Controle is niet beschikbaar voor on-premises implementaties van Azure DevOps Server. Het is mogelijk om een controlestroom van een Azure DevOps Services-exemplaar te verbinden met een on-premises of cloudexemplaren van Splunk, maar u moet ervoor zorgen dat u IP-bereiken toestaat voor binnenkomende verbindingen. Zie Toegestane adreslijsten en netwerkverbindingen, IP-adressen en bereikbeperkingen voor meer informatie.
Vereisten
Controle is standaard uitgeschakeld voor alle Azure DevOps Services-organisaties en kan worden in- en uitgeschakeld door eigenaren van organisaties en projectverzameling Beheer istrators op de pagina Organisatie Instellingen. Projectverzameling Beheer istrators zijn standaard de enige groep die volledige toegang heeft tot de functie Controle.
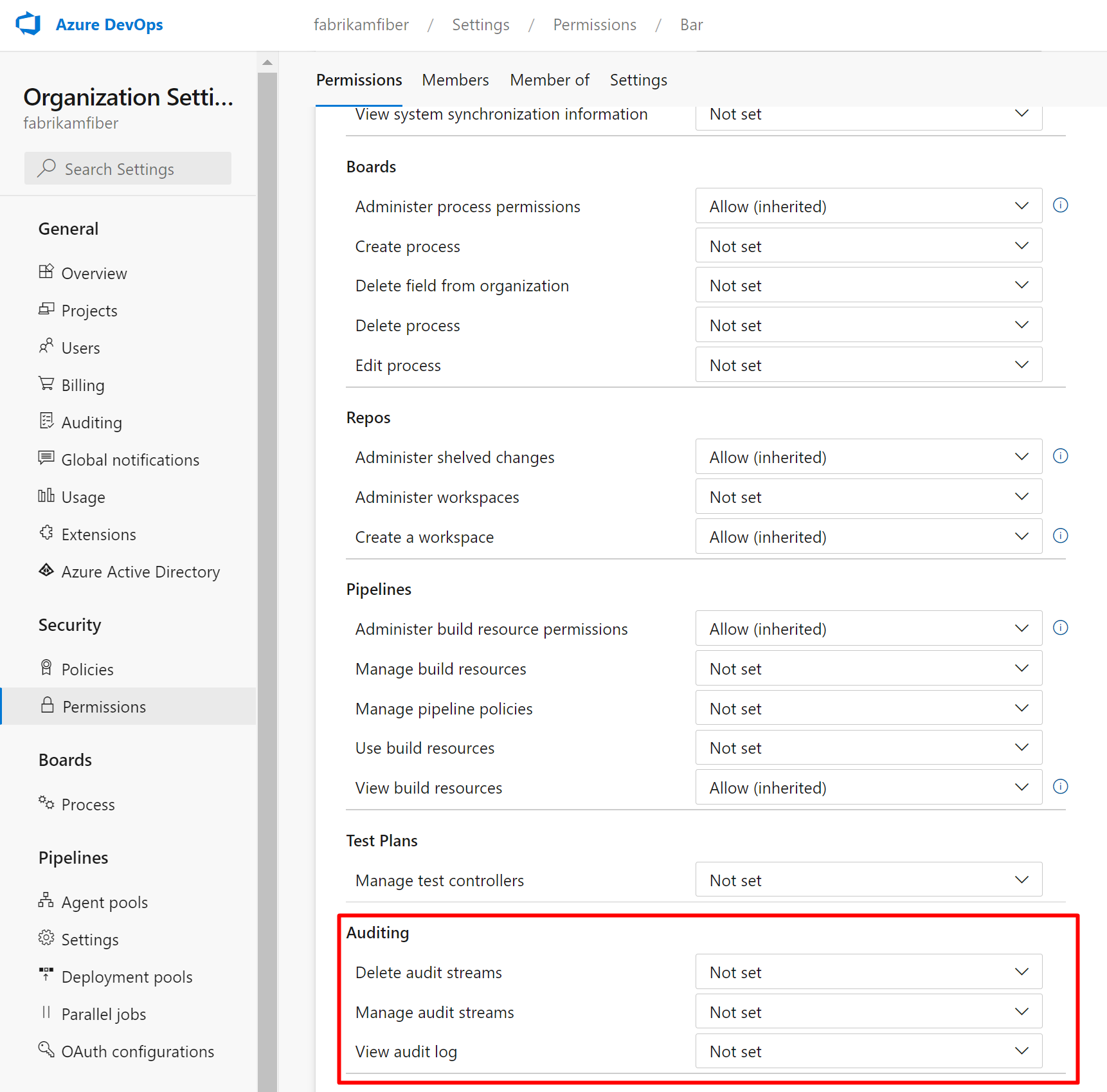
Controlemachtigingen
- Standaard hebben leden van de organisatie-eigenaren en Beheer istrators-groepen volledige toegang tot alle controlefuncties.
- Specifieke auditmachtigingen kunnen worden verleend aan elke groep via de pagina Beveiligingsmachtigingen in organisatie-Instellingen.
Notitie
Als de functie Zichtbaarheid en samenwerking van gebruikers beperken tot specifieke projecten preview is ingeschakeld voor de organisatie, kunnen gebruikers die zijn toegevoegd aan de groep Gebruikers met projectbereik de controle niet weergeven en hebben beperkte zichtbaarheid op pagina's met organisatie-instellingen. Zie Uw organisatie beheren, de zichtbaarheid van gebruikers voor projecten en meer beperken voor meer informatie en belangrijke beveiligingsgerelateerde vermeldingen.
Controle in- en uitschakelen
Meld u aan bij uw organisatie (
https://dev.azure.com/{yourorganization}).Selecteer
 Organisatie-instellingen.
Organisatie-instellingen.Selecteer Beleid onder de kop Beveiliging .
Schakel de knop Controlegebeurtenissen in logboeken in.
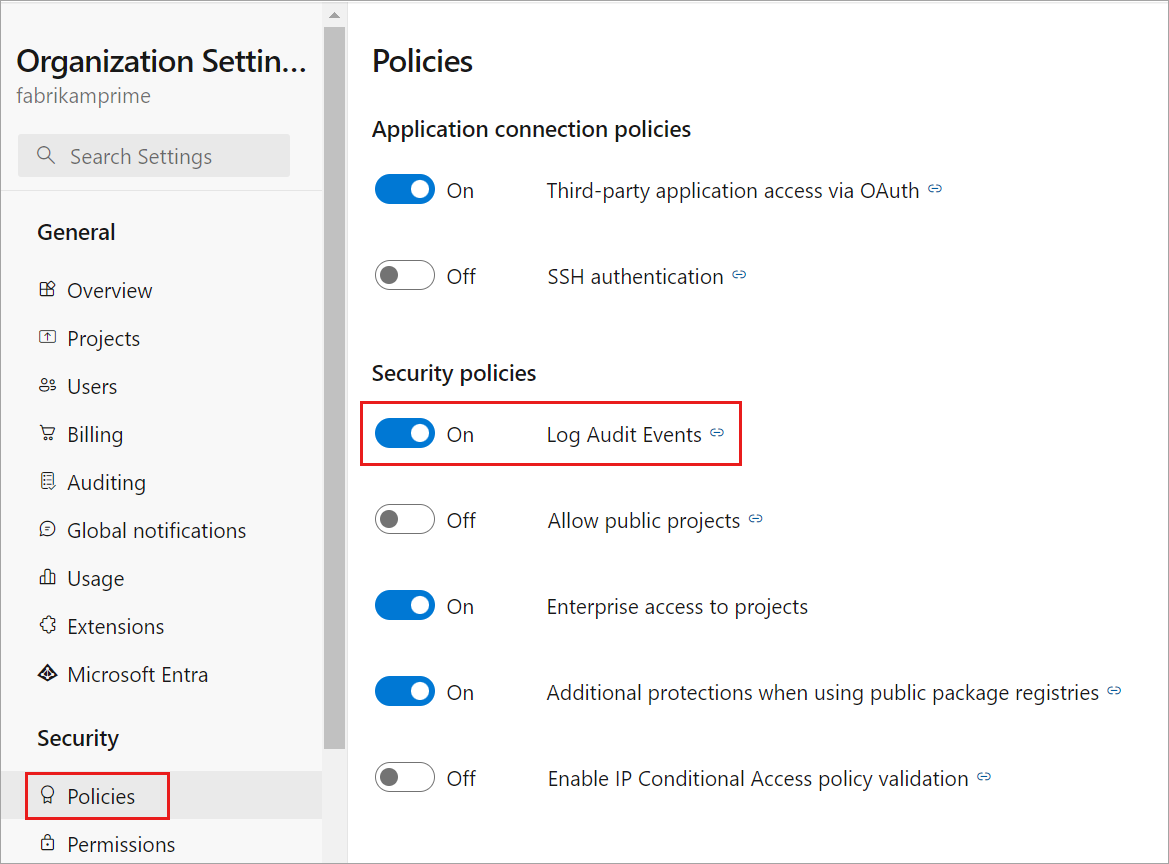
De organisatie heeft nu Controle ingeschakeld. Mogelijk moet u de pagina vernieuwen om controle weer te geven in de zijbalk. Controlegebeurtenissen worden weergegeven in controlelogboeken en via alle controlestromen die zijn geconfigureerd.
- Als u controle-gebeurtenissen niet meer wilt ontvangen, schakelt u de knop Controle inschakelen in op UIT. Wanneer de knop is uitgeschakeld, wordt de pagina Controle niet meer weergegeven in de zijbalk en is de pagina Controlelogboeken niet beschikbaar. Alle controlestromen ontvangen geen gebeurtenissen meer.
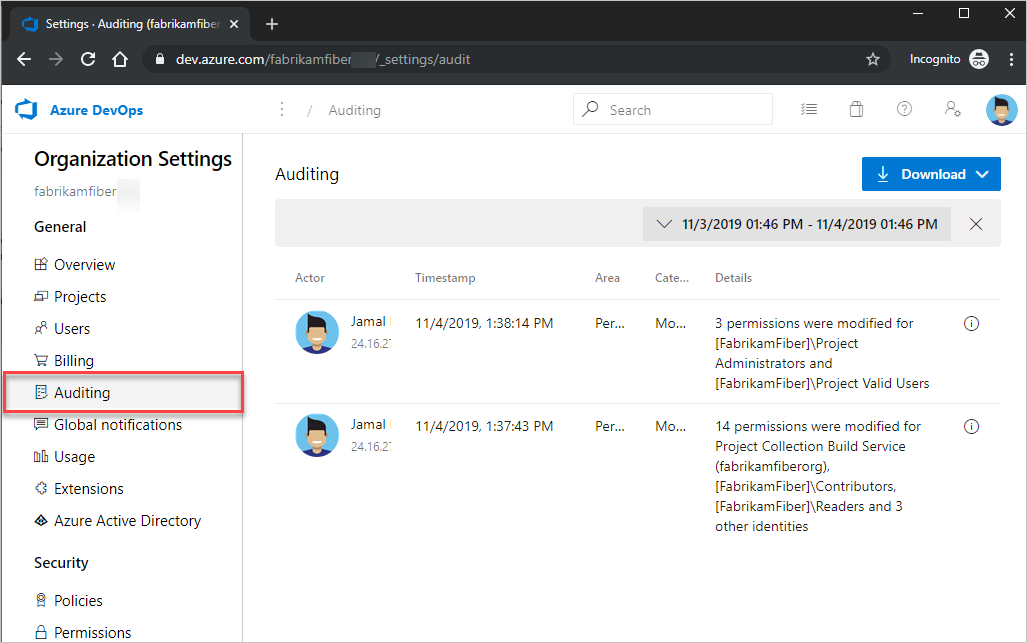
Toegangscontrole
Meld u aan bij uw organisatie (
https://dev.azure.com/{yourorganization}).Selecteer
 Organisatie-instellingen.
Organisatie-instellingen.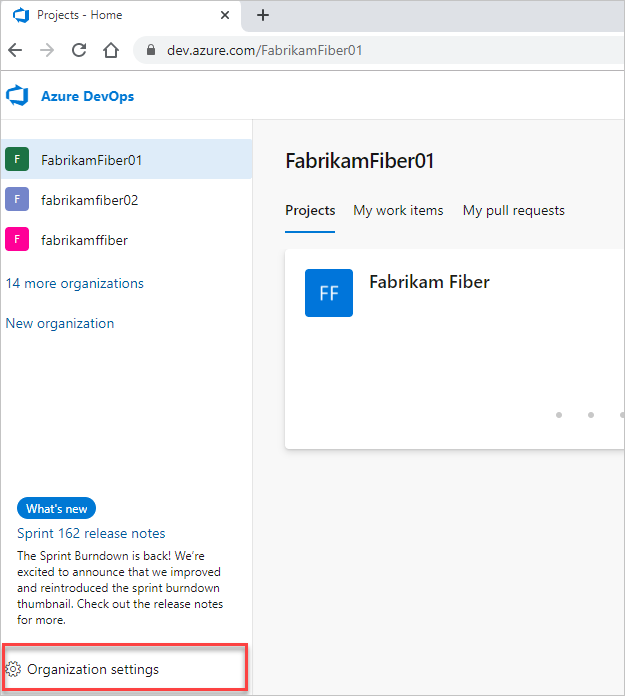
Selecteer Controle.
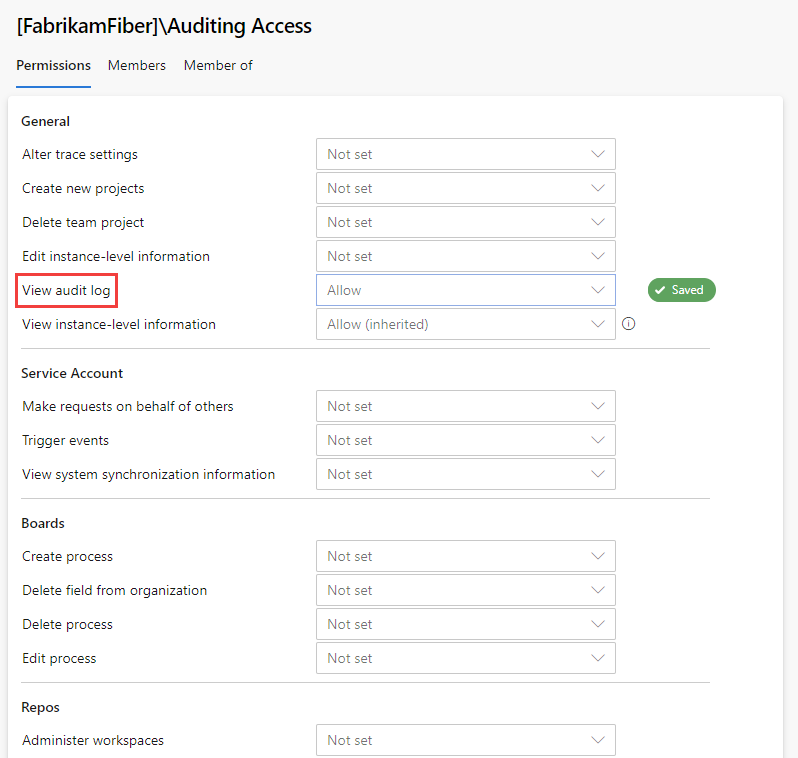
Als u Controle niet ziet in organisatie-instellingen, hebt u geen toegang om controlegebeurtenissen weer te geven. De groep Projectverzameling Beheer istrators kan machtigingen verlenen aan andere gebruikers en groepen, zodat ze de controlepagina's kunnen bekijken. Hiervoor selecteert u Machtigingen en zoekt u de groep of gebruikers om controletoegang te verlenen.
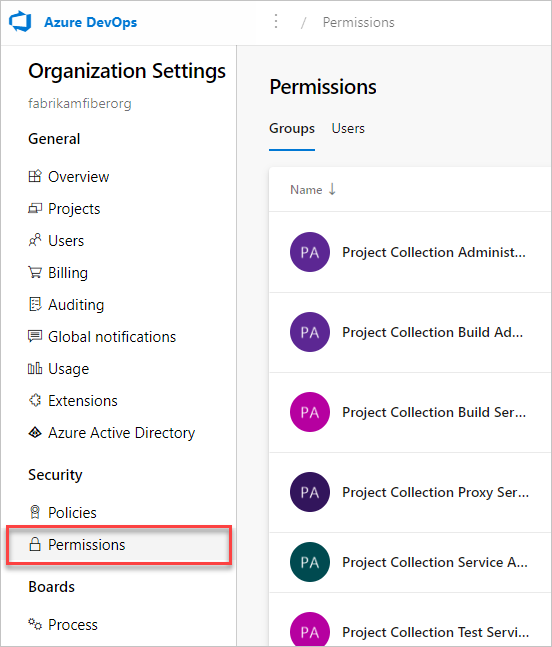
Stel auditlogboek weergeven in om toe te staan en selecteer wijzigingen opslaan.
De gebruikers- of groepsleden hebben nu toegang om de controlegebeurtenissen van uw organisatie weer te geven.
Auditlogboek controleren
De controlepagina biedt een eenvoudig overzicht van de controlegebeurtenissen die zijn vastgelegd voor uw organisatie. Zie de volgende beschrijving van de informatie die zichtbaar is op de controlepagina:
Gebeurtenisgegevens en -details controleren
| Gegevens | DETAILS |
|---|---|
| Acteur | Weergavenaam van de persoon die de controlegebeurtenis heeft geactiveerd. |
| IP | IP-adres van de persoon die de controlegebeurtenis heeft geactiveerd. |
| Tijdstempel | Tijdstip waarop de geactiveerde gebeurtenis is opgetreden. De tijd is gelokaliseerd naar uw tijdzone. |
| Gebied | Productgebied in Azure DevOps waar de gebeurtenis zich voordeed. |
| Categorie | Beschrijving van het type actie dat is opgetreden (bijvoorbeeld wijzigen, naam wijzigen, maken, verwijderen, verwijderen, uitvoeren en toegangsgebeurtenis). |
| DETAILS | Korte beschrijving van wat er zich tijdens de gebeurtenis voordeed. |
Tijdens elke controlegebeurtenis wordt ook aanvullende informatie vastgelegd die kan worden weergegeven op de controlepagina. Deze informatie omvat het verificatiemechanisme, een correlatie-id om vergelijkbare gebeurtenissen aan elkaar te koppelen, gebruikersagent en meer gegevens, afhankelijk van het type controlegebeurtenis. Deze informatie kan alleen worden bekeken door de controlegebeurtenissen te exporteren naar CSV of JSON.
ID & correlatie-id
Elke controlegebeurtenis heeft unieke id's met de naam 'ID' en 'CorrelationID'. De correlatie-id is handig voor het vinden van gerelateerde controlegebeurtenissen. Een gemaakt project kan bijvoorbeeld enkele tientallen controlegebeurtenissen genereren. U kunt deze gebeurtenissen aan elkaar koppelen omdat ze allemaal dezelfde correlatie-id hebben.
Wanneer een controlegebeurtenis-id overeenkomt met de correlatie-id, geeft deze aan dat de controlegebeurtenis de bovenliggende of oorspronkelijke gebeurtenis is. Als u alleen oorspronkelijke gebeurtenissen wilt zien, zoekt u naar de gebeurtenissen waarbij 'ID' gelijk is aan de betreffende correlatie-id. Als u vervolgens een gebeurtenis en de bijbehorende gebeurtenissen wilt onderzoeken, kunt u alle gebeurtenissen opzoeken met een correlatie-id die overeenkomt met de id van de oorspronkelijke gebeurtenis. Niet alle gebeurtenissen hebben gerelateerde gebeurtenissen.
Bulkgebeurtenissen
Sommige controlegebeurtenissen kunnen meerdere acties bevatten die tegelijk plaatsvonden, ook wel 'bulkcontrolegebeurtenissen' genoemd. U kunt deze gebeurtenissen van anderen onderscheiden met een informatiepictogram uiterst rechts van de gebeurtenis. U vindt afzonderlijke details over de acties die zijn opgenomen in de bulkcontrolegebeurtenissen via de gedownloade controlegegevens.
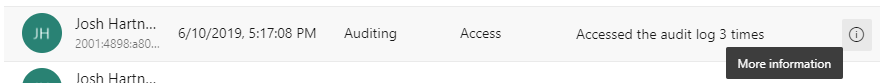
Als u het informatiepictogram selecteert, wordt aanvullende informatie weergegeven over wat er is gebeurd in deze controlegebeurtenis.
Terwijl u de auditgebeurtenissen bekijkt, kunt u de kolommen Categorie en Gebied van belang vinden. Met deze kolommen kunt u alleen de typen gebeurtenissen vinden waarin u geïnteresseerd bent. De volgende tabellen zijn een lijst met categorieën en gebieden en de bijbehorende beschrijvingen:
Lijst met gebeurtenissen
We proberen ons best om maandelijks nieuwe controle-gebeurtenissen toe te voegen. Als u een gebeurtenis wilt zien die momenteel niet wordt bijgehouden, kunt u dit met ons delen in de ontwikkelaarscommunity.
Zie de lijst met controle-gebeurtenissen voor een volledige lijst met alle gebeurtenissen die we momenteel kunnen verzenden via de functie Controle.
Notitie
Wilt u weten welke gebeurtenisgebieden uw organisatie registreert? Zorg ervoor dat u de query-API voor auditlogboeken bekijkt: https://auditservice.dev.azure.com/{YOUR_ORGANIZATION}/_apis/audit/actionsen vervang {YOUR_ORGANIZATION} door de naam van uw organisatie. Deze API retourneert een lijst met alle controlegebeurtenissen (of acties) die uw organisatie kan verzenden.
Auditlogboek filteren op datum en tijd
In de huidige gebruikersinterface voor controle kunt u alleen gebeurtenissen filteren op een datum- of tijdsbereik. Als u het bereik van de weergavebare controlegebeurtenissen wilt verkleinen op basis van een datumbereik, selecteert u het tijdfilter aan de rechterkant van de pagina.
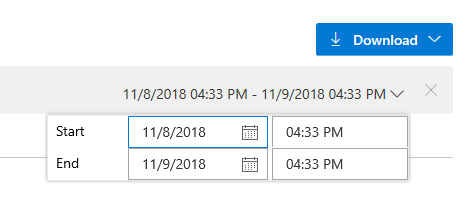
Gebruik de filters om elk tijdsbereik in de afgelopen 90 dagen te selecteren en het bereik tot de minuut te bepalen. Nadat u een tijdsbereik hebt geselecteerd, selecteert u Toepassen op de tijdsbereikkiezer om de zoekopdracht te starten. Standaard worden de bovenste 200 resultaten geretourneerd voor die tijdselectie. Als er meer resultaten zijn, kunt u omlaag schuiven om ze op de pagina te laden.
Controle-gebeurtenissen exporteren
Als u meer gedetailleerde zoekopdrachten wilt uitvoeren op de controlegegevens of gegevens wilt opslaan voor meer dan 90 dagen aan gegevens, moet u bestaande controlegebeurtenissen exporteren. De geëxporteerde gegevens kunnen vervolgens worden opgeslagen op een andere locatie of service.
Selecteer de knop Downloaden in de rechterbovenhoek van de controlepagina om controlegebeurtenissen te exporteren. U kunt ervoor kiezen om te downloaden als een CSV- of JSON-bestand.
Als u een van beide opties selecteert, wordt het downloaden gestart. Gebeurtenissen worden gedownload op basis van het tijdsbereik dat u in het filter hebt geselecteerd. Als u één dag hebt geselecteerd, krijgt u de gegevens die één dag zijn geretourneerd. Als u alle 90 dagen wilt, selecteert u 90 dagen in het tijdsbereikfilter en start u het downloaden.
Notitie
Voor langetermijnopslag en analyse van uw controlegebeurtenissen kunt u overwegen uw gebeurtenissen downstream te verzenden naar een SIEM-hulpprogramma (Security Information and Event Management) met behulp van de functie Controlestreaming. Het exporteren van de controlelogboeken wordt aanbevolen voor cursory-gegevensanalyse.
Als u gegevens wilt filteren op meer dan het datum-/tijdsbereik, raden we u aan logboeken als CSV-bestanden te downloaden en Microsoft Excel of andere CSV-parsers te importeren om door gebieds- en categoriekolommen te bladeren. Voor analyse van nog grotere gegevenssets raden we u aan geëxporteerde controlegebeurtenissen te uploaden naar een SIEM-hulpprogramma (Security Incident and Event Management) met behulp van de functie Controlestreaming. Met dergelijke hulpprogramma's kunt u meer dan 90 dagen aan gebeurtenissen, zoekopdrachten, gegenereerde rapporten en geconfigureerde waarschuwingen bewaren op basis van controlegebeurtenissen.
Beperkingen
De volgende beperkingen gelden voor wat kan worden gecontroleerd.
- Wijzigingen in microsoft Entra-groepslidmaatschap: controlelogboeken bevatten updates voor Azure DevOps-groepen en groepslidmaatschap (wanneer een gebeurtenisgebied 'Groepen' is). Als u echter lidmaatschap beheert via Microsoft Entra-groepen, worden dergelijke toevoegingen en verwijderingen van gebruikers uit die Microsoft Entra-groepen niet gecontroleerd door Azure DevOps in deze logboeken. Controleer de Auditlogboeken van Microsoft Entra om te zien wanneer een gebruiker of groep is toegevoegd aan of verwijderd uit een Microsoft Entra-groep.
- Aanmeldingsevenementen: er worden geen aanmeldingsevenementen voor Azure DevOps bijgehouden. Bekijk de Auditlogboeken van Microsoft Entra om aanmeldingsgebeurtenissen te controleren op uw Microsoft Entra-id.
Veelgestelde vragen
V: Wat is de groep DirectoryServiceAddMember en waarom wordt deze weergegeven in het auditlogboek?
A: De DirectoryServiceAddMember-groep is een systeemgroep die wordt gebruikt om het lidmaatschap van uw Azure DevOps-organisatie te beheren. Lidmaatschap van deze systeemgroep kan worden beïnvloed door veel systeem-, gebruikers- en beheeracties. Omdat deze groep een systeemgroep is die alleen wordt gebruikt voor interne processen, kunnen klanten controlelogboekvermeldingen negeren die lidmaatschapswijzigingen in deze groep vastleggen.
Verwante artikelen:
Feedback
Binnenkort beschikbaar: In de loop van 2024 zullen we GitHub-problemen geleidelijk uitfaseren als het feedbackmechanisme voor inhoud en deze vervangen door een nieuw feedbacksysteem. Zie voor meer informatie: https://aka.ms/ContentUserFeedback.
Feedback verzenden en weergeven voor