Like @Vasil Michev says you can use Access Control Policies.
Let say you want to allow all users but if the user is a member of the group TESTG then you allow the connection only if the IP is 1.2.3.4. You will have the following policy:
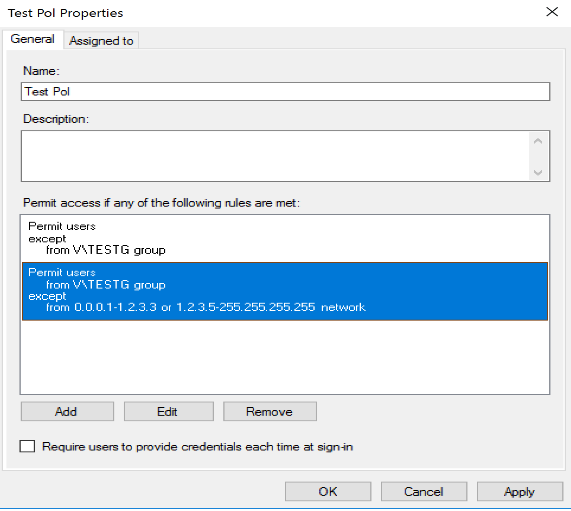
The first part allow all users as long as they are not member of the group.
If they are member of the group then we allow them as long as the IP is not between 0.0.0.0 and 1.2.3.3 and not between 1.2.3.6 and 255.255.255.255. In other word we allow only if the if IP is 1.2.3.4.
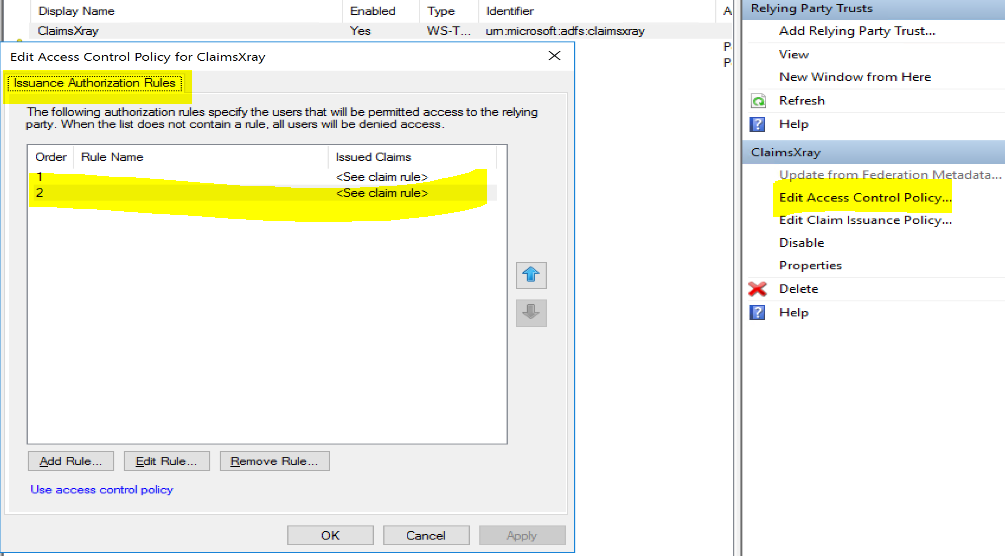
Also, you can still use the "old school" issuance authorization rules in Windows Server 2019 ADFS. To do so, set the policy of your relying party to $null, example:
Set-AdfsRelyingPartyTrust -TargetName ClaimsXray -AccessControlPolicyName:$null
Then check the GUI and you'll see your policy has been converted into an old school one :)