Hi there - Azure AD access tokens are JWTs: https://learn.microsoft.com/en-us/azure/active-directory/develop/access-tokens
One thing that may help is adding a redirect URI to https://jwt.ms so that you can see what claims are in the access token.
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
I'm building an Office.js addin for Word and attempting to use SSO for user logins. I followed the template provided at https://learn.microsoft.com/en-us/office/dev/add-ins/develop/create-sso-office-add-ins-aspnet and finally got it to work on my dev machine. Now I'm trying to deploy it to a server and I'm having problems, most recently AADSTS50011 (invalid redirect). The template specified using localhost:44355 as the host name and port in the redirect URI and (I think) in the Application ID URI in the "Expose an API" page. I have added an extra redirect URI pointing to my test server, but there is no way to add an additional Application ID URI. How should I be managing this? Should I register two apps, one for localhost and one for the server (and then a third for the production server, etc.)? Or is the Application ID URI always supposed to point to the ultimate production address?
Hi there - Azure AD access tokens are JWTs: https://learn.microsoft.com/en-us/azure/active-directory/develop/access-tokens
One thing that may help is adding a redirect URI to https://jwt.ms so that you can see what claims are in the access token.
actually, the problem was this line of code in AzureADAuthController:
Uri loginRedirectUri => new Uri(Url.Action(nameof(Authorize), "AzureADAuth", null, Request.Url.Scheme));
this returns a URI with an http protocol rather than https because the web server is listening on http behind a loadbalancer using https. I manually changed the loginRedirecUri to use https and the problem was resolved.
However, now I am having a problem decoding the accessToken returned with a successful login. My understanding it's a JWT, but it's not a valid JWT. What is the format?
You just need to make sure that you have both the localhost and production URL set in your Redirect URI list in your app registration, and that whatever you have in your application code matches one of these exactly (no missing spaces or slashes). Since this is just whatever URL you want your users to be directed to after signing in, you need to have the published production URL on hand and add it to the registration and the app configuration.
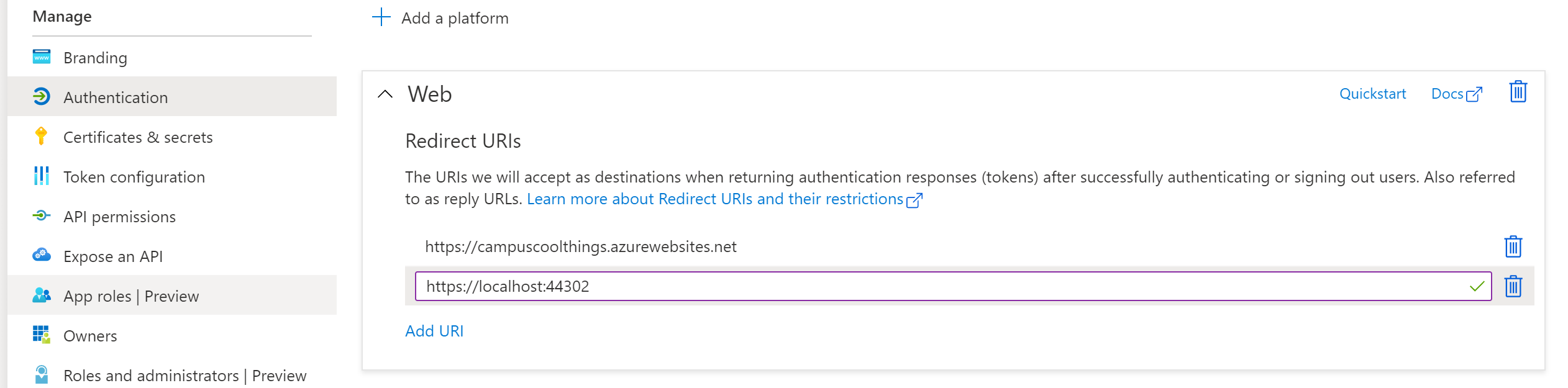
So the code will also need to have the published URL in it (https://myapp.azurewebsites.net)
string bootstrapContext = ClaimsPrincipal.Current.Identities.First().BootstrapContext.ToString();
UserAssertion userAssertion = new UserAssertion(bootstrapContext);
var cca = ConfidentialClientApplicationBuilder.Create(ConfigurationManager.AppSettings["ida:ClientID"])
**.WithRedirectUri("https://localhost:44355")**
.WithClientSecret(ConfigurationManager.AppSettings["ida:Password"])
.WithAuthority(ConfigurationManager.AppSettings["ida:Authority"])
.Build();
string[] graphScopes = { "https://graph.microsoft.com/Files.Read.All" };
For the issue with multiple Application ID URIs, as you mentioned you could solve that by having multiple app registrations for each environment, as described in this post.