I suggest you look at the Authentication Policies and Authentication Policy Silos. Those features came with WIni Server 2012 R2 and they make the isolation of admintrative zone easier (because no GPO are involved) more robust (because local admins can't override them).
You could create a Silo called Tier-0 on which you add your domain admin account, the machine account of their dedicate workstations as well as the computer account of your domain controllers. Then you apply an authentication policy is such a way that the domain admins account can only log-in on machine of the sale silo as theirs.
Here is an example. I have Pierre member of the domain admins group. Pierre's workstation is wks1 and he needs to be able to administrate DC1 (a domain controller). You enable claim support in your environment and run the following:
#Create a new policy
New-ADAuthenticationPolicy -Name "Tier-0_TGT_120mins" -Description "Authentication policy for Tier-0 (120 minutes TGT)." -UserTGTLifetimeMins 120 -Enforce -ProtectedFromAccidentalDeletion $True
#Create a new silo
New-ADAuthenticationPolicySilo -Name "Tier-0" -Description "Authentication policy silo to control the scope of logon for administrators" -UserAuthenticationPolicy "Tier-0_TGT_120mins" -ComputerAuthenticationPolicy "Tier-0_TGT_120mins" -ServiceAuthenticationPolicy "Tier-0_TGT_120mins" -Enforce -ProtectedFromAccidentalDeletion $True
#Modify the policy to allow TGT issuance only if the silo is a match
Set-ADAuthenticationPolicy -Identity "Tier-0_TGT_120mins" -UserAllowedToAuthenticateFrom "O:SYG:SYD:(XA;OICI;CR;;;WD; (@USER.ad://ext/AuthenticationSilo == 'Tier-0'))"
#Grant access to the silo to the admins and their systems
Grant-ADAuthenticationPolicySiloAccess -Identity "Tier-0" -Account "CN=Pierre,OU=_Admins,DC=contoso,DC=com"
Grant-ADAuthenticationPolicySiloAccess -Identity "Tier-0" -Account "CN=WKS1,OU=_Admins,DC=contoso,DC=com"
Grant-ADAuthenticationPolicySiloAccess -Identity "Tier-0" -Account "CN=DC1,OU=Domain Controllers,DC=contoso,DC=com"
#Assign the silo to the admins and their systems
Get-ADUser -Identity Pierre | Set-ADAccountAuthenticationPolicySilo –AuthenticationPolicySilo "Tier-0"
Get-ADComputer -Identity WKS1$ | Set-ADAccountAuthenticationPolicySilo –AuthenticationPolicySilo "Tier-0"
Get-ADComputer -Identity DC1$ | Set-ADAccountAuthenticationPolicySilo –AuthenticationPolicySilo "Tier-0"
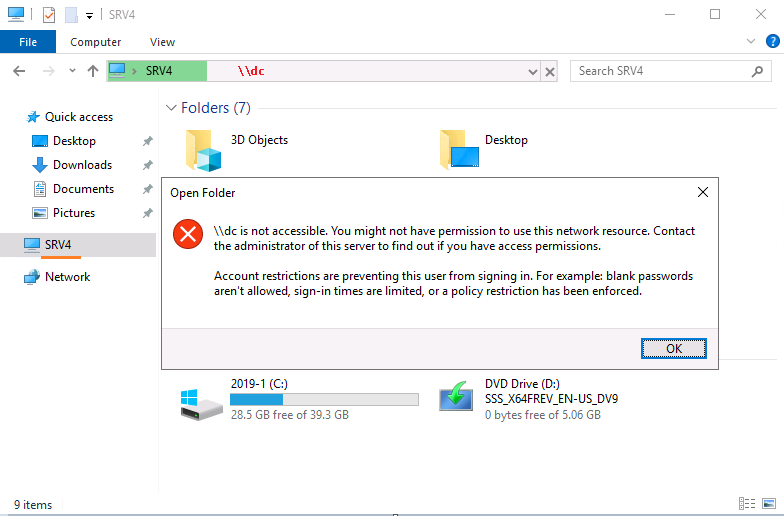
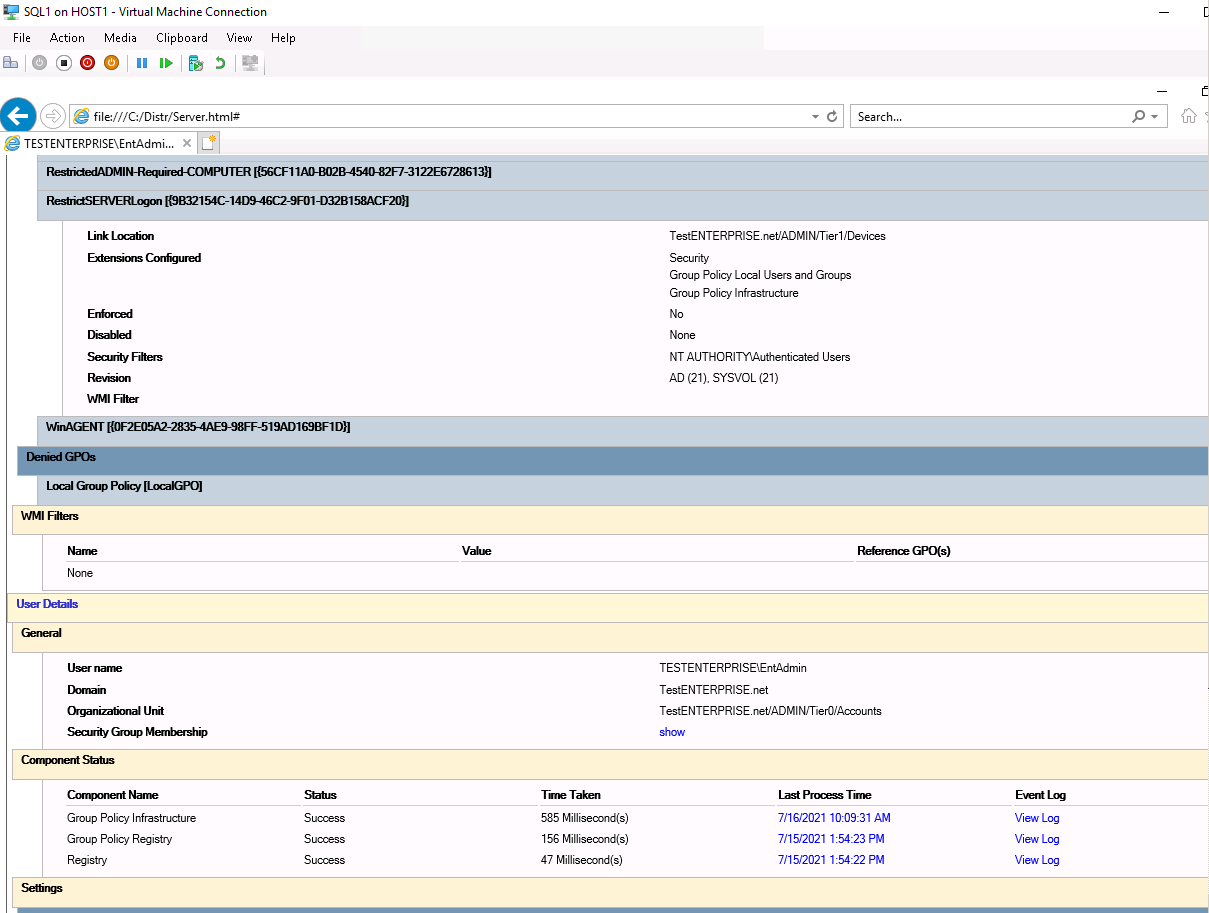
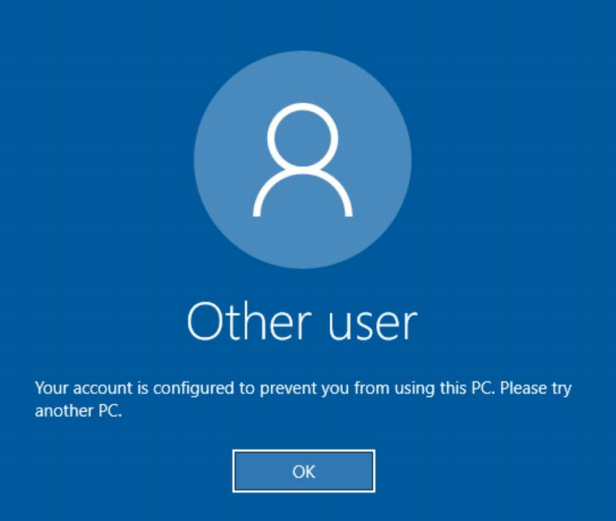
Then Pierre can only log on WKS1 and DC1. If Piere tries to log in on a system which is not a member of the silo, he gets the following error message:
Let me know if you want to know more about this. If so, I would suggest you create a new thread.