Any other further update on this issue please? even now, the Pull requests to ACR from function app goes with oubtound public IP of ASE
App Service in internal App Service Environment v3 pulls docker-image over public outbound IP of ASE
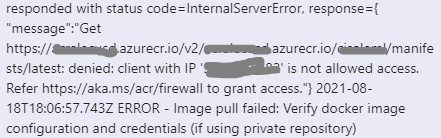
I have an internal ASEv3 provisioned into my VNet. An App Service deployed in the ASEv3 needs to pull the container-image from an ACR in the same VNet. The ACR has disabled all public network access and uses a private endpoint for communication. The App Service tries to pull the docker-image over the public outbound IP address of the ASE which results in the following error-message inside the "Deployment Center - Logs" of my App Service:
ERROR - DockerApiException: Docker API responded with status code=InternalServerError, response={"message":"Get https://myregistryxxxyyy.azurecr.io/v2/my-app/manifests/2021.1.7-appinsightsx: denied: client with IP '20.xx.xxx.xx' is not allowed access. Refer https://aka.ms/acr/firewall to grant access."}
My current workaround is to allow this public IP inside the firewall settings of the ACR.
But how can I tell the App Service to communicate over my VNet only? I already set the env-variables WEBSITE_VNET_ROUTE_ALL=1 and WEBSITE_PULL_IMAGE_OVER_VNET=true.
2 answers
Sort by: Newest
-
-
 Ryan Hill 26,241 Reputation points Microsoft Employee
Ryan Hill 26,241 Reputation points Microsoft Employee2021-08-04T14:57:36.687+00:00 Hi @Harald Reinmueller ,
When using regional VNET routing, make sure you have the following app settings configured
- DOCKER_REGISTRY_SERVER_URL
- DOCKER_REGISTRY_SERVER_USERNAME
- DOCKER_REGISTRY_SERVER_PASSWORD
Otherwise, it will fall back to public route.
EDIT: See https://azure.github.io/AppService/2021/07/03/Linux-container-from-ACR-with-private-endpoint.html. You need to use Azure DNS so that it properly resolves the private endpoint within the VNET.