Extended Validation support for websites using internal certificates
Hey all Rob here again. One feature that that is new with Windows Server 2008R2 / Windows 7 is the ability to configure your internal certification authority hierarchy in order to issue certificates that can show as Extended Validation certificates.
So for those of you who do not know, this means that you will get a shaded green bar within Internet Explorer proving that a site is ‘extra trustworthy’. If you want to learn more about extended validation click here. The feature works on the following operating system / IE Versions:
- Windows XP SP3/ 2003 SP2 – Internet Explorer 8.
- Windows Vista SP1/Windows Server 2008 – Internet Explorer 7 and 8.
- Windows 7/2008R2 – Internet Explorer 8.
Enabling this feature is a two step process to configure:
Create a new “Issuance Policy” on a certificate template to support EV certificates:
The below steps require you to be logged in as an Enterprise Admin unless you have modified the permissions on your certificate templates.
1. Open the Certificate Templates MMC (CertTmpl.msc).
2. Create a new Version 2 or Version 3 template (or modify an existing v2/v3 template).
3. Click on the Extensions tab.
4. Select Issuance Policies, and click on the Edit button.
5. Click the Add… button.
6. Click New… button.
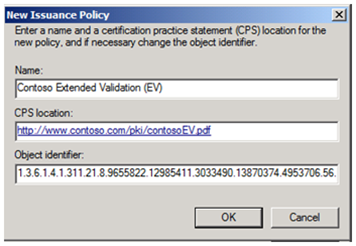
7. Type in a name for the new Extended Validation Policy. The name for the policy can be anything you like. In my example I used “Contoso Extended Validation (EV) ” as the name.
8. Type in the URL to the Certificate Practice Statement (CPS) for your extended validation policy.
NOTE: When you create a certificate policy you should have a practice statement defining how the certificate type is to be used, how the certificate type is approved to be issued, and what the requirements are to be fulfilled before issuance. CPS’s are beyond the scope of this blog however and you should do your due diligence in crafting a CPS.
9. The Object Identifier field will be filled out. You can of course replace this with an custom OID (that you obtained) from an internet authority that manages OIDs. Be sure to document and copy this OID for later use.
10. Click OK
11. Highlight the Issuance Policy you just created and click OK.
12. Do not check “Make this extension critical” and click OK.
13. Click “OK” to close the certificate template dialog box.
Create / modify a Group Policy to support the feature:
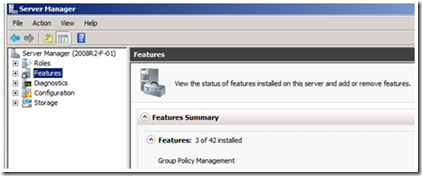
It’s actually pretty easy to setup, you will need either a Windows Server 2008R2 / Windows 7 client with RSAT tools (GPMC) installed, or a 2008R2 server with the Group Policy Management feature added .
It is important to note, that it is not required that you have a Windows Server 2008 R2 domain controller, you only need the ability to manage group policies from the newer operating system.
1. Launch Group Policy Management (GPMC.MSC).
2. Edit an existing policy / create a new policy.
3. Navigate to the following location: Computer Configuration\Policies\Windows Settings\Security Settings\Public Key Policies\Trusted Root Certification Authorities
4. Right click on Trusted Root Certification Authorities and select Import
5. You need to import your internal Root Certification Authority certificate using the import wizard.
6. Once the Root Certification Authority certificate has been imported, right click on the certificate and select “Properties”
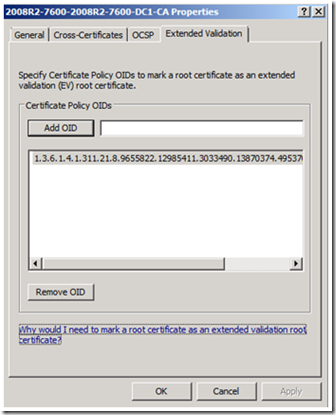
7. Click on the Extended Validation tab.
8. Paste in the OID from Issuance Policy you created above.
9. Click the Add OID button.
10. Click OK.
Have fun with Extended Validation and enjoy your green validated address bar in Internet Explorer.
- Rob ‘OID vey!’ Greene