Step-By-Step: Deploying ReFS
Hello folks,
In this series, we’ve looked at deploying or leveraging the goodness of Windows Server 2012. we’ve looked at VDI, Data Deduplication, DirectAccess, Hyper-v among others…
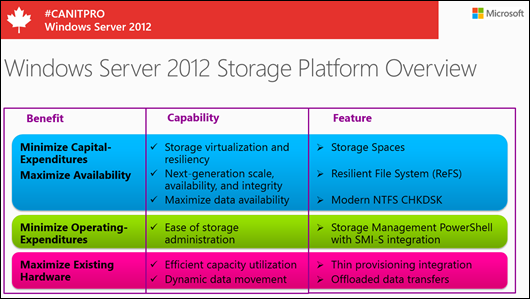
Today we’ll look at ReFS. It’s part of the Windows Server 2012 Storage Platform. It has been designed from the ground up to meet a broad set of customer requirements, for all the different ways that Windows is deployed. ReFS interfaces with Storage Spaces to automatically fix corruption.
We’ve already covered Storage Spaces & Thin provisioning. So, we’ll concentrate on ReFS for this post.
ReFS inherits the features and semantics from NTFS including BitLocker encryption, access-control lists for security, USN journal, change notifications, symbolic links, junction points, mount points, reparse points, volume snapshots, file IDs, and oplocks.
ReFS is very well suited for the following:
- General-purpose file server. Customer deploys a file server attached to a JBOD storage configuration with Serial ATA (SATA) or Serially Attached SCSI (SAS) drives.
- Consolidated remote application data storage. Customer deploys a scale-out, two-node file server cluster with Storage Spaces, in which the cluster uses a shared JBOD storage configuration with SATA or SAS drives.
However, before we go any further, let me state that ReFS supports the majority of the Win32 APIs, but there are certain features that ReFS does not support.
- Legacy stuff like Short Names and TxF (or Transactional NTFS)
- NTFS-specific features like named streams, object IDs, short names, compression, file level encryption (EFS), user data transactions, sparse, hard-links, extended attributes, and quotas
- and for those of you who looked at my Data Deduplication post , deduplication is not supported on ReFS.
deploying it is very easy. You do not need a Storage Pool to use ReFS, (you can just create a volume with the ReFS file system,. However, Storage Spaces protects data from partial and complete disk failures by allowing you to maintain copies on multiple disks. On read failures, Storage Spaces is able to read alternate copies, and on write failures (as well as complete media loss on read/write) it is able to reallocate data transparently. Many failures don’t involve media failure, but happen due to data corruptions, or lost and misdirected writes.
These are exactly the failures that ReFS can detect using checksums. Once ReFS detects such a failure, it interfaces with Storage Spaces to read all available copies of data and chooses the correct one based on checksum validation. It then tells Storage Spaces to fix the bad copies based on the good copies. All of this happens transparently from the point of view of the application
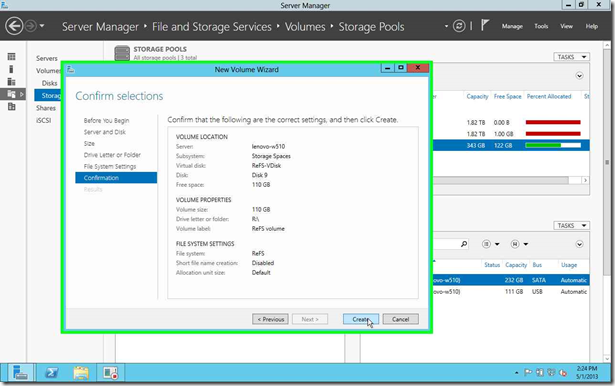
In our case we already have a Storage Pool created with a Mirrored disk created. we called it ReFS-VDisk.
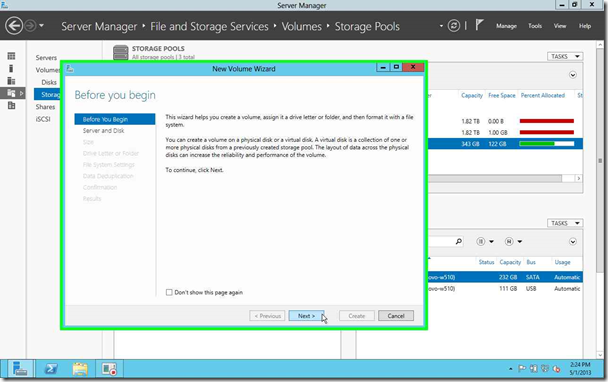
1- Using Server manger, in the “File and Storage Services, we create a new volume.
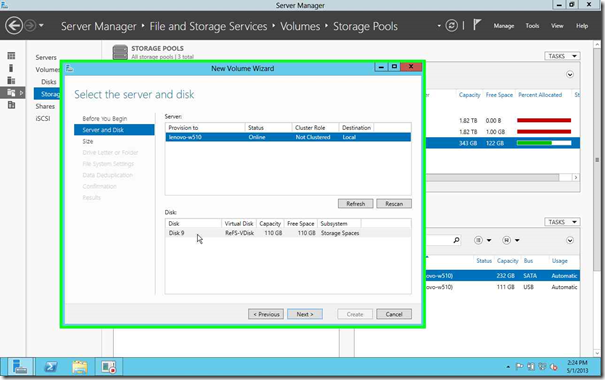
2- In the “New Volume Wizard” we select the Server and disk we want to use.
in our case as mentioned we selected a Virtual disk built on a Storage Pool, with 2 mirrored drive. and click Next
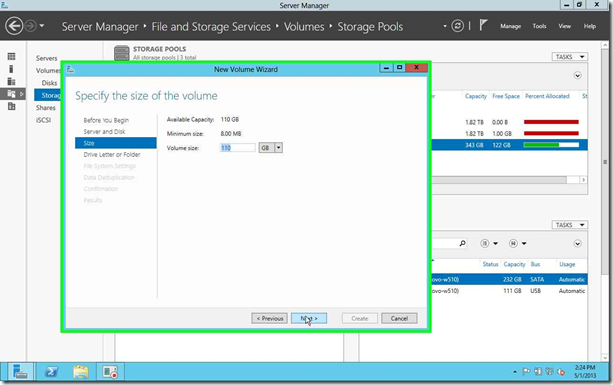
3- We allocated the maximum capacity, and click Next.
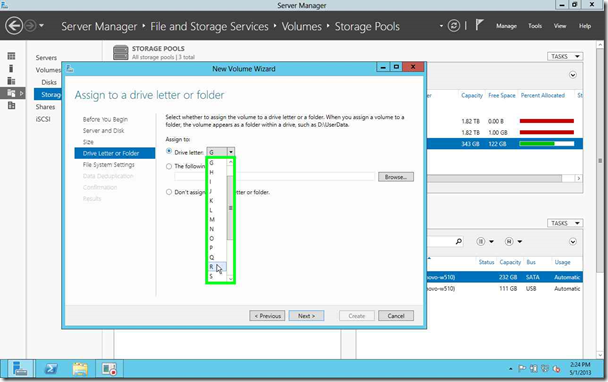
4- I like to use drive letters that make sense to me… so I selected the letter “R” for “Resilient”. and click Next,
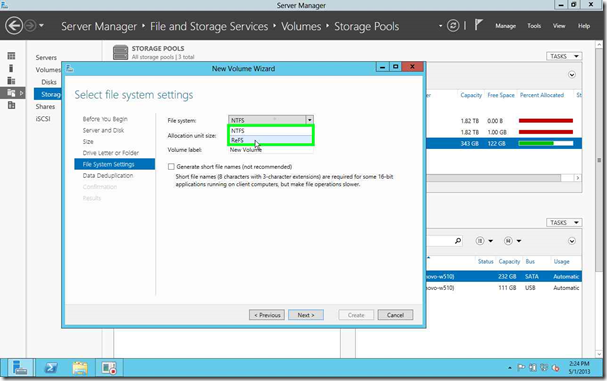
5- When asked to select a File System, Select ReFS instead of NTFS. and click Next, you can also give it a volume name that is representative, so we called our “ReFS Volume”,
9- click “Create” to complete the creation on the ReFS volume.
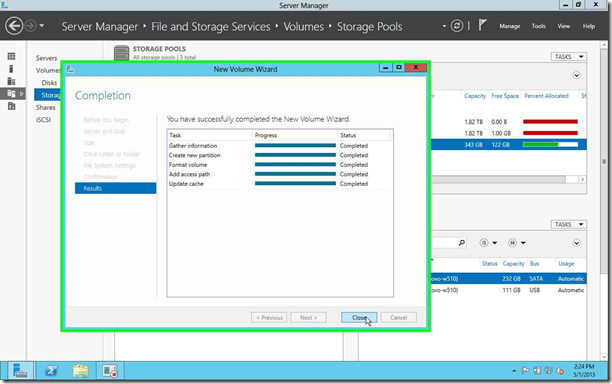
10- The server will Create and format the volume, when completed you can click “Close”.
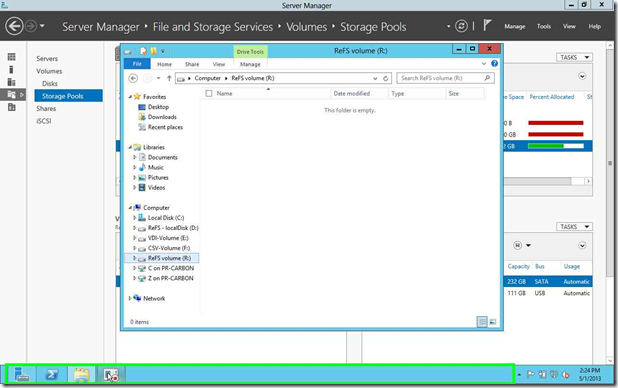
11- as you can see in File Manger, the volume is created.
We are done!. We have create a ReFS volume that will allow us to safeguard our data from corruptions.
if you want to see a really cool demo of the results of that corruption protection? please look at the following recording of Rick Claus’ session at TechEd (the ReFS demo is at time index 0:48:35)
That’s it. Are you waiting for corruption to wipe your data? Use the Windows Server 2012 evaluation copy to try this in your own environment and see how you can protect your business from corruption.
Cheers!
Pierre Roman, MCITP, ITIL | Technology Evangelist
Twitter | Facebook | LinkedIn
More resources
- Storage Spaces FAQ
- How to Configure Clustered Storage Spaces in Windows Server 2012
- Virtualizing Storage for Scale, Resiliency, and Efficiency
- Resilient File System Overview
![Signature_thumb[3] Signature_thumb[3]](https://msdntnarchive.blob.core.windows.net/media/TNBlogsFS/prod.evol.blogs.technet.com/CommunityServer.Blogs.Components.WeblogFiles/00/00/00/48/12/metablogapi/5635.Signature_thumb3_thumb_5D3BD63C.jpg)