Step-By-Step: Enabling A Primary AD FS Server in Azure for Office365 Single Sign-On
This Step-By-Step will provide instruction to setup a primary AD FS 3.0 server on a Windows Server 2012 R2 virtual machine in Azure. This post will accomplish the following:
Create the Azure Cloud Service
Build the Azure virtual machine
Install the AD FS 3.0 role
Configure AD FS 3.0
Federate with Office365
Microsoft Virtual Academy provides a great precursor to this Step-By-Step entitled: Managing Office 365 Identities and Services
Assumptions:QA
- Azure account is setup
- Directory Sync is activated, setup and running
- Valid SSL certificate is available (with private key)
- VPN connection setup from Azure to your on premise network
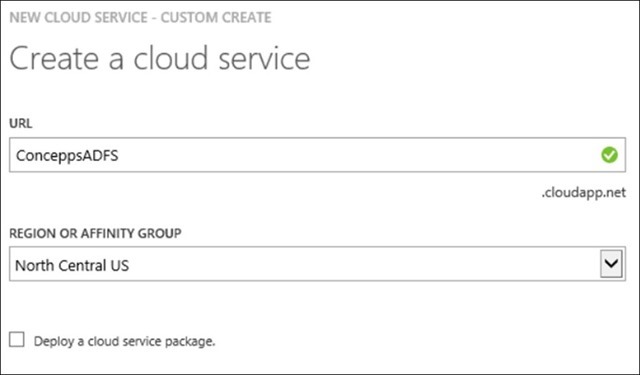
Step 1: Create a New Cloud Service
Because we are going to load balance one or more virtual machines, we need to create a Cloud Service to put them in. Think of it as a bucket to hold your virtual machines. You will require one for the AD FS Servers and one for the Web Application Proxies (AD FS Proxy Servers)
Click New
Select Compute -> Cloud Service -> Custom Create
Enter a URL or Name for the Cloud Service. This name must be unique across the .cloudapp.net name space.
Select your Region or Affinity Group
Click OK
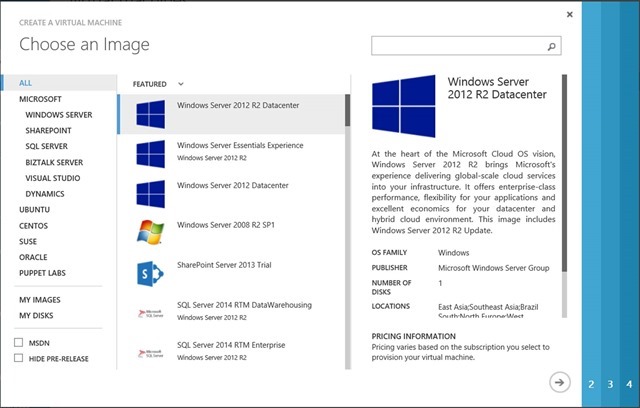
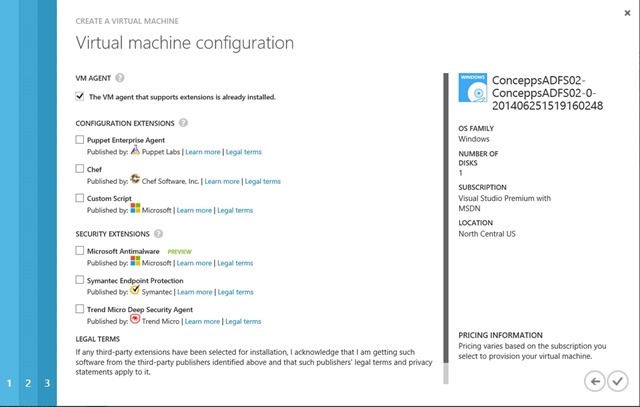
Step 2: Create the Virtual Machine in Azure
Click New
Select Compute -> Virtual Machine -> From Gallery
Choose Windows Server 2012 R2 Datacenter
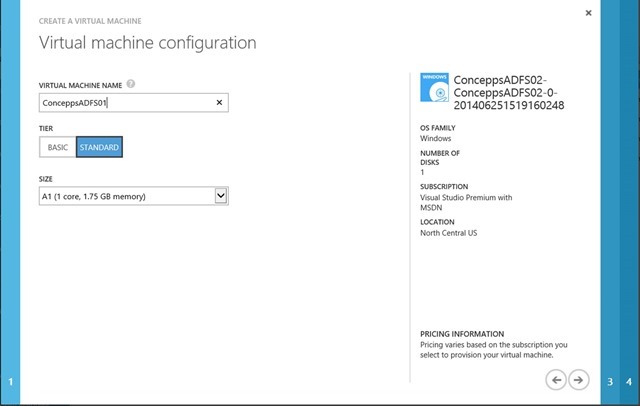
Enter Virtual Machine Name
Select Server Tier
Select Server Size
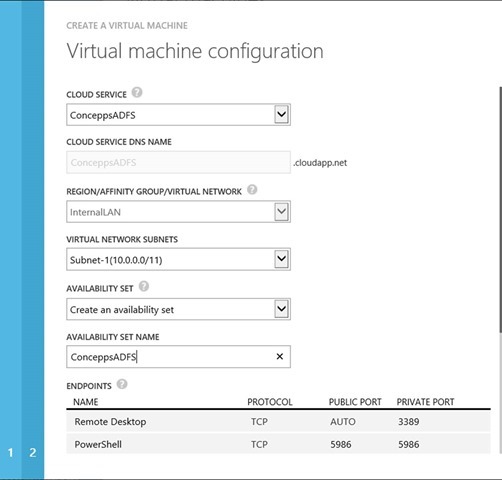
Select the AD FS Cloud Service that was created earlier. This is very important.
Step 3: Verify Subnet
Drop down to Create an availability set
Enter name for the availability set
NOTE: This does not load balance the servers, it will just place the VM accordingly so that if a rack of servers goes down, all the members of the set will be placed in different fault domains. This ensures that an outage isn’t extended to all the servers in the set.
Click Next
Once the VM is provisioned go to the next step
Step 4: Add the Server to the Domain
Since the AD FS server needs to authenticate against Active Directory, they need to be added to the local domain. Add the server to the local domain
Step 5: Install the Azure Active Directory Module for Windows PowerShell
Use this BLOG post to install the Azure Active Directory Module for PowerShell and the required Microsoft Online Services Sign-In Assistant 7.0
Connecting to Office365 with PowerShell
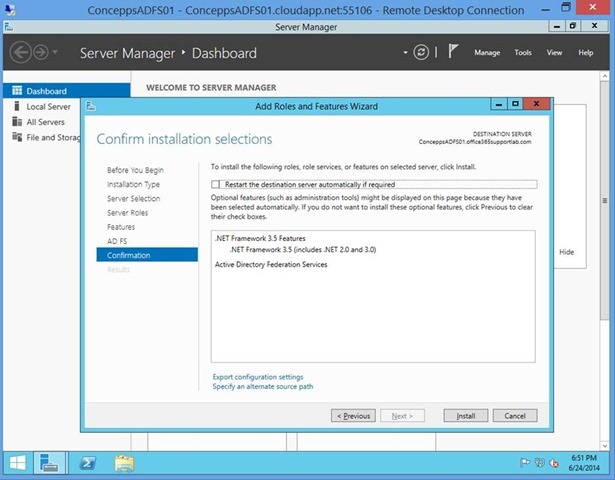
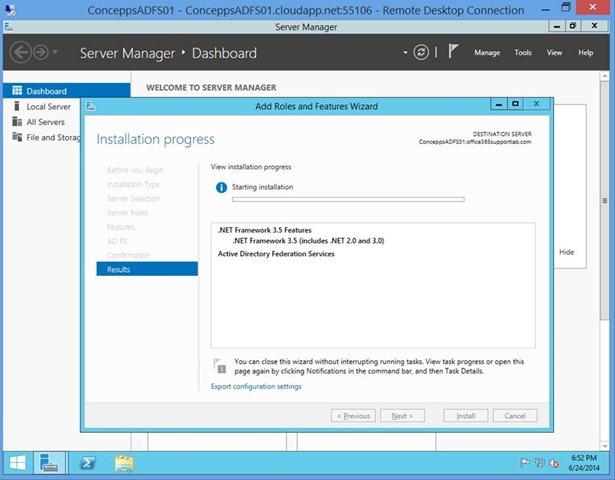
Step 6: Install the AD FS Role
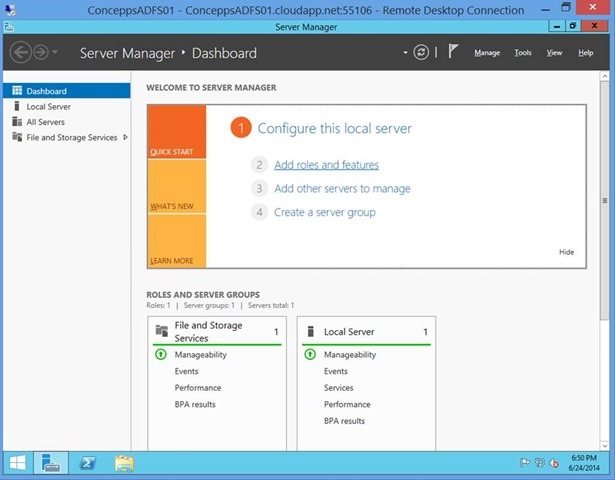
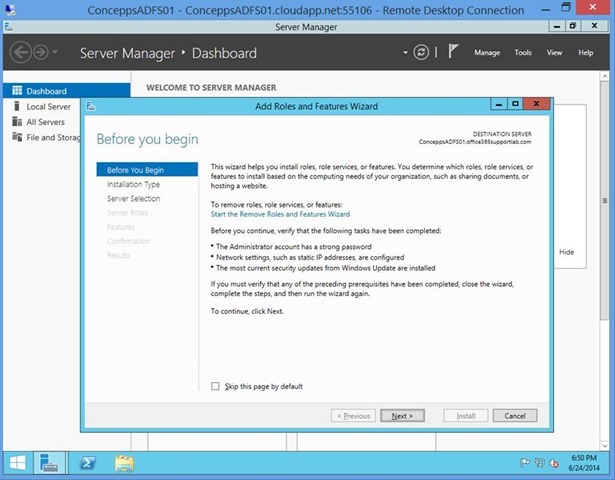
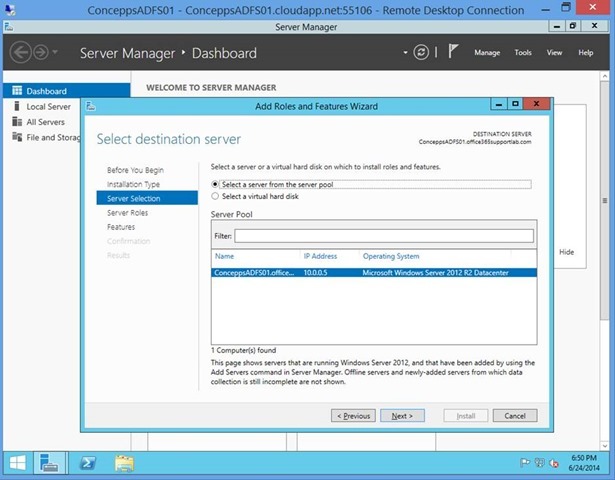
Open Server Manager
Click Add roles and features
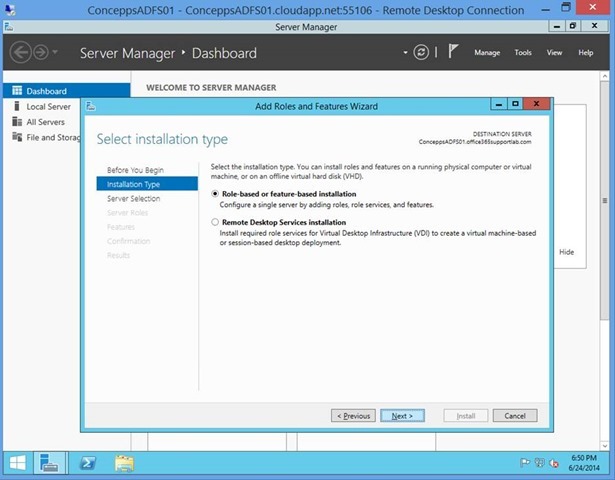
Select Role-based or feature-based installation
Make sure that the AD FS Server is listed as the server to install to
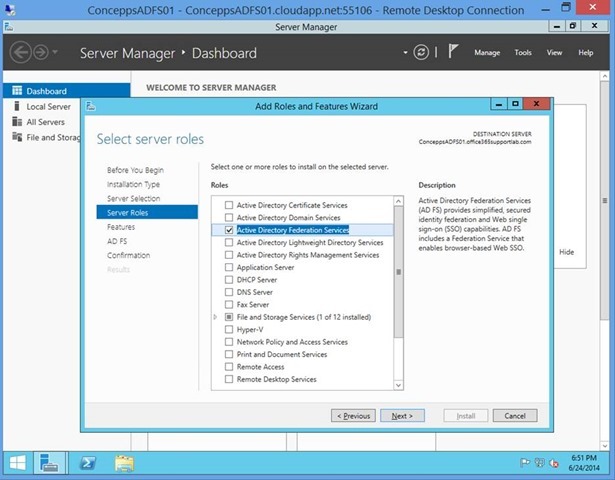
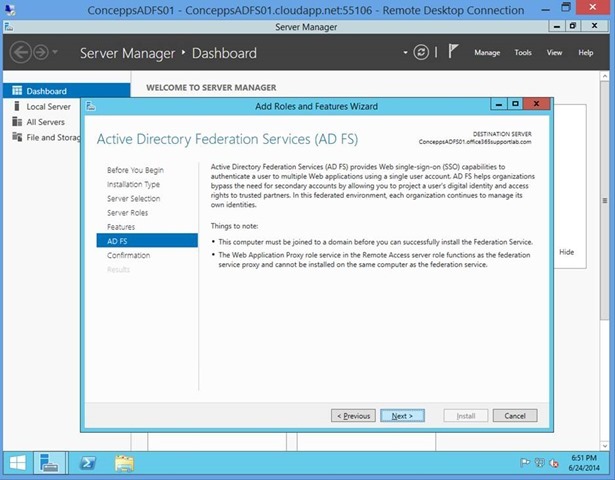
Select Active Directory Federation Services
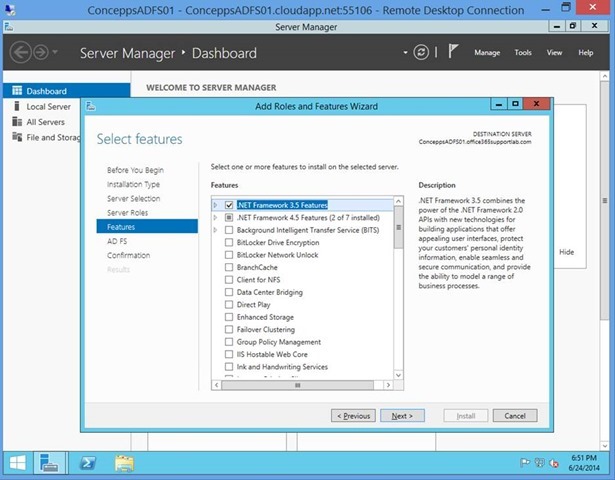
Leave defaults
Wait for the install to complete
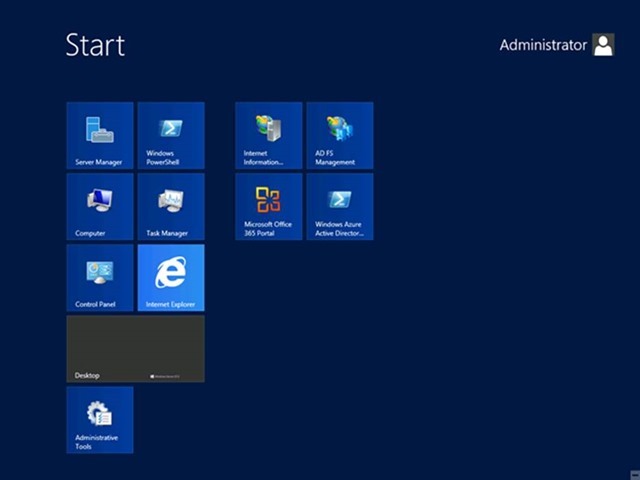
Step 7: Import the SSL Certificate
AD FS uses certificate to secure the connection from AD FS to Office365. For this reason, we need a valid SSL certificate. I choose to use GoDaddy, as I find they are a one stop shop for all my domain needs. It’s a personal choice, so use whoever you feel comfortable with. For the purposes of this BLOG post, I will use a multi-name certificate; I DON’T recommend this for a production environment. A couple reasons are that I like to keep things simple and if we have multiple names on the certificate, it starts to get complicated (not technically, but management of the certificate). Secondly, I don’t like to share certificates across services. This cuts down on the cross contamination from the support teams at larger companies. If you lump the AD FS services with the Exchange certificate, AD FS usually gets left in the dust and forgot about when it comes time to renew.
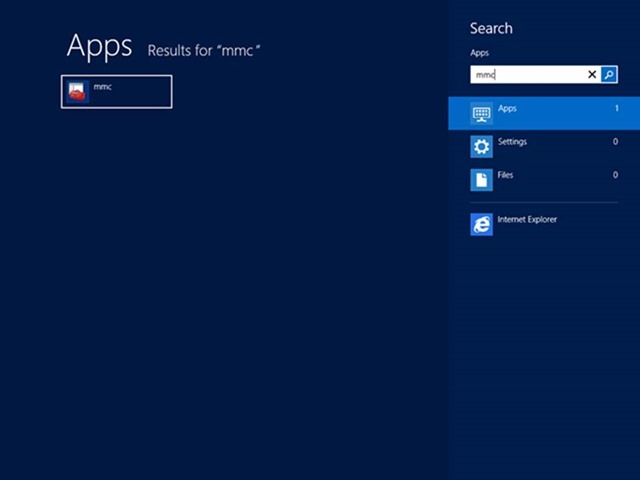
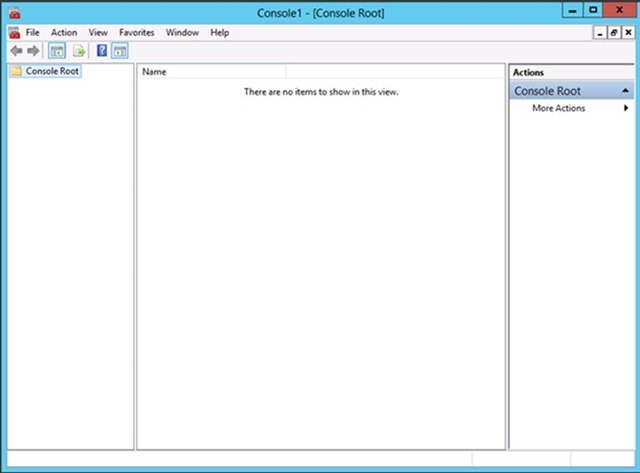
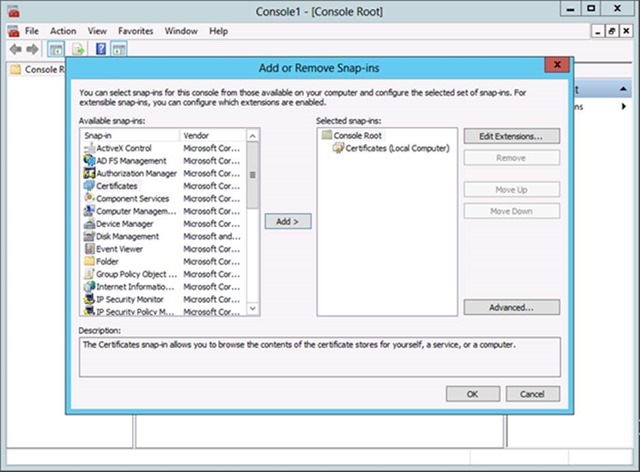
Type MMC
Click the MMC app
MMC opens
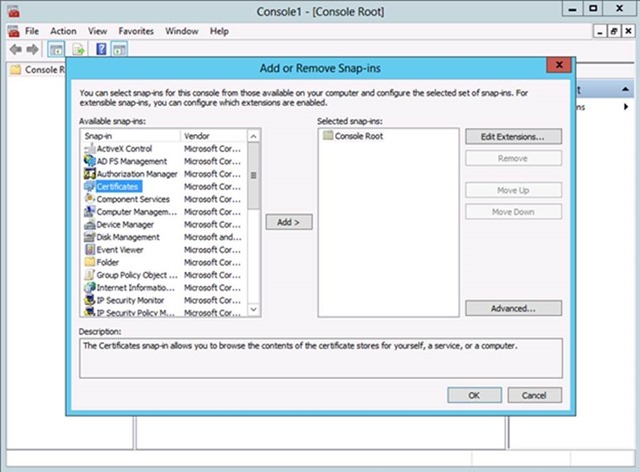
Click File
Click Add/Remove Snap-in
Select Certificates
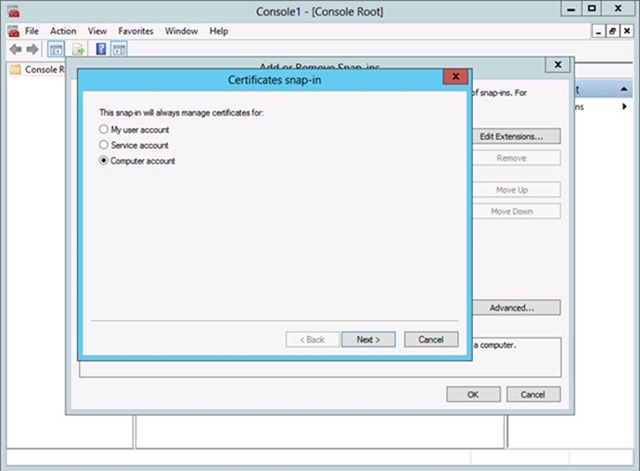
Select Computer Account
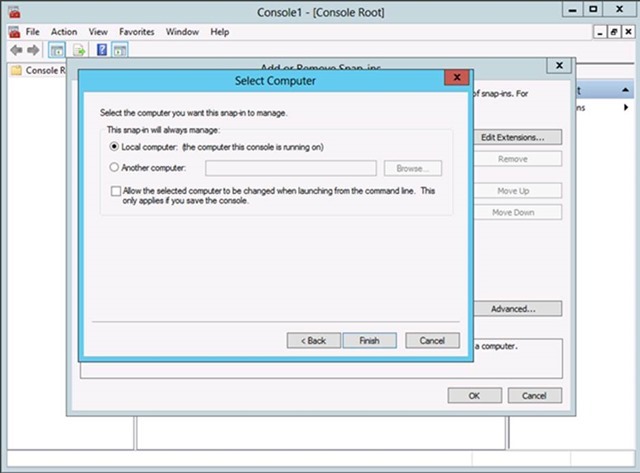
Select Local Computer
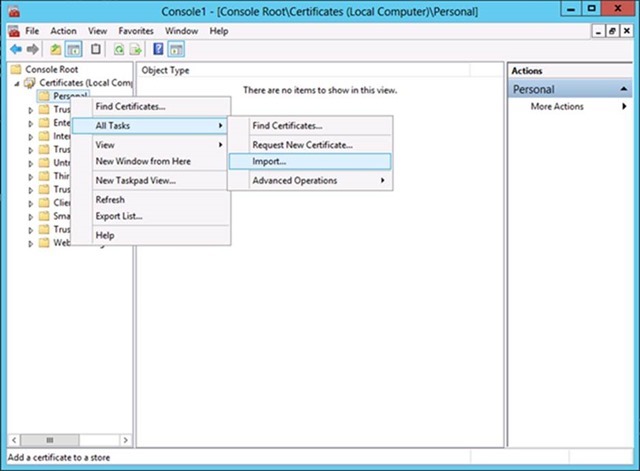
Expand Certificates
Expand Personal
Right Click Certificates
Select Local Machine
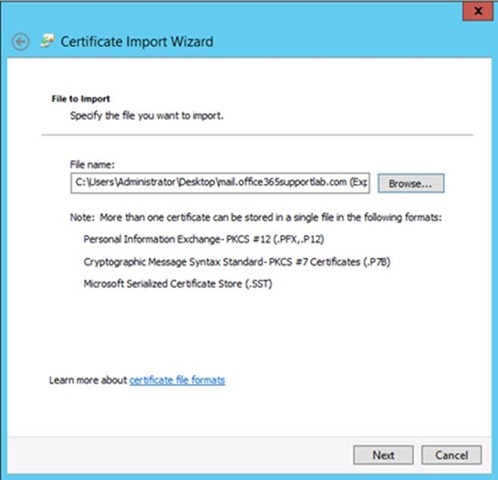
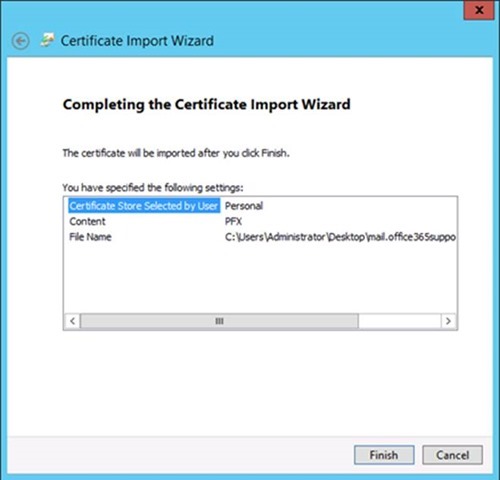
Browse to the Exported Certificate
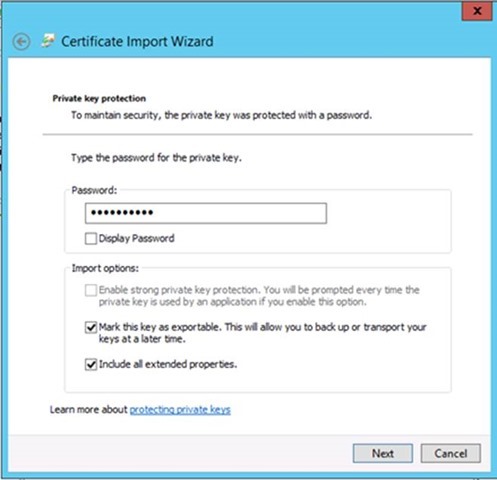
Enter Password
Mark the key as exportable
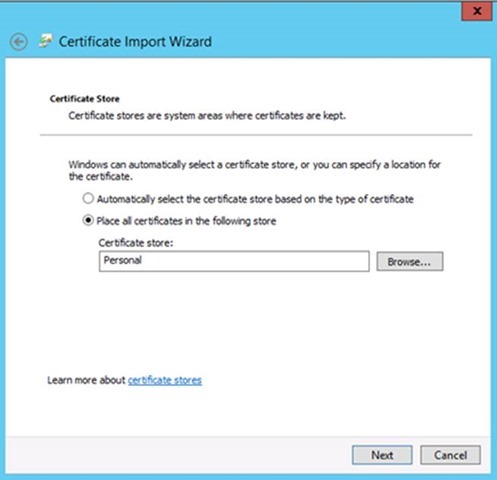
Place in the Personal certificate store
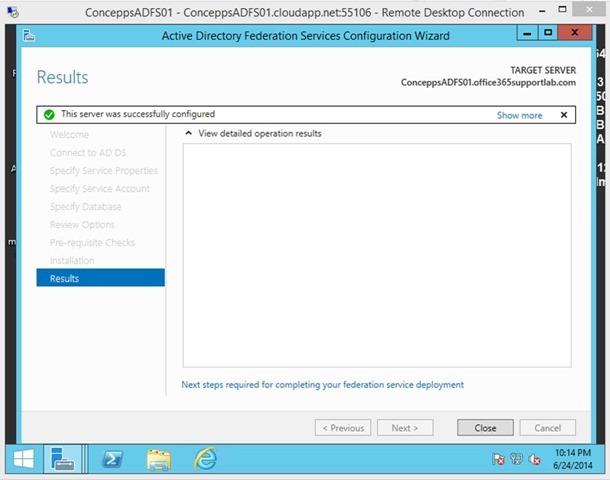
Step 8: Setup and Configure AD FS 3.0
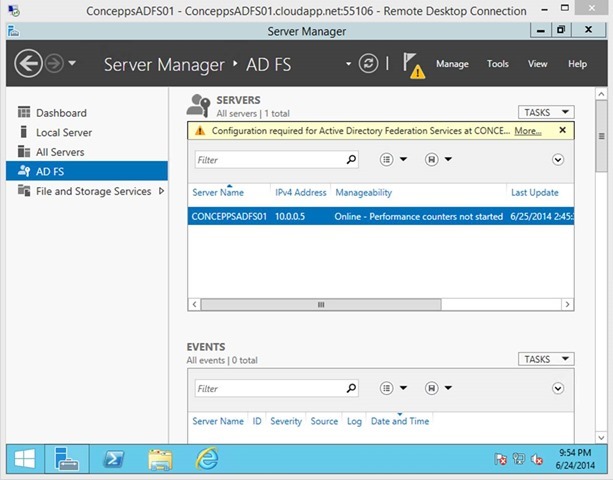
Open Server Manger
Select AD FS
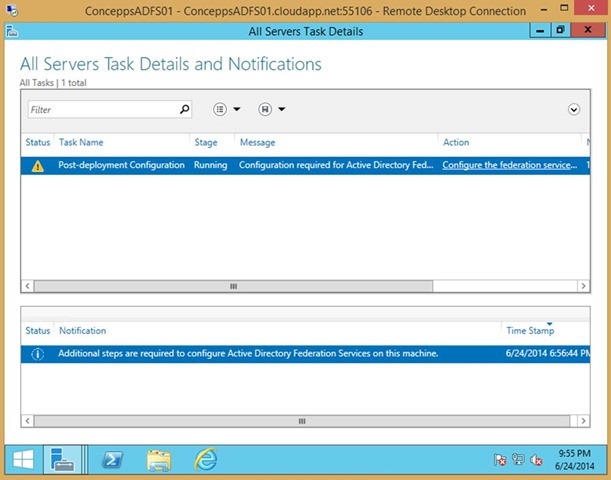
Click More… where it says Configuration required for Active Directory Federation Servers at…
Click Configure the federation service… action on the Post-Deployment Configuration
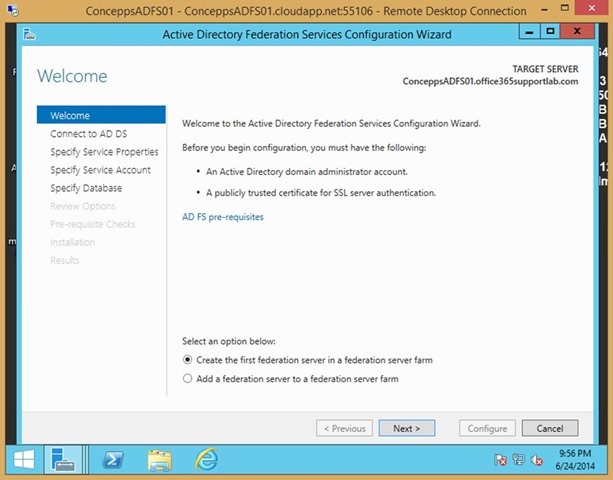
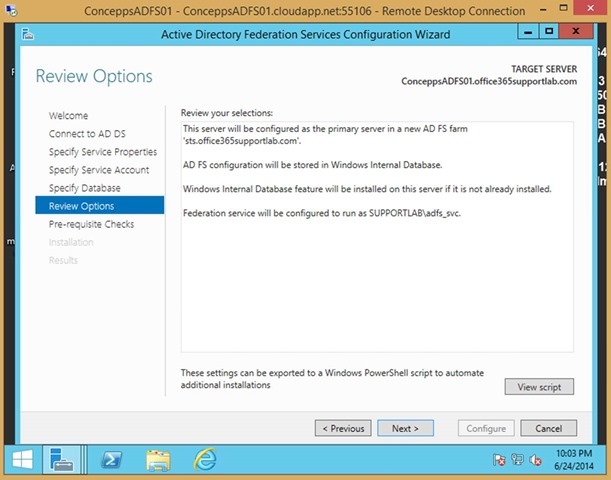
Select Create the first federation server in a federation server farm
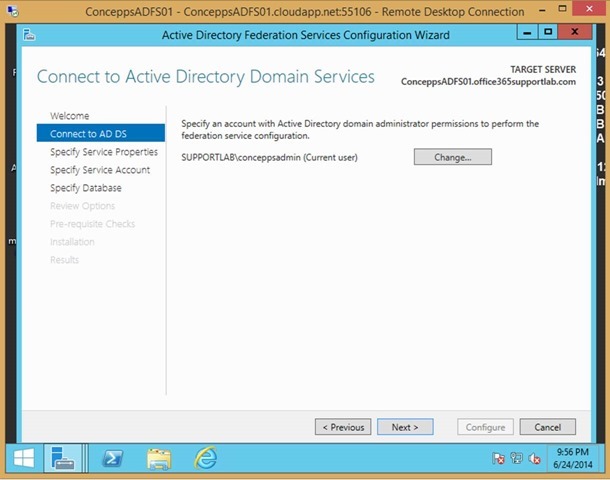
Enter credentials for a user that has domain administrator permissions. This is used to complete the install, it’s not used as the AD FS service account
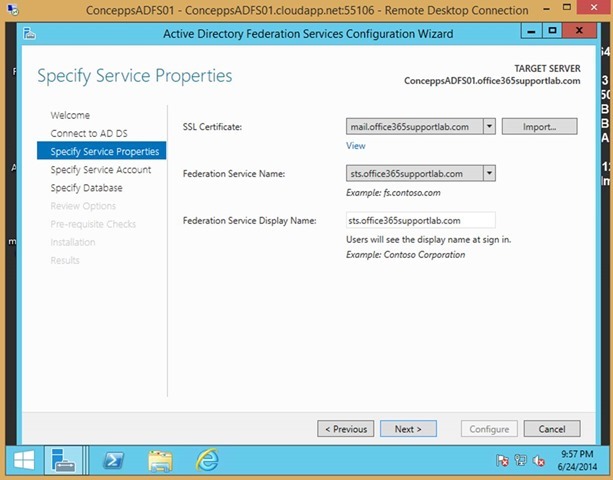
Select the SSL certificate that you imported
Select the Federation Service Name
Enter the Federation Service Display Name
NOTE: Since I am using a multi-name certificate these three values don’t match for me. In production I always recommend that you use a single name certificate to keep things simple. If that’s the case then the three values below should all match e.g. sts.domain.com
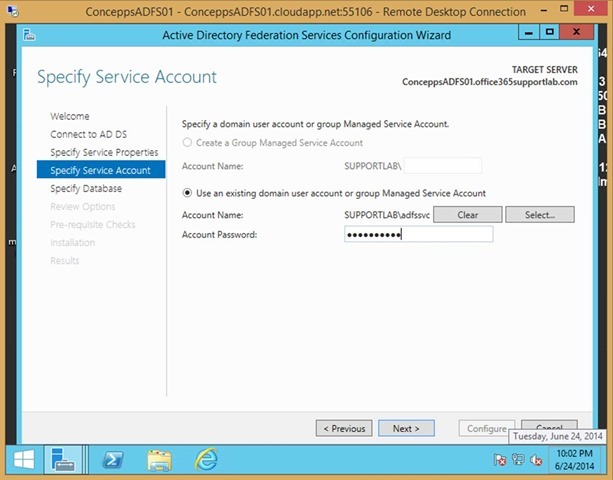
Enter the AD FS Service Account Name and Password
NOTE: This can be a managed service account or a domain user account designated for AD FS. If you use a domain user account, it does not need any special permissions. The install will give it the permissions required.
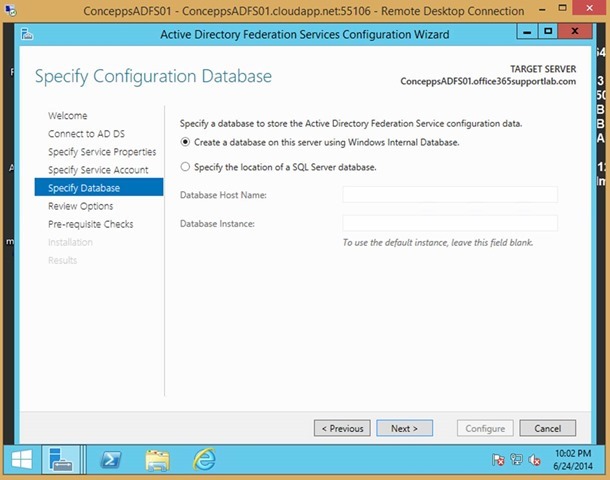
Select Windows Internal Database or the location of a SQL Server Database. The choice is yours, but for most companies the Windows Internal Database works just fine
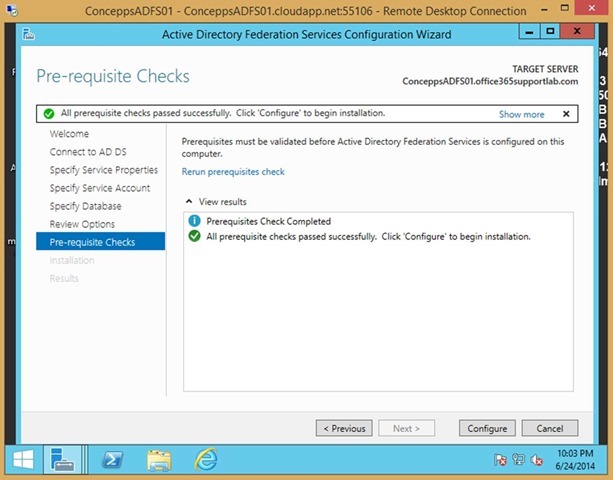
Wait for the Pre-requisite checks to be completed
Click Close
Step 9: Federate with Office365
Open the Desktop on the AD FS server
Find Azure Active Directory Module for Windows PowerShell
Right Click and Run As Administrator
Set the credential variable
$cred=Get-Credential
Enter a Global Administrator account from Office 365
Connect to Microsoft Online Services with the credential variable set previously
- Connect-MsolService –Credential $cred
Set the MSOL ADFS Context server, to the ADFS server (optional if you are on the AD FS server)
- Set-MsolADFSContext –Computer adfs_servername.domain_name.com
Convert the domain to a federated domain
- Convert-MsolDomainToFederated –DomainName domain_name.com
Successful Federation
- Successfully updated ‘ domain_name.com ‘ domain
Verify federation
- Get-MsolFederationProperty –DomainName domain_name.com
This concludes the setup of the first AD FS server and federation with Office365.