Step-By-Step: Setting up the new Azure AD Sync Tool
Hello Folks,
A while back, Anthony Bartolo wrote about Syncing An On Premise AD with Azure Active Directory. But on September 16th 2014 Alex Simons announced on his blog that Azure Active Directory Sync is now GA!.
So let’s revisit the topic and see how the new tool can help. as always, I recommend a few MVA modules to act as a primer if you’re not familiar with Microsoft Azure.
- Microsoft Azure IaaS Deep Dive Jump Start
- Get Started with Windows Azure Today Jump Start
- Windows Azure for IT Pros Jump Start
AAD Sync is our new directory synchronization tool that simplifies the process of connecting Azure AD to Windows Server AD. It also makes it more simple to connect complex, multi-forest deployments. It also has the capabilities to:
- Active Directory and Exchange multi-forest environments can be extended now to the cloud.
- Control over which attributes are synchronized based on desired cloud services.
- Selection of accounts to be synchronized through domains, OUs, etc.
- Ability to set up the connection to AD with minimal Windows Server AD privileges.
- Setup synchronization rules by mapping attributes and controlling how the values flow to the cloud.
- Preview AAD Premium password change and reset to AD on-premises.
If you just want to get started, you can download it here.
First, make sure you have uninstalled the old version of DirSync.. Then, to install AADSync, you need a computer running the Windows Server operating system.
- Windows Server 2008
- Windows Server 2008 R2
- Windows Server 2012
- Windows Server 2012 R2
Your target computer for installing AAD Sync can be stand-alone, a member server or a domain controller. and it must have the following components need installed:
- .Net 4.5
- PowerShell (preferably PS3 or better)
______________________________________________________________________
Note:
The tool needs an instance of SQL Server to store identity data. By default a SQL Express LocalDB is installed and the service account for the service is created on the local machine during the install.
Since Express has a 10GB size limit (it enables you to manage approximately 100.000 objects.) If you anticipate managing a higher volume of directory objects, you need to point the installation process to a different version of SQL Server.
______________________________________________________________________
Let Start
Account Required
To get all this working you will need 1 Account in your Azure AD (follow the same steps as in Anthony’s post.) And you’ll need an account in each forest you want to sync. The account only need the default read permissions. A regular user account in ADDS already fulfills this requirement. In our test Domain we will use the Administrator account.
Installing and configuring AADSync
1- download the tool from here.
2- Execute MicrosoftAzureADConnectionTool.exe.
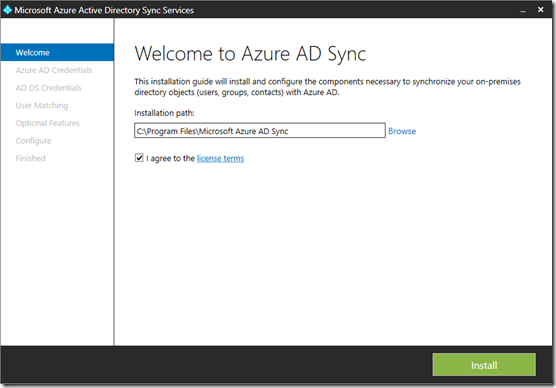
3- Once you get to the “Welcome to Azure AD Sync” dialogue box, Agree to the license terms and click Install
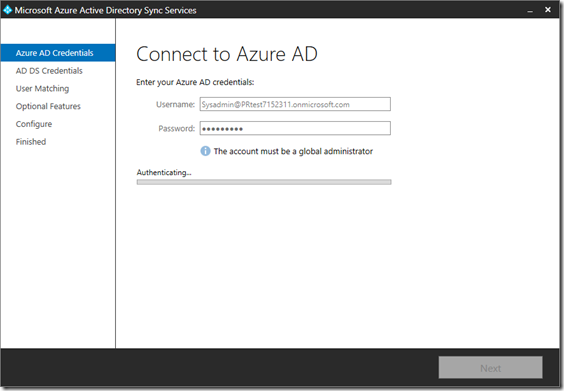
4- once it’s installed, the tool will start (it may take a few seconds) and once you get to Connect to Azure AD, Supply the credentials to connect to your Azure AD directory. (the global account you created earlier) I used a Global Admin in my directory in Azure called SysAdmin
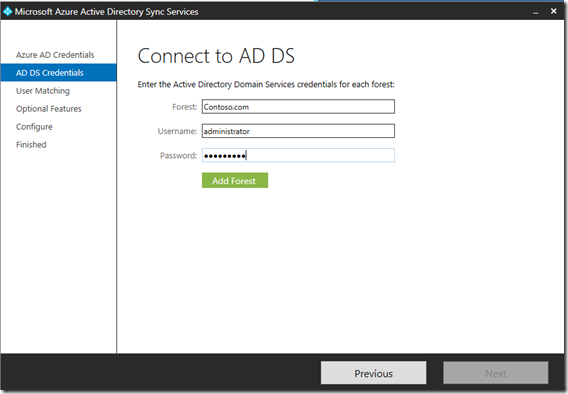
5- And as you would assume, you need to supply credentials for your local forest\domains to the Connect to AD DS dialogue box. And click “Add Forest” button and once you domain shows up. click next.
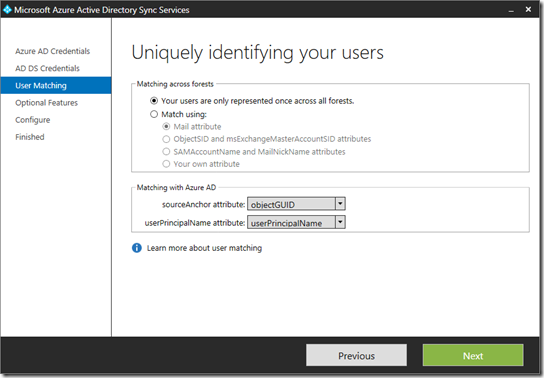
6- In the Uniquely identifying your users
you need to configure the following:
6.1- The Matching across forests feature allows you to define how users from your ADDS forests are represented in Azure AD.
A user might either be represented only once across all forests or have a combination of enabled and disabled accounts
6.2- You can use the Matching with Azure AD option to specify the attribute you want to use for identity federation. The sourceAnchor attribute is an attribute which is not changing during the lifetime of a user object. In single-forest and environments and where the account is never moved between forests, then objectGUID is a good candidate. If the user is moved between forests or domains, then an alternative attribute must be selected.
The userPrincipalName attribute is the user’s login ID in Azure AD. By default the userPrincipalName attribute in ADDS is used. If this attribute is not routable or not suitable as the login ID a different attribute, such as mail, can be selected in the installation guide.
click Next to move on to the Optional Features.
7- In the Optional features dialogue box, you can select Exchange hybrid deployment, if you have an Hybrid Exchange environment. For us we will NOT enable this setting. The password write-back is an Azure Active Directory Premium feature. (which we do not have enabled in our test environment so i will leave it checked off) and If you want to review or limit the attributes which are synchronized with Azure AD, then select Azure AD app and attribute filtering. You will then get two additional pages in the wizard. Right now we just want to get it synced, So we will leave that check off as well.
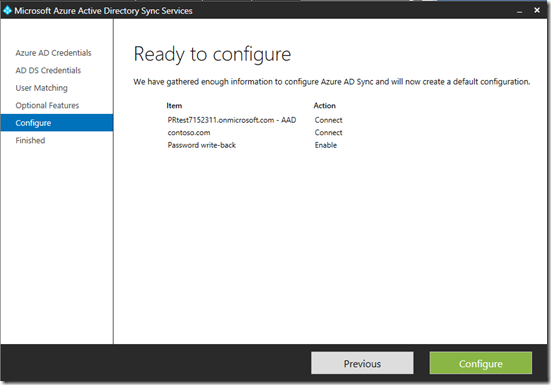
8- The Configure screen allows you to start the configuration process. just click “Configure”
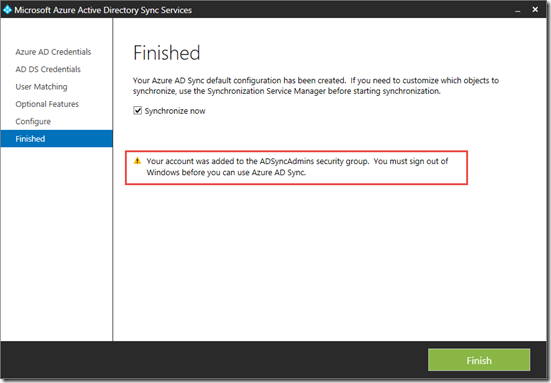
it will connect, and configure the sync rules and bring up the “Finished” screen. where if you leave the “Synchronize Now” once you click Finished it will start the sync process
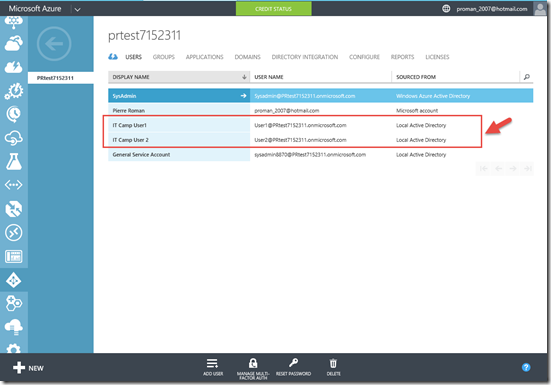
That’s it. We now have our Local directory synced in Azure.
Next week we will explore how we can specify attributed to be synced.
Cheers!
Pierre Roman, MCITP , ITIL | IT Pro AdvisorTwitter | Facebook | LinkedIn