Monitoring your UNIX/Linux Servers with System Center Operations Manager 2012
As I have discussions with different organizations, I learn about the tools utilized to monitor their various systems and services. They range from no to low cost and up to very high cost global monitoring systems. A common theme I hear is “we have way too may tools and need to consolidate”. Consolidation isn’t an overnight project, however there are steps that may be taken to remediate monitoring tool sprawl.
System Center 2012 R2, more specifically System Center Operations Manager 2012 R2 provides a single console to monitor something as simple as a service or as complex as a distributed application.
System Center Operations Manager 2012 R2 also provides web application probing from the inside and globally via Global Service Monitoring (think of it as an outside in approach), deep application monitoring down to code level for .NET and Java via Application Performance Monitor, system advisement via System Center Advisor where an online service collects data on workloads such as SQL Server, Exchange, Lync, Hyper-V, Active Directory, Windows Server, and provides alerting, analysis, and best practice information to help remediate potential issues.
System Center Operations Manager 2012 R2 also provides network monitoring and will provide alerts on network devices such as switches and routers. This functionality is useful in environments where systems administrators or engineers need to troubleshoot network issues before contacting the network team.
Organizations also have heterogeneous environments where Windows, UNIX, and flavors of Linux coexist. Having multiple monitoring and alerting technologies can be cumbersome, especially if the servers are managed by the same team.
Using System Center Operations Manager 2012 R2 agents to monitor Windows Servers is fairly straight forward. However monitoring UNIX/Linux servers requires a few more steps. Let’s take a look at what’s involved to prepare Operations Manager:
- Create accounts to be used for monitoring and agent maintenance.
- Add the created accounts to the appropriate UNIX/Linux profiles.
- Information on how to do 2 and 3 may be found here: https://technet.microsoft.com/en-us/library/hh212926.aspx
- Self-signed certificates are used by the agent (may be installed automatically with the agent or manually configured).
- The UNIX/Linux Management Pack is installed.
For the purposes of this this walk-through I am utilizing Ubuntu 12, however Operations Manager 2012 R2 supports the following flavors of UNIX/Linux via the free downloadable Management Pack: https://www.microsoft.com/en-us/download/details.aspx?id=29696
- AIX
- HP-UX
- Red Hat
- Solaris
- SUSE
- Universal Linux (Debian, CentOS, Ubuntu, etc.) – you may need to modify the GetOSVersion.sh file under “Program Files\Microsoft System Center 2012 R2\Operations Manager\Server\AgentManagement\UnixAgents” do so at your own risk. Make a copy of the file before editing.
Now let’s look at what’s involved to prepare a UNIX/Linux system
Because I installed a fresh instance of Linux, I needed to prepare the server. The following are items to verify before deploying agents to UNIX/Linux:
- The UNIX/Linux machine is on the network, with an IP, in DNS (the certificate uses the FQDN of the machine when signing it, more info in the troubleshooting section below), and can ping the Operations Manager server successfully.
- Install SSH on the server, and specify the port it will communicate on (Default is 22). This allows the OM 2012 agent to speak to the UNIX/Linux machine. For the purposes of this walk through I used openssh.
- Create an account that can be used for elevated permissions on your UNIX/Linux system.
- I simplified this process by only using user accounts. More secure options are available such as using login credentials and an SSH Key. More information may be found here: https://technet.microsoft.com/en-us/library/hh212886.aspx
DEPLOYING AGENTS
In the Operations Manager console navigate to Administration then expand Administration and then expand Device Management. Select UNIX/Linux Computers and right click and select Discovery Wizard. You can right click on any node and achieve the same results though.
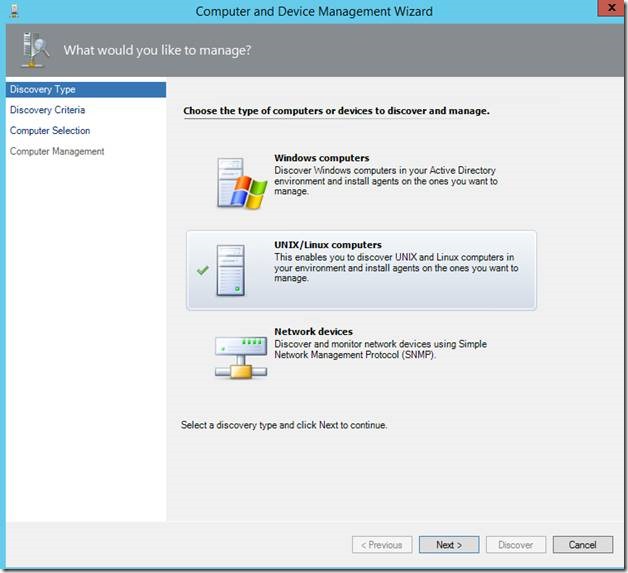
When the discovery wizard opens select UNIX/Linux Computers and select Next.
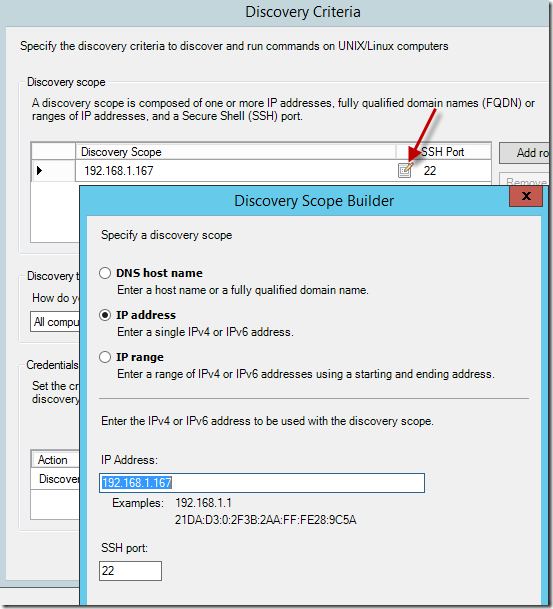
Under Discovery Criteria add the discover scope. The scope can be the FQDN of a system, a single IP, or a range of IPs as shown below. I only have one machine so I utilized the IP address.
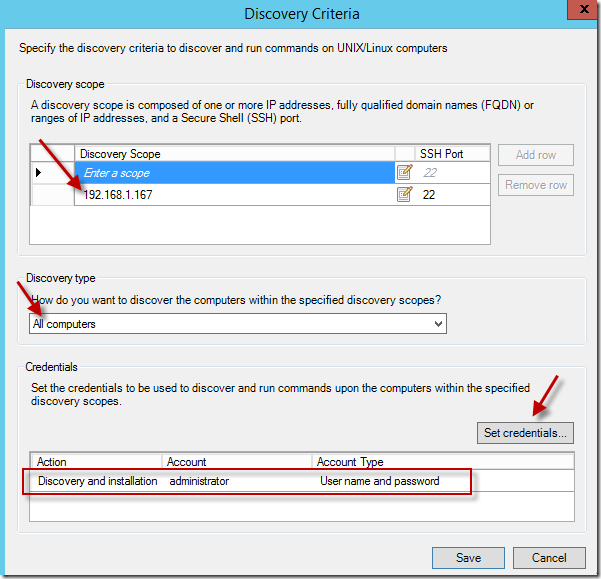
Next select the Discovery type and finally the credentials that will be used to contact and install the agent on the system. Select Save when finished.
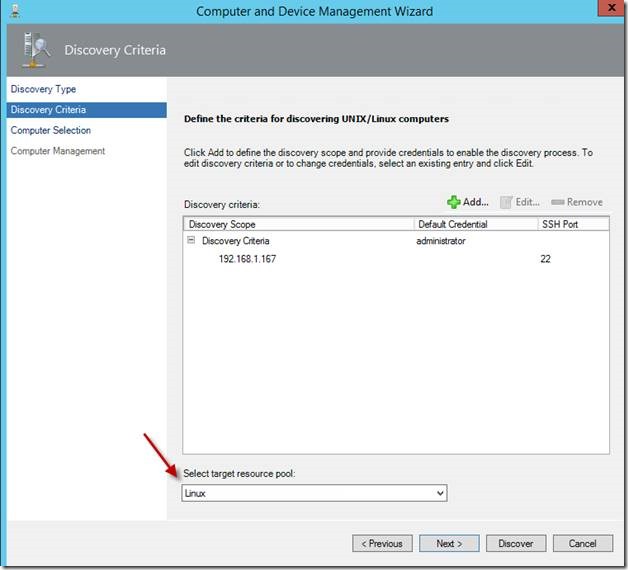
With the above step completed you’ll be taken back to the wizard. Select a target resource pool and select Discover.
Note, separate resource pools may be created, for example I’ve seen resource pools created for network devices, UNIX/Linux server, etc. Resource pools are good if you looking to distribute work across multiple management servers where the management servers in the resource pool will take over for failed management servers. More information on creating resource pools may be found here: https://technet.microsoft.com/en-us/library/hh230706.aspx
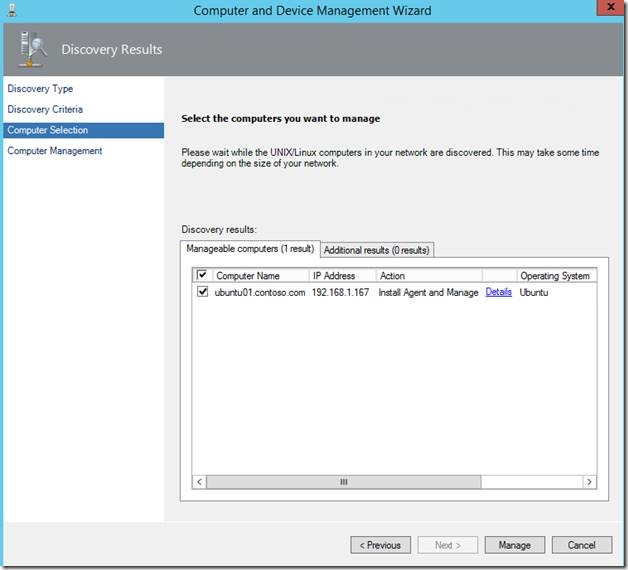
Once the UNIX/Linux systems are discovered check the systems you want to install the agent on and select Manage.
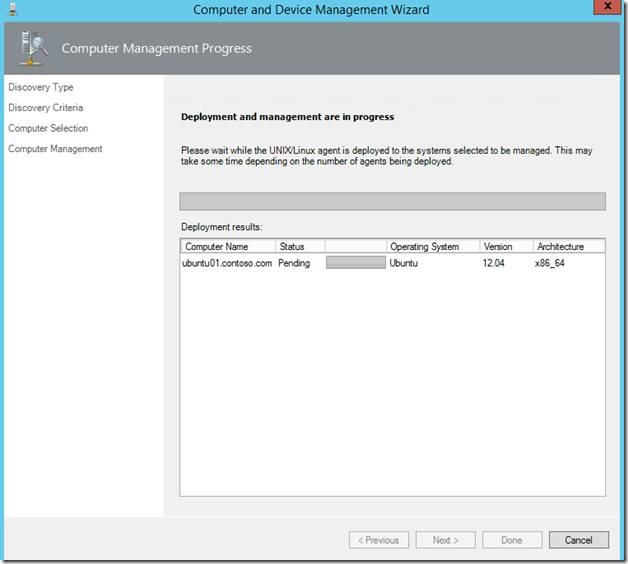
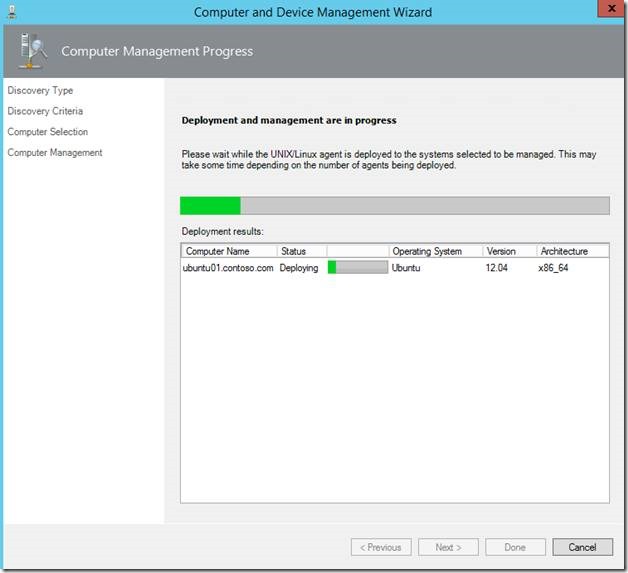
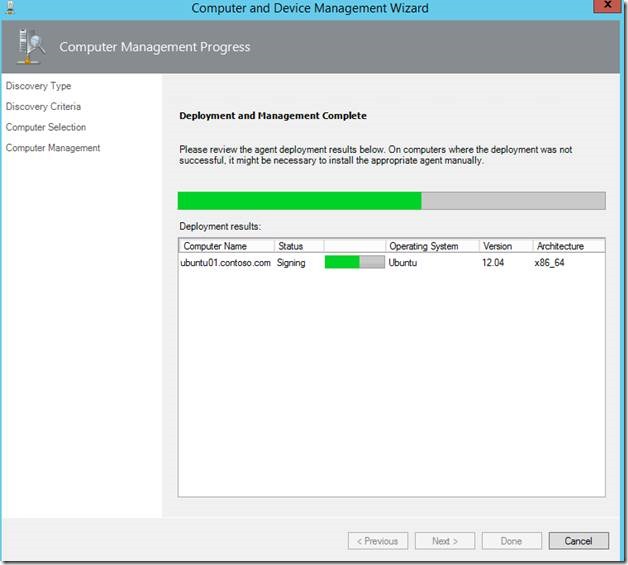
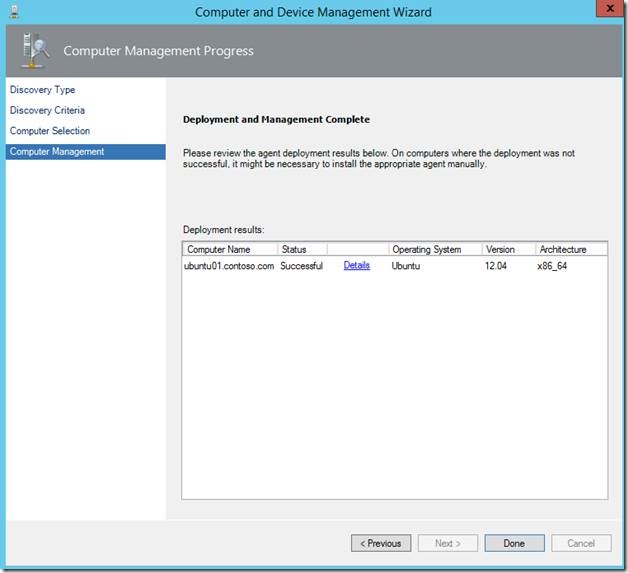
You’ll see the progress similar to the following images:
POST AGENT DEPLOYMENT
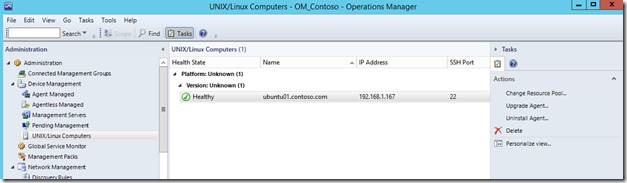
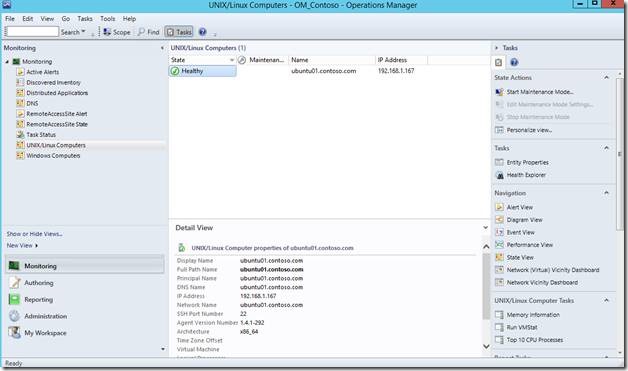
Once the agents are installed, wait a few minutes for data to populate and you will see the following:
In the Operations Manager console select Monitoring from the bottom left and select the UNIX/Linux Computers view.
You are also able to monitor processes, services, etc. by creating monitors under Authoring.
Thank you for reading through, that concludes the walk-through.
TROUBLESHOOTING
There are always nuances with any operating system and with the availability of multiple flavors of UNIX and Linux you may have to do a little troubleshooting. It’s important to have both environments prepared before attempting install the Operations Manager agents.
Troubleshooting UNIX/Linux Agent Discovery
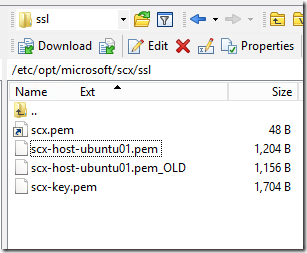
If the agent doesn’t register because of certification naming issues please view the following:
https://technet.microsoft.com/en-us/library/hh212851.aspx
The certificate is located in the following directory on the UNIX/Linux server: