How to Limit or Restrict the Use of Bootable Media Devices for OS Deployment Using SCCM
I have been on quite a few customer engagements where I have been asked to develop a process that will restrict the use of legacy media devices, such as DVD or UFD, to deploy OS images. Many of these customers come from legacy environments where they are used to building a unique image on DVD and must have a way to ensure an outdated image is no longer able to be deployed.
I will post later on how I was able to do this with a rare, non-networked, stand-alone media device, but for this post, I will focus on bootable media. Thankfully, SCCM makes this pretty easy for us.
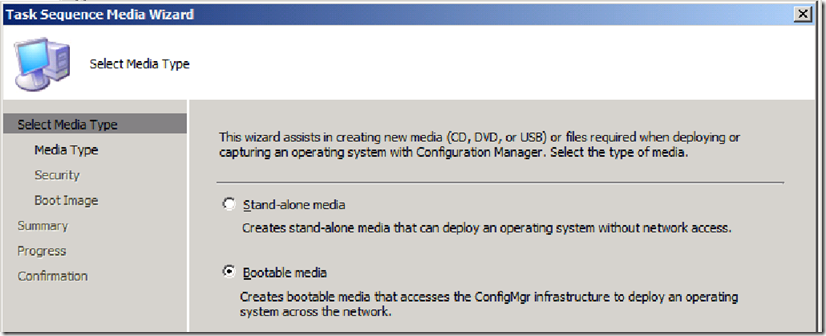
Here, I have a selected my task sequence and have selected Create Task Sequence Media and will create Bootable Media.
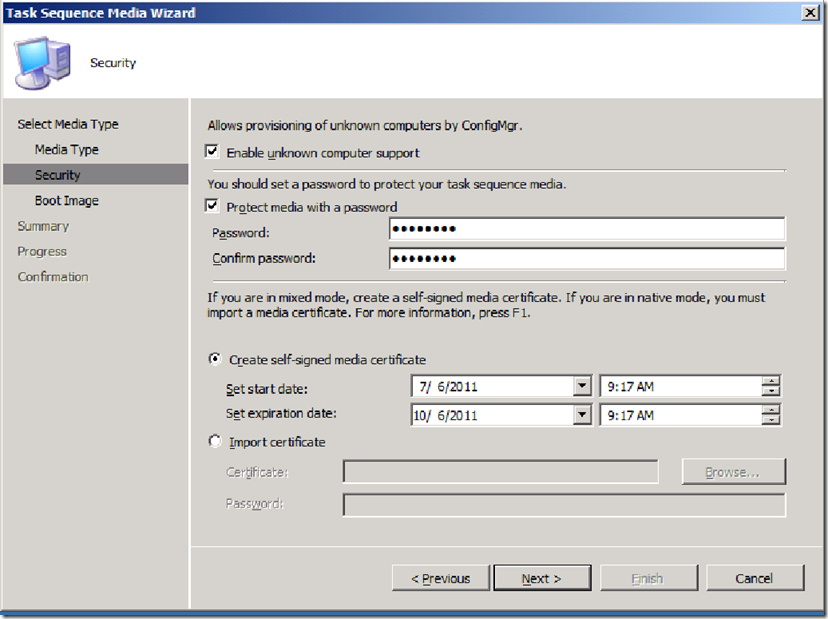
On the Security page of the Task Sequence Media Wizard, you will notice that Create self-signed media certificate is checked by default with a 1-year expiration date. However, since this fictional customer renews there boot images once a quarter, I have set the expiration date to 3 months in the future. I could also set a HARD date that may not be the full 3 months, but will end when the customer chooses to archive this particular boot image.
It is also important to note, that if you have a PKI infrastructure, you can import your own certificate.
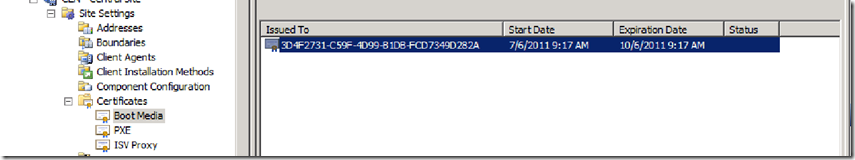
Once my media is created, you will notice the self-signed certificate now shows up under Site Settings>Certificates>Boot Media.
IMPORTANT: This is only visible/manageable from the site the bootable media is created from.
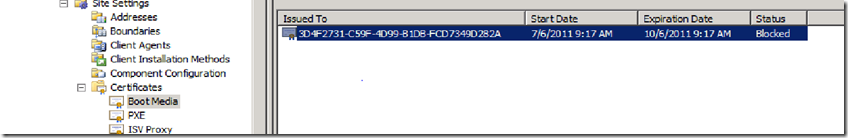
When I want to expire this boot media, I can highlight this certificate and choose ‘Block’. It is also important to note, that if the customer has a HARD date to expire all boot images, for example, on 09/01/2011, when a new one is released, we can select all of these certificates with a Start Date prior to 09/01/2011 and block them all at once.
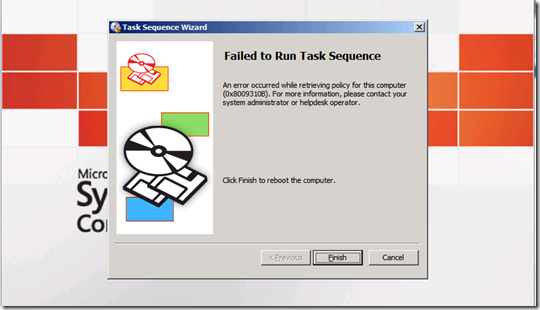
The next time this bootable media device is run, it will fail.
This post was contributed by Brad Tucker, a Senior Consultant with Microsoft Services, East Region, United States
Disclaimer: The information on this site is provided "AS IS" with no warranties, confers no rights, and is not supported by the authors or Microsoft Corporation. Use of included script samples are subject to the terms specified in the Terms of Use