Authorization Manager … Why not?
One of this days, when I was just talking with some of my colleagues we start wandering about Authorization mechanisms, and rapidly they evolved to all sort of techniques.
They talk about COM+ Roles, they talked about ASP.NET Roles, they talked about Passport Accounts, and they even talked about ADAM.
So after awhile I just said: “Hey, and what about Azman?”
Everyone just look at me, almost blank, and I was able to realize that there is a lot of ignorance about the AzMan.
This was a big surprise for me, since I always considered AzMan one of the most interesting mechanisms to implement Authorization. It’s easy to use, it’s reliable, it’s highly customizable and extensible and the performance is great.
So this time I decided to write a little about the Authorization Manager.
I rapidly realize that I don´t need to write a long a very technicall article about the AzMan, since there is a lot of that on the Internet, I would give some directions for that in the end of this article.
So, it was not a question of lack of technical information available that cause this strange obscurity about the AzMan.
Also, theres was not for lack of interest in the Microsoft, because the AzMan will have a major role in the Longhorn OS.
So I would say that mainly the Developer community does not know much about the AzMan because they can see the value for them in the AzMan.
So let’s try to do that
I’m a Developer, and this is what I need
Let’s start by saying what you, as a Developer, need.
If you ask me, I would say, that I need an Access control functionality for applications that is simple and secure.
I also need to improve the security of my products by ensuring proper integration with AD and windows security technologies.
And finally I absolutely need to reduce administrative management requirements for my software – e.g. improving their value proposition to clients
I would say that everyone will agree that those are obvious needs for all of us.
What about the scenarios that I usually have to face? Let’s think also a little about this.
Well, I have to protect access to Web-based, collaboration, and LOB applications (e.g. development team sites)
I also have to provide a secure, automated access for trusted groups, e.g. clinician access to patient healthcare data
Of course, I also have to provide audit records of who accessed what data and when.
Agree?
So after this where it goes the question that everyone is asking now … I hope:
What is Authorization Manager?
This is one is easy, you can use the Live Search and put that question in and you will get a lot of results answering.
For me, the answer is quite simple; Authorization Manager is roughly a component of Windows that provides an easy-to-use authorization framework for Web-based and line-of-business applications.
It provides role-based access control, e.g. the ability to control access to applications based on Active Directory group policy or another set of role-based permissions.
Visually is something like this
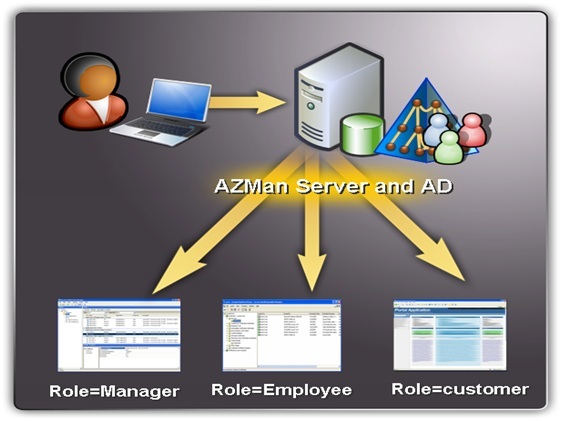
In terms of structure the primary components of the Authorization Manager are as follows:
· We have a role-based user interface, which determines end-user access based on user or group permissions in AD or SQL
· We have a management interface, which enables Administrators to configure access control for groups and individuals, manage roles, and view audit logs
· And we also have, of course, an enforcement functionality, which enables Administrators to enforce organizational policy rules.
So, what’s in there for me?
· With it, I now have a Simple Access Control Development Model.
It helps me reducing the software development costs by providing manageable, centralized administration and natural development model for my Web and line-of-business applications.
Also, it gives us the ability to define operations, tasks, roles, and business rules with a natural development model.
· Platform Services in Longhorn Reduce Development Scope
That’s true; AzMan will have a big presence in the new Longhorn Operating System.
· It will simplifies the Deployment, Configuration, and Management process for me
Through enabling a security policy based on a company's organizational structure and business rules by defining user roles
Through the ability to define operations, tasks, and roles using flexible authorization rules
By giving a centralized configuration and management it will help reduce the total cost of ownership
· Increases Security through Access Control
Now, the Access controls are based on security policy
The User identity is the basis for the access
The privileges are updated automatically as users change roles
How it works?
The concept in is essence is very simple, you are receiving a simplified development model for managing flexible groups, business rules, and store authorization policies.
The AzMan can though provide a role-based access control for applications, it determines user access based on Active Directory or SQL permissions.
You can also extend existing directory services with a simple access control model.
And finally, you can be easily integrated into most applications.
So I hope I was able to capture your interest and awake your curiosisty, if so, now you can dive on the technical details about the AzMan, and for that you will find a lot of resources, here it goes some of them.
Sia next time, jp.
Resources on the Web:
· Authorization Manager Blog
· Authorization Manager Developer Whitepaper
https://msdn2.microsoft.com/en-us/library/aa480244.aspx
· Authorization Manager Whitepaper
· Platform SDK Documentation
· DEV: Keith Brown MSDN Article (Sample included): Use Role-Based Security in Your Middle Tier .NET Apps with Authorization Manager
https://msdn.microsoft.com/msdnmag/issues/03/11/AuthorizationManager/
· Server Watch Tutorial: Exploring Windows 2003 Security: Authorization Manager
https://www.serverwatch.com/tutorials/article.php/3287431
· Authorize It - Use Role-Based Security in Your Middle Tier .NET Apps with Authorization Manager
https://msdn.microsoft.com/pt-pt/magazine/cc300469(en-us).aspx