RRAS Service fails to start on ISA Server 2006 when enabling RADIUS Authentication for VPN Users
Introduction
Consider a scenario where the ISA Server administrator has dial-in VPN correctly configured and working through ISA Server 2006. Now he needs to use RADIUS as the credentials authority and he makes the appropriate changes to the RADIUS configuration on the VPN settings as shown in Figures 1, 2 and 3:
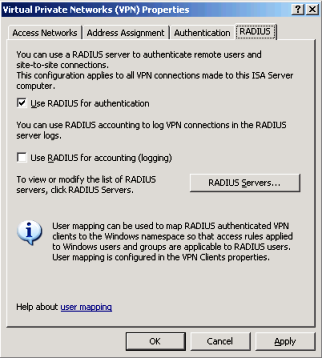
Figure 1 – RADIUS correctly enabled on ISA.
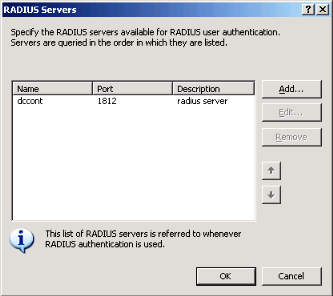
Figure 2 – RADIUS Server using the default authentication port.
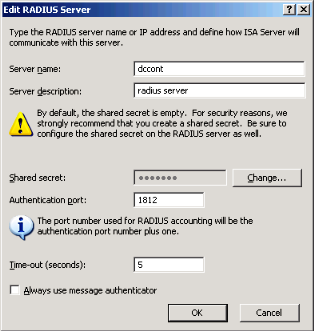
Figure 3 – RADIUS Server with the shared secret set.
After applying the changes, the RRAS service stops and the following event appears in Event Viewer when RRAS tries to restart:
Event Type: Error
Event Source: Microsoft Firewall
Event Category: None
Event ID: 21098
Date: 12/15/2009
Time: 4:16:46 PM
User: N/A
Computer: ISACONTN1
Description:
The RADIUS server list is empty. As a result, the Remote Access Service may fail to start.
Understanding the Behavior
Clearly the RADIUS server list is not empty as you can see in Figure 2 and 3. However if you observe other events in the event viewer you will see that the RADIUS server failure event is almost immediately preceded by this one:
Event Type: Warning
Event Source: Microsoft Firewall
Event Category: None
Event ID: 21301
Date: 12/15/2009
Time: 4:16:43 PM
User: N/A
Computer: ISACONTN1
Description:
The server name dccont cannot be resolved by DNS to a valid IP address.
Using Network Monitor during the moment of the failure, you can see that the Windows OS (where ISA server is installed) sends the DNS query for this name:
10.20.20.1 dccont.contoso.com DNS DNS:QueryId = 0xDE85, QUERY (Standard query), Query for dccontn1.contoso.com of type Host Addr on class Internet
The DNS Server reply with the following answer:
dnsrv.contoso.com 10.20.20.1 DNS DNS:QueryId = 0xDE85, QUERY (Standard query), Response - Name Error
What happens is that if ISA Server is not able to resolve the name of the RADIUS Server it can’t really proceed with this configuration because it has no credentials authority for the VPN client connections.
Common errors that can cause this are:
1. “dccont” was specified as an unqualified name (as shown in Figures 2 & 3). This leaves the server having to rely on the domain suffix devolution to resolve the name to an IP address. If the ISA has no domain suffix or the domain where the “dccont” RADIUS server registers its name is unknown to the ISA server or its DNS servers, the ISA server won’t resolve that name. You should always use fully-qualified names to avoid this behavior.
2. dccont.contoso.com is not known to the DNS server used by the ISA server. This may be due to an incorrect DNS configuration at the ISA server or the RADIUS server is not properly registered in DNS
3. DNS forwarding or recursion is failing at the DNS server used by the ISA server.
There are no doubt many other reasons for name resolution to fail at the chosen DNS server; you’ll just have to put on your Sherlock Holmes hat and get sleuthing.
Author
Yuri Diogenes
Sr Security Support Escalation Engineer
Microsoft CSS Forefront Edge Team
Technical Reviewer
Jim Harrison
Program Manager
Microsoft CSS Forefront Edge CS Team