HTTP to HTTPS redirects on IIS 7.x and higher
***Updated post on 8th May 2017***
This is the most common requirement on most of the Exchange servers hosted on IIS. The server admins configure an http to https redirect.
Today I will be discussing few ways of doing this. I will keep updating this document as I find more ways to do so. I am considering OWA as a sub application under IIS for all the below examples. Here is the structuring of the Web Site:
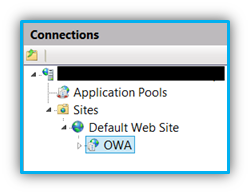
In this case, we want all the requests (both HTTP & HTTPS) to be redirected on HTTPS to the application called "OWA" under the Default Web Site.
Method 1: Using IIS URL Rewrite Module
For this you will have to install the URL Rewrite module. (FYI, this is available for IIS 7 and higher only.)
Download from here: https://www.iis.net/downloads/microsoft/url-rewrite
Once installed, the URL Rewrite module would be listed under IIS section. There are few articles out there on this. Here are few to list:
- https://www.sslshopper.com/iis7-redirect-http-to-https.html
- https://www.jppinto.com/2010/03/automatically-redirect-http-requests-to-https-on-iis7-using-url-rewrite-2-0/
These articles are definitely a great repository, however I observed that they have not addressed an important factor.
As specified in the above links add the below section in the web.config at the root of the site:
In the above rule I'm checking whether the server variable "SERVER_PORT_SECURE" is set to 1 or 0. (I'm doing a permanent redirect in the above URL, it can be changed accordingly as per the requirement)
If you want to include the query string in the re-written url, then you can add appendQueryString="true" under the action section.
You can find the complete list of IIS Server variables here: https://msdn.microsoft.com/en-us/library/ms524602(v=vs.90).aspx
SERVER_PORT_SECURE A string that contains either 0 or 1. If the request is being handled on the secure port, then this is 1. Otherwise, it is 0.
Alternatively, instead of the above server variable the following server variable "HTTPS" and "SERVER_PORT" can also be used correspondingly.
| NOTE: Ensure the rewrite rule is disabled at each of the virtual directories/applications under the Default Web Site. Due to inheritance, the rule will cause the requests to end up in infinite loop calling itself repeatedly. |

Method 2: Using IIS Default Document (a default.asp page)
In this method we will introduce a sample asp page at the root of the website and then add the following piece of code:
Alternatively you could use the port numbers in the above code to achieve the same (ensure to change the port numbers as per the website configuration).

Method 3: Using IIS HTTP Redirect Module
This is one of the simplest methods, but has a lot of limitations and ideally not used. Here is how we do it:
PRE-REQUISITES: HTTP Redirect module is installed and the website has a valid HTTPS binding in place.
Launch the IIS Manager.
Go to the HTTP Redirect module.
Fill the details as per the requirement as shown below:
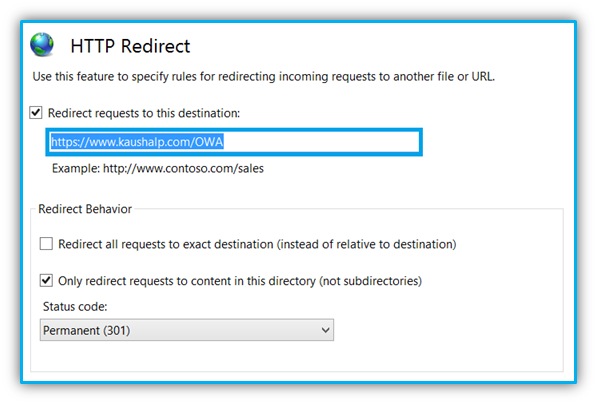
This may not be ideal for all the scenarios as the user is redirected to a specified URL.
| NOTE: Ensure the enforced redirection is removed from each of the virtual directories/applications under the Default Web Site. Due to inheritance, the requests will end up in an endless loop, redirecting to itself repeatedly.
Also ensure Require SSL is not checked at the Root of the website under SSL Settings, this may cause to throw an error page to the users when the browse the site over HTTP. It can be enforced at the application level. |

There is another way using custom error pages which has been documented here:
- https://www.sslshopper.com/iis7-redirect-http-to-https.html
- https://www.jppinto.com/2009/04/automatically-redirect-http-requests-to-https-iis-7/
The author in the 2nd link claims that it doesn't work on IIS 7.5 and higher versions due to updates in the configuration security.
I haven't found the time to test and write it up and neither am I sure if the above actually works. Once I have tested I will add it up here.