Leverage GRE Tunneling to enable the multi-tenant direct routing on Windows Server Gateway
Windows Server Gateway (WSG) is multi-tenant gateway but the forwarding gateway functionality is not which can only support one virutal network. That means if you want to enable direct routing for multiple virtual networks, you have to have equal number of dedicated HNV Gateway. That's not cost effiective for service provider.
As the paper "GRE Tunneling in Windows Server Technical Preview" mentioned Windows Server Threshold introduces a feature that enables a Generic Routing Encapsulation (GRE) tunnel capability for the Windows Server Gateway. GRE is a lightweight tunneling protocol that can encapsulate a wide variety of network layer protocols inside virtual point-to-point links over an Internet Protocol internetwork. GRE supports Multi-tenancy and can achieve up to 2.0Gbps throughput on a 6 core virtual machine. In additioni, many 3rd-party hardware and software network appliance can support GRE (RFC 2890).
Now Windows Server 2012 R2 can also support GRE tunneling by install the hofix KB3022776. The hotfix is not public available. You need to open a case to CTS and request the hotfix https://support.microsoft.com/en-us/kb/3022776 .
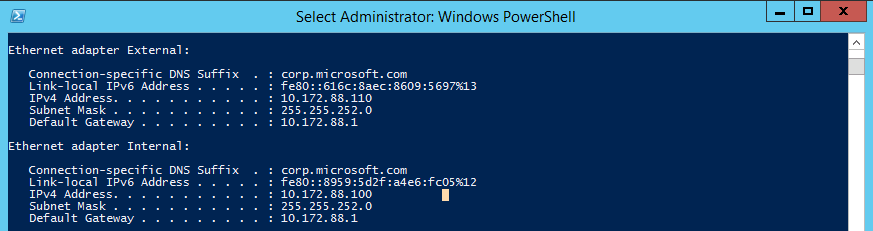
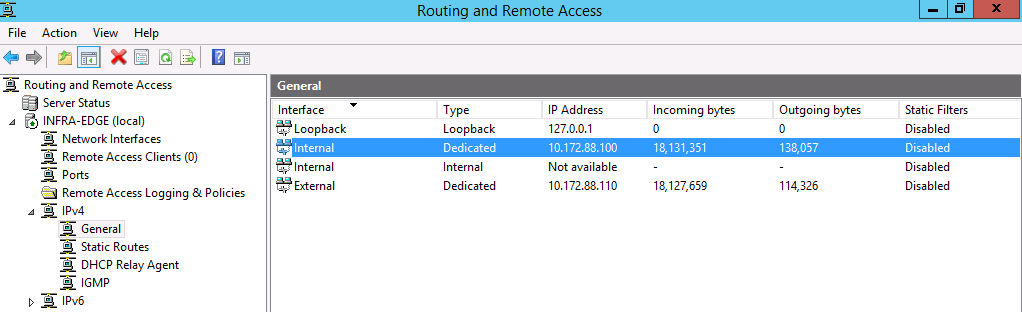
In the following test, I have a Windows Server 2012 R2 RRAS VM, which has two NICs. Both of the NICs connect to the same physical network.
I configured RRAS and used one of the NICs as the external. The other was configured as internal.
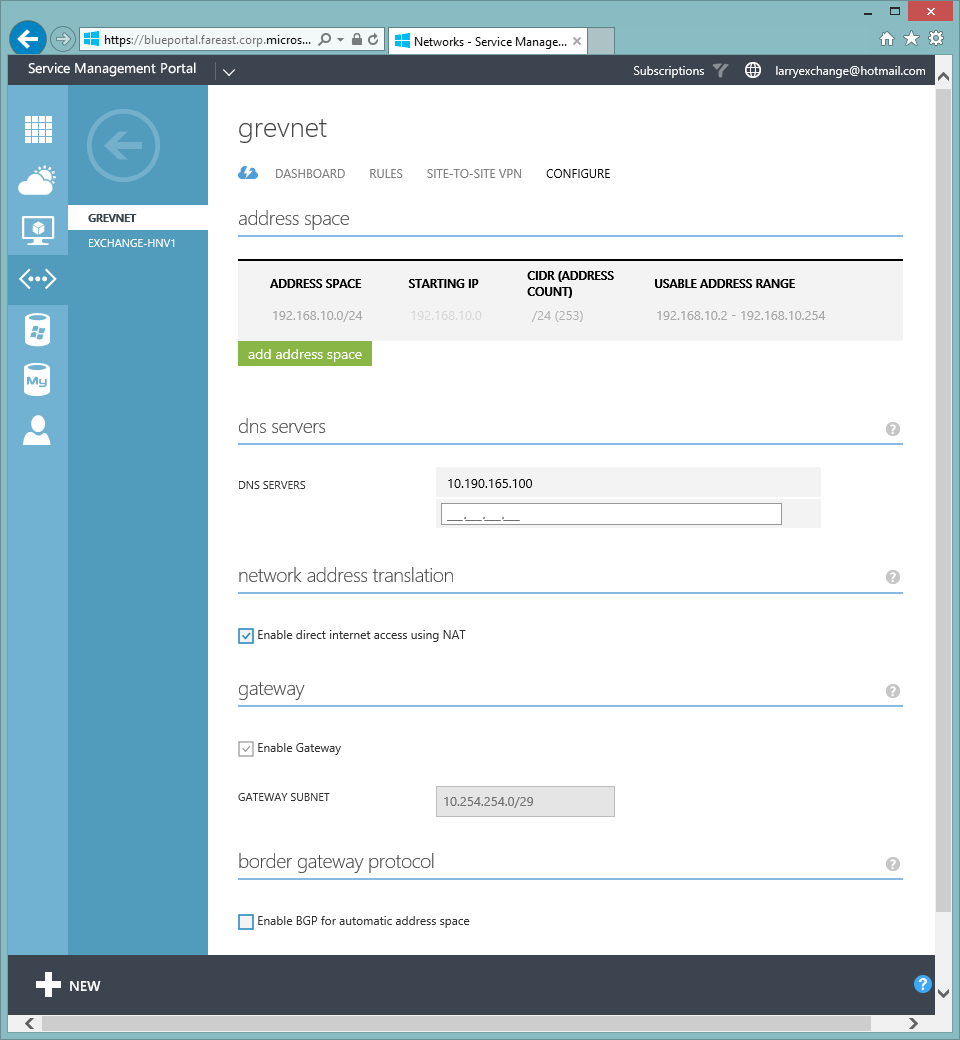
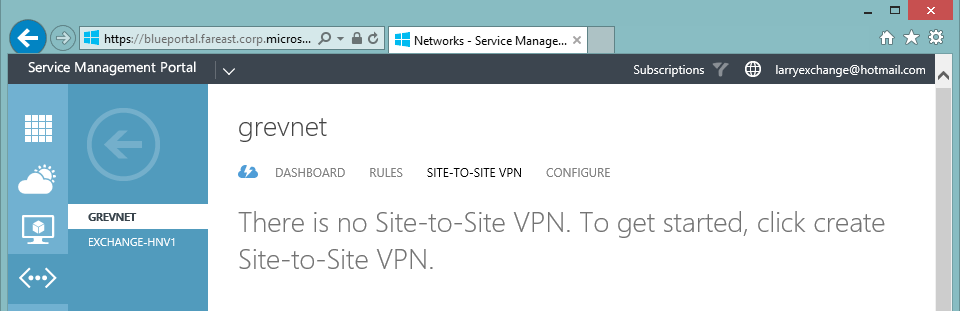
I have Windows Azure Pack Vritual Network, I didn't create S2S VPN gateway from WAP portal.
After installing hotfix KB3022776 on both WSG (Service Provider's multi-tenant HNV Gateway) and the new RRAS (Service Provider's GRE dedicated VM), I can configure GRE VPN now.
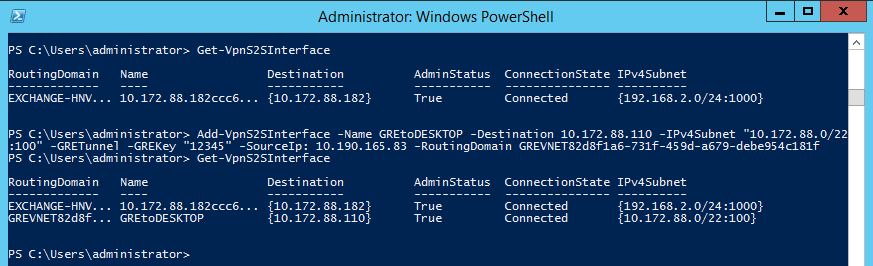
On WSG, I run the cmdlet:
Add-VpnS2SInterface -Name GREtoDESKTOP -Destination 10.172.88.110 -IPv4Subnet "10.172.88.0/22:100" -GRETunnel -GREKey "12345" -SourceIp: 10.190.165.83 -RoutingDomain GREVNET82d8f1a6-731f-459d-a679-debe954c181f
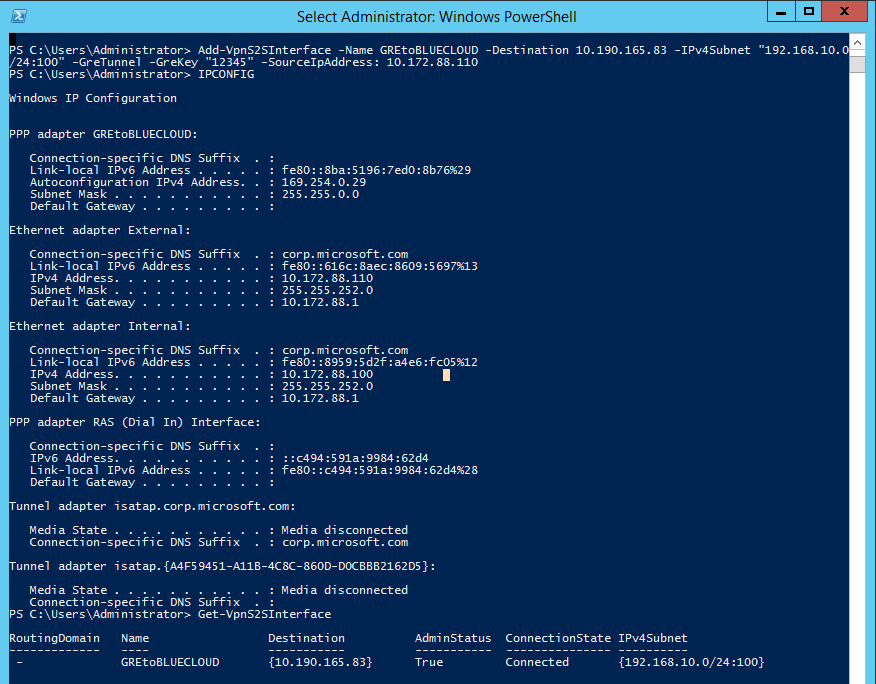
On RRAS, I run the cmdlet:
Add-VpnS2SInterface -Name GREtoBLUECLOUD -Destination 10.190.165.83 -IPv4Subnet "192.168.10.0/24:100" -GreTunnel -GreKey "12345" -SourceIpAddress: 10.172.88.110
Using cmdlet "Get-VpnS2SInterface" I could see the GRE VPN connection was already connected.
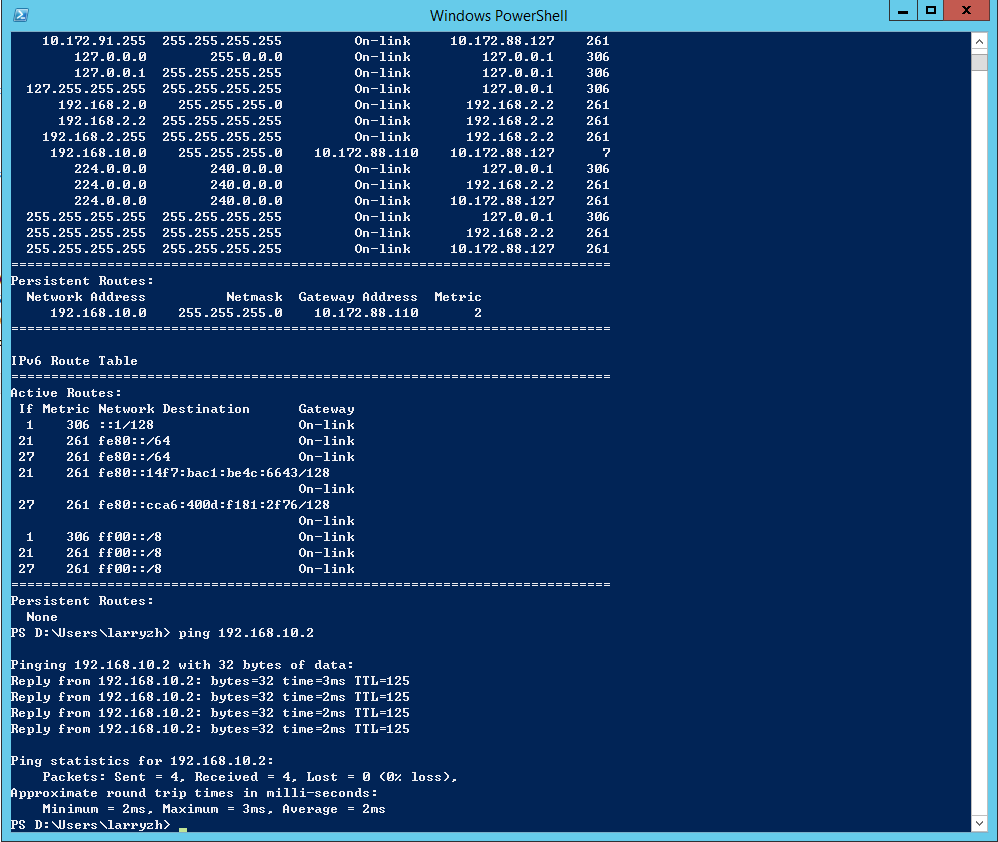
After adding a static routing in physical network "10.172.88.0/22", the VMs in virtual network 192.168.10.0/24 and physical network are connected each other.