Monitoring machines using Certificates with System Center Operations Manager 2007 R2 - Part 1
(Post courtesy Rohit Kochher)
In this series of two blogs, we will discuss about monitoring machines in non-trusted domain. In part one we will discuss about scenarios to use certificates and configuring certificate template for Operations Manager. In part two, we will talk about installation, approval of gateway servers and configuring monitoring for Workgroup machines.
Kerberos or Certificates
System Center Operations Manager 2007 R2 uses mutual authentication to communicate with agents. This can be done using Kerberos v5 or certificates. In case the monitored computers are in the same domain as that of Operations Manager server, or if the two domains have a two way trust we can use Kerberos. But if you want to monitor machines in a workgroup or in a non-trusted/one way trusted domain we need certificates. Certificates help in Mutual authentication.
The following blog post from the Operations Manager support team has a nice diagram that shows where you would use Kerberos vs. certificates for authentication: Step by Step for using Certificates to communicate between agents and the OpsMgr 2007 server.
Scenarios to used Certificates
If my Operations Manager server is in domain A and I want to monitor machines which are in a workgroup, I need to use certificates. I will install certificates on my Operations Manager server and on each workgroup machine that I want to monitor.
If my Operations Manager server is in domain A and I want to monitor machines in untrusted domain B, I will use certificates along with a gateway server. But this time I don’t need to install certificates on all machines in domain B. I can simply install the Gateway Server in domain B and have certificates installed on the Operations Manager server of domain A and the Gateway Server of domain B. Within Domain B, Kerberos is the security mechanism between the agents and the Gateway server. Between the Gateway and Operations Manager servers, certificates are used to provide mutual authentication.
Another benefit of gateway servers is that I need to open only 1 port 5723 (TCP) between the Gateway and Operations Manager servers.
We will also need name resolution between the Operations Manager server and gateway server. This can be done using DNS, host files etc.
Let’s get it Started
I have installed Active Directory Certificate Services (AD CS) and Certificate Authority Web Enrollment roles on 2008 R2. Certificate Authority is of Enterprise type. More on 2008 R2 CA can be found here. Also to configure HTTPS binding for CA, check this article.
Configuring certificate template for SCOM
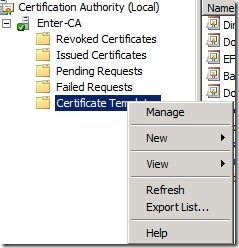
1) On 2008 R2 Server, Click Start, then Administrative Tools and open Certification Authority snap-in. Click on Certificate templates, then on Manage.
2) Right Click on IPSec (offline request) template and select Duplicate Template option.
Select Windows Server 2003 Enterprise option for the version.
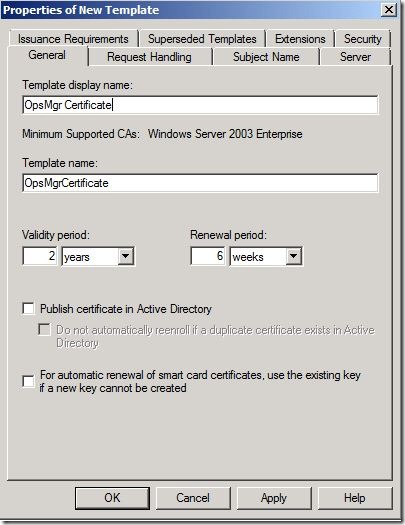
3) In Properties of new Template on General tab, give any name to template like OpsMgr Certificate using Template Display Name.
4) On request handling tab check Allow private key to be exported.
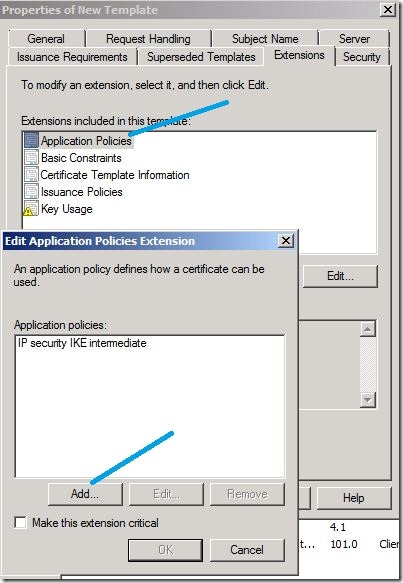
5) Click the Extensions tab, and in Extensions included in this template, click Application Policies, and then click Edit. In the Edit Application Policies Extension dialog box, click IP security IKE intermediate, and then click Remove.
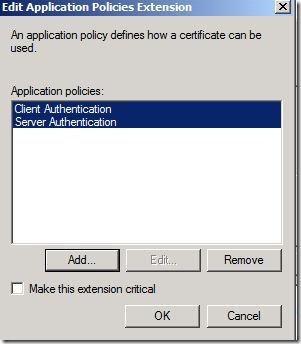
6) Click Add and then select Client Authentication and Server Authentication and click OK.
7) Click on Security tab and give Authenticated users Read and Enroll permissions.
8) Close the Certificate templates console.
Add the configured templates to certificate templates folder
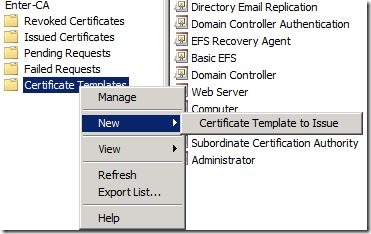
Right click Certificate templates in CA console. Click on New and then Certificate template to issue. Select the certificate template that we named in step 3.
This way we configure our certificate for SCOM. In part 2 we will discuss about installation of certificates and deployment of gateway server.
Stay Tuned!!
Additional Resources