People Picker doesn’t resolve users and groups from Azure Active Directory (AAD) / Grant access to SharePoint 2013 sites using AAD groups
This post talks about how to grant permissions to SharePoint 2013 sites based on AAD groups and why the out-of-the-box people picker functionality doesn’t resolve users and groups from Windows Azure Active Directory
You can integrate SharePoint with Windows Azure Active Directory (https://technet.microsoft.com/en-us/library/dn635311(v=office.15).aspx) to grant access to users from AAD to SharePoint 2013 sites.
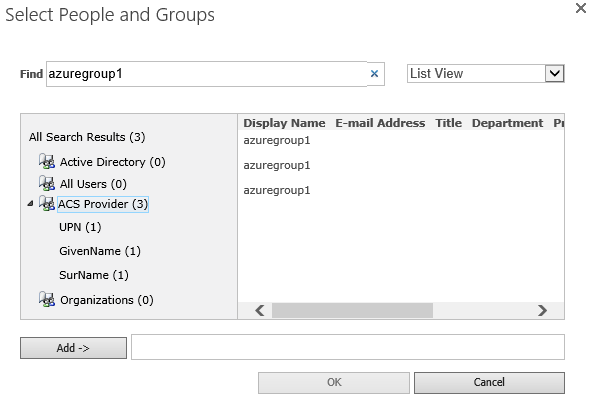
Now what happens if you want to grant access to the AAD users using AAD groups? …the security groups will not be resolved in SharePoint. In fact, in the people picker control, you get results for any search string entered, but SharePoint does not validate the user input. Any input is validated as is against each claim type configured (whatever the user types). This is not specific to AAD, or AAD groups.
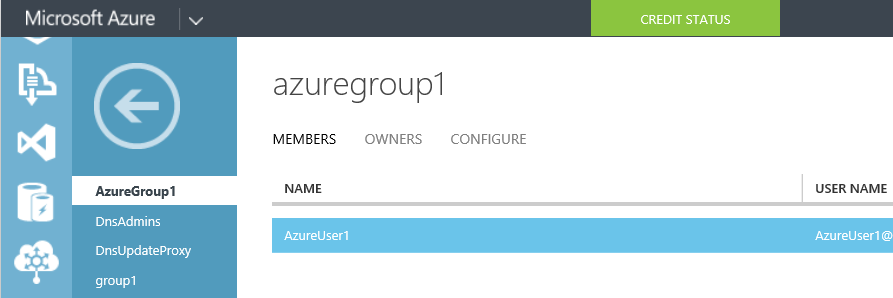
AAD group:
People Picker Control:
Why can we not grant permissions in SharePoint 2013 sites to groups from Azure Active Directory (AAD)?
There is a good reason behind it. When a user authenticates, AAD does not include his group membership in the SAML token received by SharePoint, so SharePoint does not know to which groups the user belongs to, thus cannot make authorizations based on groups.
Ok ok.. so now that we know the reason behind it,
How do we make it work?
We have to implement a custom claims provider ( https://msdn.microsoft.com/en-us/library/office/ee535894(v=office.15).aspx ) that will get the AAD groups of the user and add them to his SAML token, which will allow SharePoint to process authorization on groups.
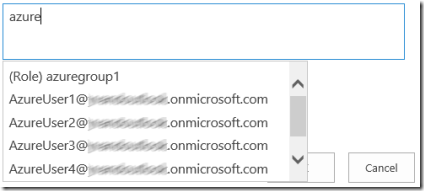
Another benefit of using a custom claims provider is that it adds search capabilities to the people picker, so when a user uses people picker to grant a permission, he gets actual users and groups from AAD.
Project https://azurecp.codeplex.com implements what I describe above. Credits to the developer of the project who supported me also in writing this blog article!