Part 3 - Protecting NDES with Web Application Proxy (WAP) in the DMZ
As you might have learned from my previous blog post about certificate deployment to mobile devices via NDES it’s mandatory to open port 443 (TCP) from any IP on the internet inbound to your NDES server. At the same time the NDES server needs to be domain joined to the same domain as your Certificate Authority/ConfigMgr Server and Domain Controllers.
The NDES server could either be placed in your trusted zone next to your CA/ConfigMgr server/DC’s OR in the DMZ with a large amount of firewall exceptions required for a typical domain joined server.
Some of our customers don’t prefer or allow such type of configuration and require a reverse proxy in front of the NDES server, preferably non-domain joined and in the DMZ.
Your reverse proxy is likely to block large GET requests
The interesting part is when a mobile device on the internet receives a certificate profile from Microsoft Intune, this profile includes an URL to the NDES server. From that point on the device will reach out to the NDES server with a massive GET request (including a challenge to secure any known SCEP vulnerabilities) – depending on your configured key length it can be up to 30kb or even 40kb. Many reverse proxy solutions do not allow such large URL’s to be accepted, including UAG or Web Application Proxy (WAP). In my experience the only working solution is TMG however that product is discontinued and no longer recommended.
The good news
The good news is that we have been working on a fix to address this issue. As of today there is an hotfix that mitigates the maximum GET request size restriction in our Web Application Proxy solution. This hotfix is private for now, this means it’s not tested extensively and therefore comes with limited support. Because of that it’s not publically available without contacting Microsoft support, more information will be published at a later timeframe. In the future a KB will be posted that describes this issue and fix (KB523052).
Update: the hotfix is now generally available and part of the December Windows Update. Read more details in this post.
Design Overview
From a design perspective this is what it could look like:
Please do no note that Web Application Proxy is built on top of http.sys which has a similar restriction, however that restriction can be changed by altering the registry.
Open the registry editor on your Web Application Server and add the following two registry keys:
Location: HKLM\SYSTEM\CurrentControlSet\Services\HTTP\Parameters
Value: MaxFieldLength
Type DWORD
Data: 65534 (decimal)Location: HKLM\SYSTEM\CurrentControlSet\Services\HTTP\Parameters
Value: MaxRequestBytes
Type DWORD
Data: 65534 (decimal)
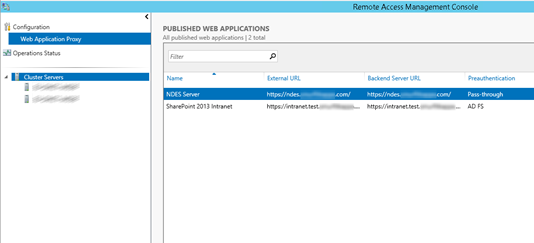
Publishing the NDES server using the Remote Access Management Console on the WAP is fairly straight forward:
After changing the registry, applying the hotfix and rebooting your server, mobile devices should be able to request a certificate via the (workgroup) WAP from the NDES server. If the devices fails to receive a certificate, please refer to the troubleshooting section in my previous blog post regarding Windows Intune and NDES.
I hope this guide helps you secure NDES using Microsoft Technology (Web Application Proxy). If it helped, please consider leaving a reply.
Regards,
Pieter