IE Process mode gives https://event popup
Note: Blog updated with the latest information.
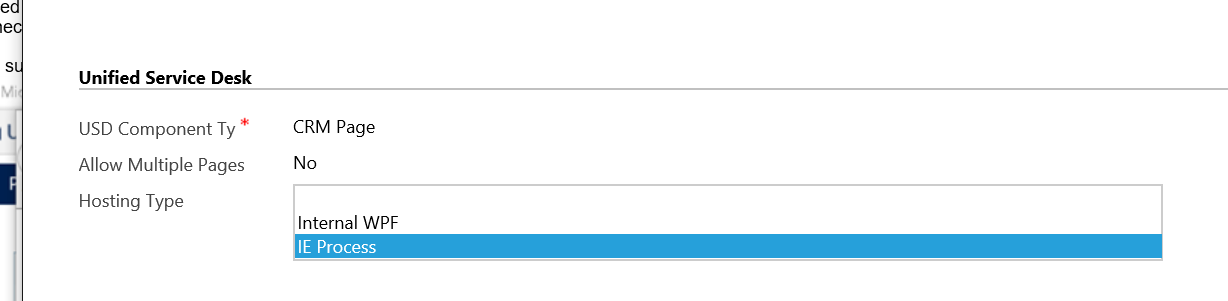
Most Unified Service Desk customers today utilize the Internal WPF setting for CRM Pages and Standard Web Applications but there are distinct tradeoffs when using this setting in that it utilizes the WPF WebBrowser control for hosting URLs and there are some rendering differences between it and standard Internet Explorer. Another important point about the WebBrowser control is that all the memory that would normally sit in an IExplore.exe process, now lives inside your UnifiedServiceDesk.exe process. This has the effect of making it appear as though Unified Service Desk utilizes a lot more memory than it actually does. There is another way to host the browser built into USD 2.0, however, and that is called IE Process mode. Generally the guidance is to make sure that a specific web application (such as CRM) utilize only Internal WPF hosted controls or only IE Process hosted controls. This is because they are treated as separate sessions and use of both may cause an additional authentication step to be required that would otherwise be unnecessary.
So, suppose you decide you want to take advantage of the IE Process setting and so you switch your CRM hosted controls to utilize this setting. One thing you might notice right away are some https://event popups appearing with no content all over the place.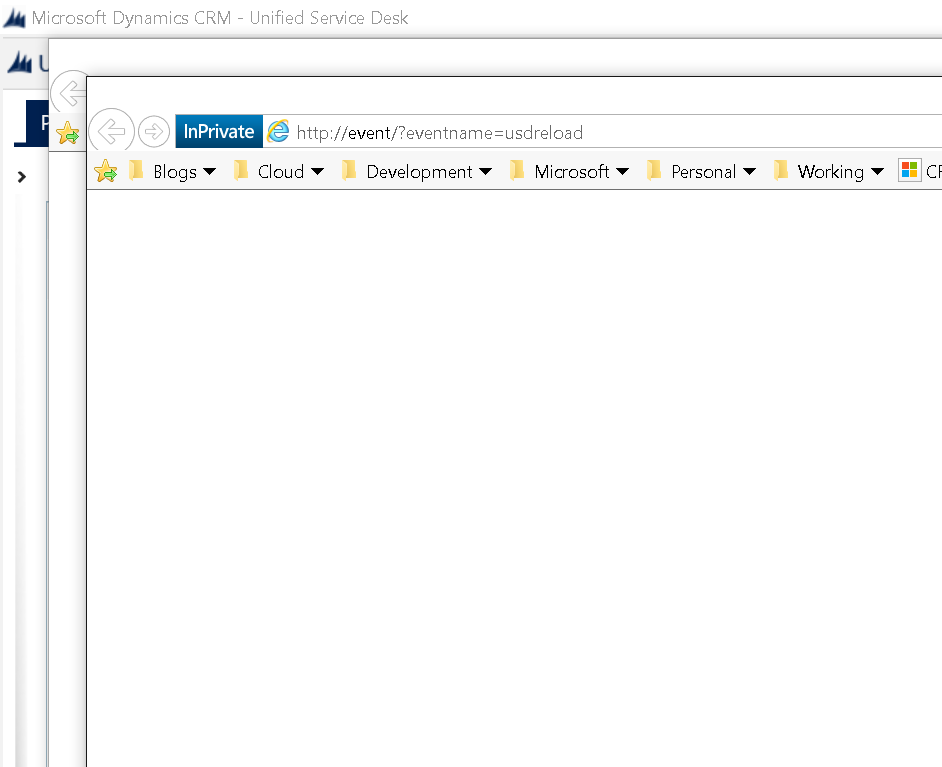
These popups are part of a mechanism that Unified Service Desk (USD) uses to communicate command and content from a web page back to USD for processing. This happens because when these popups occur in IE 11, it checks the security zone of the popup, and if the security zone the URL lives within happens to be in a zone where protected mode is NOT set , IE will not notify the hosting application about the event and will not allow USD to act on it. This URL happens to live in the Intranet zone by default, which also happens to have protected mode off by default.
In Internet Properties, by default, the four Security zones will have the following settings.
| Zones | Enable Protected Mode |
|---|---|
| Internet | Checkbox selected |
| Intranet | Checkbox not selected |
| Trusted sites | Checkbox not selected |
| Restricted sites | Checkbox selected |
There are two ways you can address the issue:
1. Enable Protected Mode for Intranet (Recommended way)
To enable the option using Internet options:
- Open Internet Explorer.
- Select Tools > Internet Options > Security tab.
- Select a zone to change the security settings.
Following are the zones:- Internet
- Local intranet
- Trusted sites
- Restricted sites
- Select the Enable Protected Mode check box for the intranet zone. If you have URLs in trusted sites that you use in USD then enable protected mode there as well.
- Select Apply, and then select OK.
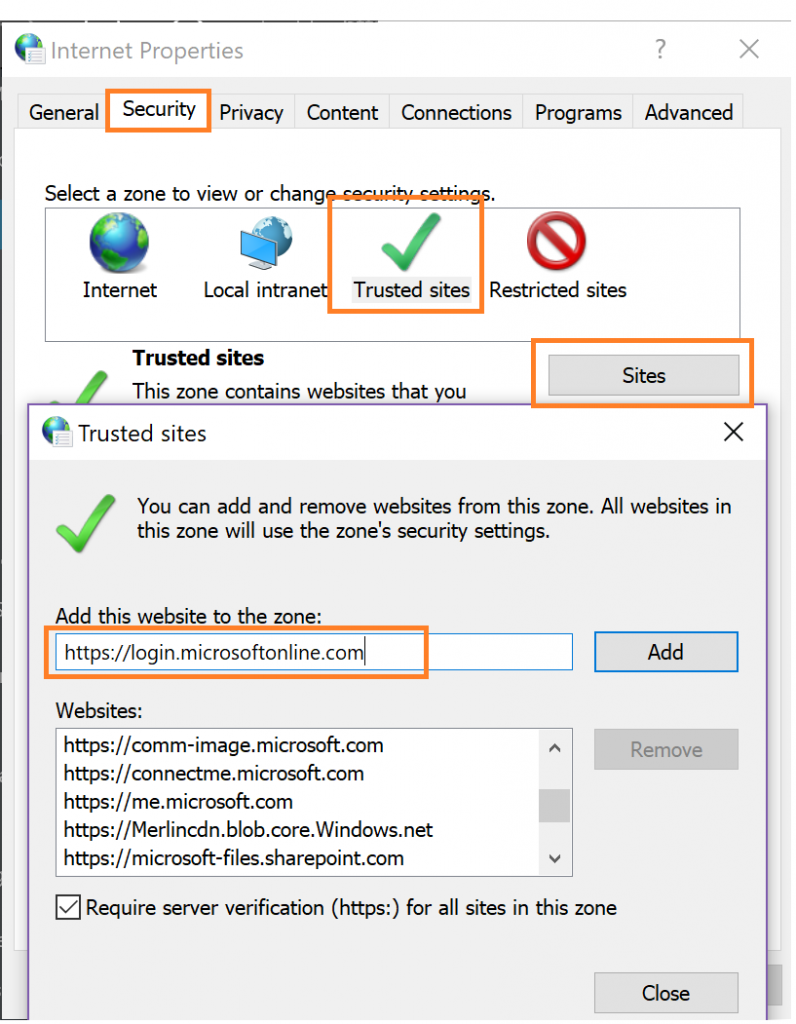
2. Add the URLs to the Trusted sites zone in Internet Properties.
Without changing the above mentioned default settings, add the URLs to the Trusted sites. To add the URLs, follow the steps:
- Go to Control Panel > Internet Options > Security tab.
- Select Trusted sites.
- Select Sites.
- In the Add this website to the zone field, add the Dynamics 365 instance and authentication URLs, and select Add. For example:
- https://*.dynamics.com
- https://login.microsoftonline.com
- Select Close, and then again select Apply.
Note: If you have an actual intranet application that pops windows that you want to control with USD, you must similarly ensure that you also add the Trusted sites zone.
Warning: There may be many redirection URLs and you may need to handle them as well. Some users have reported issues in single sign on across different sites when using this setting. We recommend that you opt for this only in the case when you cannot enable protected mode for your intranet zones and have tested your end to end scenarios thoroughly with line of business applications.
Now, if you restart the Internet Explorer and try opening the USD, the https://event popups won't appear.
Read more about the recommended Internet Explorer settings here (/en-us/dynamics365/customer-engagement/unified-service-desk/admin/internet-explorer-settings-bpa )
(This blog was originally authored by Jayme Pechan, and later updated by Kumar Ashutosh and Karthik Balasubramanian)