Security assessment: Riskiest lateral movement paths (LMP)
This articled describes the Riskiest lateral movement paths (LMP) security posture assessment report, available in Microsoft Secure Score.
What are Risky lateral movement paths?
Microsoft Defender for Identity continuously monitors your environment to identify sensitive accounts with the riskiest lateral movement paths that expose a security risk, and reports on these accounts to assist you in managing your environment. Paths are considered risky if they have three or more non-sensitive accounts that can expose the sensitive account to credential theft by malicious actors.
Learn more about LMP:
- Understand and investigate Lateral Movement Paths (LMPs) with Microsoft Defender for Identity
- MITRE ATT&CK Lateral Movement
What risk do risky lateral movement paths pose?
Organizations that fail to secure their sensitive accounts leave the door unlocked for malicious actors.
Malicious actors, much like thieves, often look for the easiest and quietest way into any environment. Sensitive accounts with risky lateral movement paths are windows of opportunities for attackers and can expose risks.
For example, the riskiest paths are more readily visible to attackers and, if compromised, can give an attacker access to your organization's most sensitive entities.
How do I use this security assessment?
Review the recommended action at https://security.microsoft.com/securescore?viewid=actions to discover which of your sensitive accounts have risky LMPs.
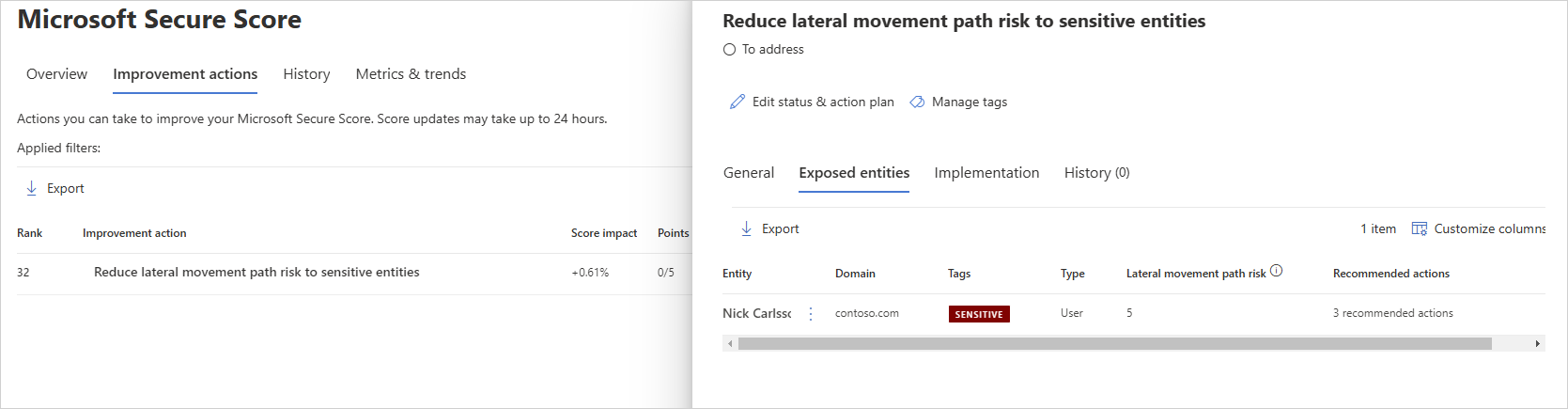
Take appropriate action:
- Remove the entity from the group as specified in the recommendation.
- Remove the local administrator permissions for the entity from the device specified in the recommendation.
Note
While assessments are updated in near real time, scores and statuses are updated every 24 hours. While the list of impacted entities is updated within a few minutes of your implementing the recommendations, the status may still take time until it's marked as Completed.
See Also
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for