General installation
How can I harden my Microsoft Entra Connect server to decrease the security attack surface?
Microsoft recommends hardening your Microsoft Entra Connect server to decrease the security attack surface for this critical component of your IT environment. Following these recommendations decreases the security risks to your organization.
- Deploy Microsoft Entra Connect on a domain joined server and restrict administrative access to domain administrators or other tightly controlled security groups.
To learn more, see:
Does the installation work if the Microsoft Entra Global Administrator has two-factor authentication (2FA) enabled?
As of the February 2016 builds, this scenario is supported.
Is there a way to install Microsoft Entra Connect unattended?
Microsoft Entra Connect installation is supported only when you use the installation wizard. An unattended, silent installation isn't supported.
I have a forest where one domain can't be contacted. How do I install Microsoft Entra Connect?
As of the February 2016 builds, this scenario is supported.
Does the Microsoft Entra Domain Services health agent work on server core?
Yes. After you install the agent, you can complete the registration process by using the following PowerShell cmdlet:
Register-AzureADConnectHealthADDSAgent -Credentials $cred
Does Microsoft Entra Connect support syncing from two domains to a Microsoft Entra ID?
Yes, this scenario is supported. Refer to Multiple Domains.
Can you have multiple connectors for the same Active Directory domain in Microsoft Entra Connect?
No, multiple connectors for the same AD domain aren't supported.
Can I move the Microsoft Entra Connect database from the local database to a remote SQL Server instance?
Yes, the following steps provide general guidance on how to do this move. For more information, see Move Microsoft Entra Connect database from SQL Server Express to remote SQL Server
Back up the LocalDB ADSync database. The simplest way to make this backup is to use SQL Server Management Studio installed on the same machine as Microsoft Entra Connect. Connect to (LocalDb).\ADSync, and then back up the ADSync database.
Restore the ADSync database to your remote SQL Server instance.
Install Microsoft Entra Connect against the existing remote SQL database. The article demonstrates how to migrate to using a local SQL database. If you're migrating to using a remote SQL database, in step 5 of the process you must also enter an existing service account that the Windows ADSync service uses. This sync engine service account is described here:
Use an existing service account: By default, Microsoft Entra Connect uses a virtual service account for the synchronization services to use. For remote SQL Server instance or web proxy with authentication, use a managed service account or a service account in the domain. In those cases, enter the account to use. Make sure that users who are running the installation are system administrators in SQL so that login credentials for the service account can be created. For more information, see Microsoft Entra Connect accounts and permissions.
With the latest build, the SQL administrator can provision the database and grant the Microsoft Entra Connect administrator with database owner rights to install the product. For more information, see Install Microsoft Entra Connect by using SQL delegated administrator permissions.
To keep things simple, we recommend the users who install Microsoft Entra Connectto have system administrator rights in SQL. However, with recent builds you can now use delegated SQL administrators, as described in Install Microsoft Entra Connect using SQL delegated administrator permissions.
What are some of the best practices from the field?
The following is an informational document that presents some of the best practices that engineering, support, and our consultants have developed over the years. This is presented in a bullet list that can be quickly referenced. Although this list attempts to be comprehensive, there may be other best practices that might be added to the list in the future.
- If using Full SQL then it should remain local vs. remote:
- Fewer hops
- Easier to troubleshoot
- Less complexity
- Need to designate resources to SQL and allow overhead for Microsoft Entra Connect and OS.
- Bypass the web proxy if possible, otherwise ensure that the web proxy timeout value is greater than 5 minutes.
- If a web proxy is required, then you must add the web proxy configuration to the machine.config file.
- Be aware of local SQL jobs and maintenance and how they'll impact Microsoft Entra Connect - particularly re-indexing.
- Ensure that DNS can resolve names externally.
- Ensure that server specifications are per recommendation whether you're using physical or virtual servers.
- Ensure that if you're using a virtual server that resources required are dedicated.
- Ensure that you have the disk and disk configuration meet Best Practices for SQL Server.
- Install and configure Microsoft Entra Connect Health for monitoring.
- Use the export deletion threshold that is built into Microsoft Entra Connect to prevent accidental deletes.
- Carefully review release updates to be prepared for all changes and new attributes that may be added.
- Backup everything:
- Backup Keys
- Backup Synchronization Rules
- Backup Server Configuration
- Backup SQL Database
- Avoid using Azure Backup for the ADSync database as it may lead to deadlocks and potentially cause the run profile to freeze.
- Ensure that there are no 3rd party backup agents that are backing up SQL without the SQL VSS Writer (common in virtual servers with 3rd party snapshots).
- Limit the number of custom synchronization rules that are used as they add complexity.
- Treat Microsoft Entra Connect Servers as Tier 0 Servers.
- Be leery of modifying cloud synchronization rules without great understanding of the impact and the right business drivers.
- Make sure that the correct URLs and Firewall ports are open for support of Microsoft Entra Connect and Microsoft Entra Connect Health.
- Leverage the cloud filtered attribute to troubleshoot and prevent phantom objects.
- With the Staging Server ensure that you're using the Microsoft Entra Connect Configuration Documenter tool for consistency between servers.
- Staging Servers should be in separate datacenters (Physical Locations.
- Staging servers aren't meant to be a High Availability solution, but you can have multiple staging servers.
- Introducing a "Lag" Staging Servers could mitigate some potential downtime in case of an issue.
- Test and Validate all upgrades on the Staging Server first.
- Always validate exports before switching over to the staging server. Leverage the staging server for Full Imports and Full Synchronizations to reduce business impact.
- Keep version consistency between Microsoft Entra Connect Servers as much as possible.
Can I allow Microsoft Entra Connect to create the Microsoft Entra Connector account on Workgroup machine?
No, in order to allow Microsoft Entra Connect to auto-create the Microsoft Entra Connector account, the machine must be domain-joined.
Network
I have a firewall, network device, or something else that limits the time that connections can stay open on my network. What should my client-side timeout threshold be when I use Microsoft Entra Connect?
All networking software, physical devices, or anything else that limits the maximum time that connections can remain open should use a threshold of at least five minutes (300 seconds) for connectivity between the server where the Microsoft Entra Connect client is installed and Microsoft Entra ID. This recommendation also applies to all previously released Microsoft Identity synchronization tools.
Are single label domains (SLDs) supported?
While we strongly recommend against this network configuration (see article), using Microsoft Entra Connect Sync with a single label domain is supported, as long as the network configuration for the single level domain is functioning correctly. In SLD scenarios where the Active Directory NetBIOS domain name differs from the FQDN domain name, it's unsupported to install Microsoft Entra Connect.
Are Forests with disjoint AD domains supported?
No, Microsoft Entra Connect doesn't support on-premises forests that contain disjoint namespaces.
Are "dotted" NetBIOS names supported?
No, Microsoft Entra Connect doesn't support on-premises forests or domains where the NetBIOS name contains a dot (.).
Is pure IPv6 environment supported?
No, Microsoft Entra Connect doesn't support a pure IPv6 environment.
I have a multi-forest environment and the network between the two forests is using NAT (Network Address Translation). Is using Microsoft Entra Connect between these two forests supported?
No, using Microsoft Entra Connect over NAT isn't supported.
Federation
What do I do if I receive an email that asks me to renew my Microsoft 365 certificate?
For guidance about renewing the certificate, see renew certificates.
I have "Automatically update relying party" set for the Microsoft 365 relying party. Do I have to take any action when my token signing certificate automatically rolls over?
Use the guidance that's outlined in the article renew certificates.
Environment
Is it supported to rename the server after Microsoft Entra Connect has been installed?
No. Changing the server name renders the sync engine unable to connect to the SQL database instance, and the service can't start.
Are Next Generation Cryptographic (NGC) sync rules supported on a FIPS-enabled machine?
No. They aren't supported.
If I disabled a synced device in the [Microsoft Entra admin center](https://entra.microsoft.com), why it's re-enabled?
Synced devices might be authored or managed on-premises. If a synced device is enabled on premises, it might be re-enabled in the Microsoft Entra admin center even if was previously disabled by an administrator. To disable a synced device, use the on-premises Active Directory to disable the computer account.
If I block user sign-in at the Microsoft 365 or [Microsoft Entra admin center](https://entra.microsoft.com) for synced users, why it's unblocked upon signing in again?
Synced users might be authored or managed on-premises. If the account is enabled on premises, it can unblock the sign-in block placed by administrator.
Identity data
Why doesn't the userPrincipalName (UPN) attribute in Microsoft Entra ID match the on-premises UPN?
For information, see these articles:
- Usernames in Microsoft 365, Azure, or Intune don't match the on-premises UPN or alternate login ID
- Changes aren't synced by the Azure Active Directory sync tool after you change the UPN of a user account to use a different federated domain
You can also configure Microsoft Entra ID to allow the sync engine to update the UPN, as described in Microsoft Entra Connect Sync service features.
Is it supported to soft-match an on-premises Microsoft Entra group or contact object with an existing Microsoft Entra group or contact object?
Yes, this soft match is based on the proxyAddress. Soft matching isn't supported for groups that aren't mail-enabled.
Is it supported to manually set the ImmutableId attribute on an existing Microsoft Entra group or contact object to hard-match it to an on-premises Microsoft Entra group or contact object?
No, manually setting the ImmutableId attribute on an existing Microsoft Entra group or contact object to hard-match it's currently not supported.
Custom configuration
Where are the PowerShell cmdlets for Microsoft Entra Connect documented?
With the exception of the cmdlets that are documented on this site, other PowerShell cmdlets found in Microsoft Entra Connect aren't supported for customer use.
Can I use the "Server export/server import" option that's found in Synchronization Service Manager to move the configuration between servers?
No. This option doesn't retrieve all configuration settings, and it shouldn't be used. Instead, use the wizard to create the base configuration on the second server, and use the sync rule editor to generate PowerShell scripts to move any custom rule between servers. For more information, see Swing migration.
Can passwords be cached for the Azure sign-in page, and can this caching be prevented because it contains a password input element with the autocomplete = "false" attribute?
Currently, modifying the HTML attributes of the Password field, including the autocomplete tag, isn't supported. We're currently working on a feature that allows for custom JavaScript, which lets you add any attribute to the Password field.
The Azure sign-in page displays the usernames of users who have previously signed in successfully. Can this behavior be turned off?
Currently, modifying the HTML attributes of the Password input field, including the autocomplete tag, isn't supported. We're currently working on a feature that allows for custom JavaScript, which lets you add any attribute to the Password field.
Is there a way to prevent concurrent sessions?
No.
autoupgrade
What are the advantages and consequences of using autoupgrade?
We're advising all customers to enable autoupgrade for their Microsoft Entra Connect installation. The benefit's that you always receive the latest patches, including security updates for vulnerabilities that have been found in Microsoft Entra Connect. The upgrade process is painless and happens automatically as soon as a new version is available. Many thousands of Microsoft Entra Connect customers use autoupgrade with every new release.
The autoupgrade process always first establishes whether an installation is eligible for autoupgrade. If it's eligible, the upgrade is performed and tested. The process also includes looking for custom changes to rules and specific environmental factors. If the tests show that an upgrade is unsuccessful, the previous version is automatically restored.
Depending on the size of the environment, the process can take a couple of hours. While the upgrade is in progress, no sync between Windows Server Active Directory and Microsoft Entra ID happens.
I received an email telling me that my autoupgrade no longer works and I need to install a new version. Why do I need to do this?
Last year, we released a version of Microsoft Entra Connect that, under certain circumstances, might have disabled the autoupgrade feature on your server. We have fixed the issue in Microsoft Entra Connect version 1.1.750.0. If you have been affected by the issue, you can mitigate it by running a PowerShell script to repair it or by manually upgrading to the latest version of Microsoft Entra Connect.
To run the PowerShell script, download the script and run it on your Microsoft Entra Connect server in an administrative PowerShell window. To learn how to run the script, view this short video.
To manually upgrade, you must download and run the latest version of the AADConnect.msi file.
- If your current version is older than 1.1.750.0, download and upgrade to the latest version.
- If your Microsoft Entra Connect version is 1.1.750.0 or later, no further action is required. You’re already using the version that contains the autoupgrade fix.
I received an email telling me to upgrade to the latest version to re-enable autoupgrade. I'm using version 1.1.654.0. Do I need to upgrade?
Yes, you need to upgrade to version 1.1.750.0 or later to re-enable autoupgrade. Download and upgrade to the latest version.
I received an email telling me to upgrade to the latest version to re-enable autoupgrade. If I have used PowerShell to enable autoupgrade, do I still need to install the latest version?
Yes, you still need to upgrade to version 1.1.750.0 or later. Enabling the autoupgrade service with PowerShell doesn't mitigate the autoupgrade issue found in versions before 1.1.750.0.
I want to upgrade to a newer version but I’m not sure who installed Microsoft Entra Connect, and we don't have the username and password. Do we need this?
You don’t need to know the username and password that was initially used to upgrade Microsoft Entra Connect. Use any Microsoft Entra account that has the Global Administrator role.
How can I find which version of Microsoft Entra Connect I'm using?
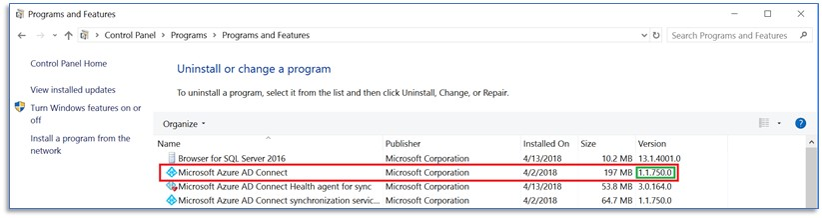
To verify which version of Microsoft Entra Connect is installed on your server, go to Control Panel and look up the installed version of Microsoft Entra Connect by selecting Programs > Programs and Features, as shown here:
How do I upgrade to the latest version of Microsoft Entra Connect?
To learn how to upgrade to the latest version, see Microsoft Entra Connect: Upgrade from a previous version to the latest.
We already upgraded to the latest version of Microsoft Entra Connect last year. Do we need to upgrade again?
The Microsoft Entra Connect team makes frequent updates to the service. To benefit from bug fixes and security updates as well as new features, it's important to keep your server up to date with the latest version. If you enable autoupgrade, your software version is updated automatically. To find the version release history of Microsoft Entra Connect, see Microsoft Entra Connect: Version release history.
How long does it take to perform the upgrade, and what is the impact on my users?
The time needed to upgrade depends on your tenant size. For larger organizations, it might be best to perform the upgrade in the evening or weekend. During the upgrade, no synchronization activity takes place.
I believe I upgraded to Microsoft Entra Connect, but the Office portal still mentions DirSync. Why is this?
The Office team is working to get the Office portal updates to reflect the current product name. It doesn't reflect which sync tool you're using.
My autoupgrade status says, “Suspended." Why is it suspended? Should I enable it?
A bug was introduced in a previous version that, under certain circumstances, leaves the autoupgrade status set to “Suspended.” Manually enabling it's technically possible but would require several complex steps. The best thing you can do is install the latest version of Microsoft Entra Connect.
My company has strict change-management requirements, and I want to control when it’s pushed out. Can I control when autoupgrade is launched?
No, there's no such feature today. The feature is being evaluated for a future release.
Will I get an email if the autoupgrade failed? How will I know that it was successful?
You won't be notified of the result of the upgrade. The feature is being evaluated for a future release.
Do you publish a timeline for when you plan to push out autoupgrades?
autoupgrade is the first step in the release process of a newer version. Whenever there's a new release, upgrades are pushed automatically. Newer versions of Microsoft Entra Connect are pre-announced in the Microsoft Entra Roadmap.
Does autoupgrade also upgrades Microsoft Entra Connect Health?
Yes, autoupgrade also upgrades Microsoft Entra Connect Health.
Do you also autoupgrade Microsoft Entra Connect servers in staging mode?
Yes, you can autoupgrade a Microsoft Entra Connect server that is in staging mode.
If autoupgrade fails and my Microsoft Entra Connect server doesn't start, what should I do?
In rare cases, the Microsoft Entra Connect service doesn't start after you perform the upgrade. In these cases, rebooting the server usually fixes the issue. If the Microsoft Entra Connect service still doesn't start, open a support ticket. For more information, see Create a service request to contact Microsoft 365 support.
I’m not sure what the risks are when I upgrade to a newer version of Microsoft Entra Connect. Can you call me to help me with the upgrade?
If you need help with upgrading to a newer version of Microsoft Entra Connect, open a support ticket at Create a service request to contact Microsoft 365 support.
Operational best practice
Below are some best practices you should implement when syncing between Windows Server Active Directory and Microsoft Entra ID.
Apply Multi-Factor Authentication for all synced accounts Microsoft Entra multifactor authentication helps safeguard access to data and applications while maintaining simplicity for users. It provides additional security by requiring a second form of authentication and delivers strong authentication via a range of easy to use authentication methods. Users may or may not be challenged for MFA based on configuration decisions that an administrator makes. You can read more about MFA here: https://www.microsoft.com/security/business/identity/mfa?rtc=1
Follow the Microsoft Entra Connect server security guidelines The Microsoft Entra Connect server contains critical identity data and should be treated as a Tier 0 component as documented in the Active Directory administrative tier model. Please also refer to our guidelines for securing your Microsoft Entra Connect server.
Enable PHS for leaked credentials detection Password Hash Sync also enables leaked credential detection for your hybrid accounts. Microsoft works alongside dark web researchers and law enforcement agencies to find publicly available username/password pairs. If any of these pairs match those of your users, the associated account is moved to high risk.
Troubleshooting
How can I get help with Microsoft Entra Connect?
Search the Microsoft Knowledge Base (KB)
- Search the KB for technical solutions to common break-fix issues about support for Microsoft Entra Connect.
Microsoft Q&A question page for Microsoft Entra ID
- Search for technical questions and answers or ask your own questions by going to the Microsoft Entra community.
Why am I seeing Events 6311 and 6401 occur after Sync Step Errors?
The events 6311 - The server encountered an unexpected error while performing a callback and 6401 - The management agent controller encountered an unexpected error - are always logged after a synchronization step error. To resolve these errors, you need to clean up the synchronization step errors. For more information, see Troubleshooting errors during synchronization and Troubleshoot object synchronization with Microsoft Entra Connect Sync